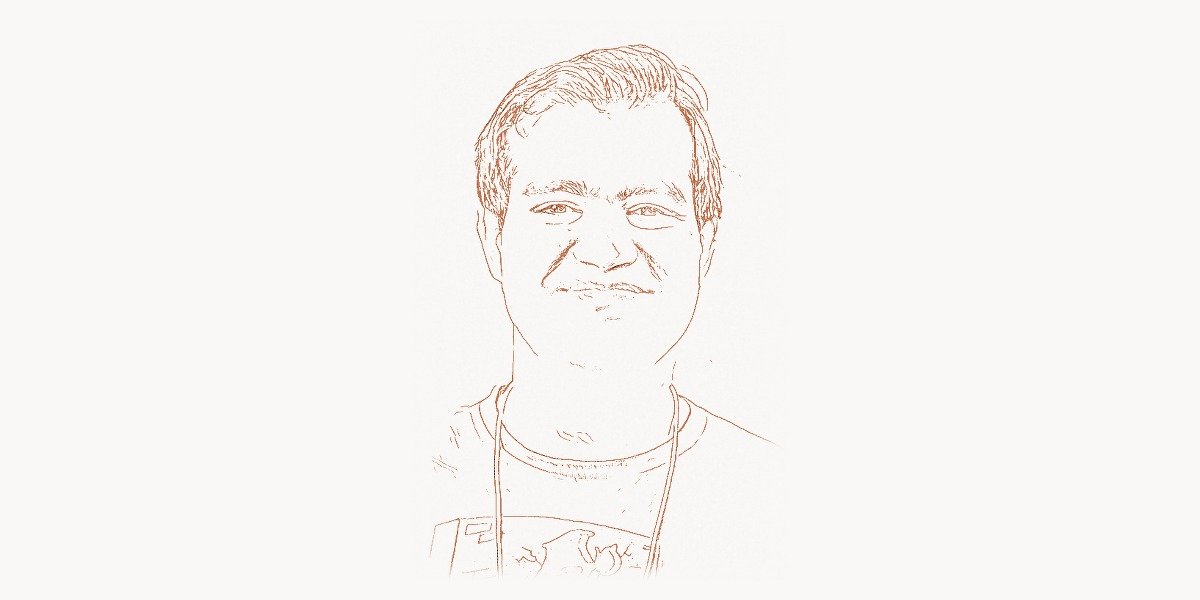
In the summer of 2008, one man held a secret that could have unraveled the entire internet. Dan Kaminsky, a 29-year-old security researcher with a reputation for finding bugs that others considered theoretical, had discovered a fundamental flaw in the Domain Name System — the protocol that translates every human-readable web address into the numerical IP addresses that computers actually use. The vulnerability was not a bug in one vendor’s software. It was a design flaw in DNS itself, meaning that virtually every nameserver on the planet was affected. If exploited, an attacker could redirect any domain name to any IP address, silently rerouting bank websites to phishing servers, email to surveillance systems, software updates to malware distributors. Kaminsky did something remarkable: instead of publishing the exploit for fame or selling it for profit, he spent months coordinating a secret, industry-wide patch before disclosing the details. It was the largest synchronized security fix in internet history, and it cemented Kaminsky’s place as one of the most important figures in cybersecurity. When he died in April 2021 at the age of 42, the security community lost not just a brilliant researcher but a moral compass — someone who consistently argued that security exists to protect people, not to control them.
Early Life and Education
Dan Kaminsky was born on February 7, 1979, in San Francisco, California. He grew up in a household where curiosity was encouraged, and he discovered computers early. By the age of five, Kaminsky was already tinkering with the family’s home computer, fascinated by the logic of how software worked. His childhood coincided with the personal computing revolution of the 1980s, and like many future security researchers, he was drawn not just to what computers could do, but to the boundaries of what they were supposed to do — the edges where systems behaved in unexpected ways.
Kaminsky’s aptitude for finding unexpected behaviors manifested early. At age eleven, he accidentally triggered a security alert at his family’s internet service provider by systematically scanning their network — not out of malice, but out of pure curiosity about how the network was structured. The incident, which temporarily cut off his family’s internet access, was a formative moment. It taught him that digital exploration had real consequences and that the boundaries between investigation and intrusion were thinner than most people realized.
He attended Santa Clara University, where he studied computer science and deepened his understanding of networking protocols. But Kaminsky’s real education happened outside the classroom. He immersed himself in the hacker community of the late 1990s — not the criminal underground, but the research-oriented community that gathered at conferences like DEF CON and Black Hat to share knowledge about how systems actually worked versus how they were supposed to work. This community valued intellectual honesty, creative problem-solving, and a deep commitment to understanding systems at the protocol level. Kaminsky thrived in it. By the time he graduated, he was already a known figure in security circles, recognized for his deep understanding of network protocols and his ability to find vulnerabilities that others had overlooked for years.
After university, Kaminsky worked at several security firms, including Cisco and Avaya, where he focused on network security analysis. He quickly earned a reputation as someone who could see patterns in network traffic that were invisible to conventional tools. His early work on DNS analysis tools and network auditing laid the groundwork for the discovery that would define his career. Kaminsky approached security the way Bruce Schneier approached cryptography — by questioning the fundamental assumptions that everyone else took for granted.
The DNS Cache Poisoning Breakthrough
In early 2008, while conducting routine research on DNS behavior, Kaminsky stumbled onto something that made his blood run cold. He had found a way to reliably poison DNS caches — to inject false records into the nameservers that virtually every internet user depended on for translating domain names into IP addresses. What made his discovery catastrophic was not just that it worked, but that it worked against every major DNS implementation simultaneously, and it could be executed in seconds rather than the hours or days that previous theoretical cache poisoning attacks required.
Technical Innovation
To understand why Kaminsky’s discovery was so devastating, you need to understand how DNS resolution works. When you type a URL into your browser, your computer asks a recursive DNS resolver for the corresponding IP address. If the resolver does not have the answer cached, it queries authoritative nameservers in a hierarchical chain — starting from the root servers, then the top-level domain servers (.com, .org, etc.), then the domain’s own authoritative servers. The response is then cached for a period defined by the record’s Time to Live (TTL) value, so future queries for the same domain are answered from cache without repeating the full lookup.
The security of this process rested on a fragile mechanism: transaction IDs. Each DNS query included a 16-bit transaction ID, and the resolver would only accept a response that matched the transaction ID of the outstanding query. Since there were 65,536 possible transaction IDs, an attacker who wanted to inject a forged response would need to guess the correct ID before the legitimate response arrived. Previous cache poisoning research had shown this was theoretically possible but practically difficult — you had to race against the legitimate server, and if you lost the race, the cached legitimate answer would block further attempts until the TTL expired, which could be hours or days.
Kaminsky’s insight was elegant and terrifying. Instead of querying for a domain that already existed in cache (like www.example.com), he queried for random, nonexistent subdomains (like abc123.example.com). Since these subdomains had never been queried before, there was no cached answer to block the attack. Each query for a new random subdomain opened a fresh race window. The attacker could flood the resolver with hundreds of queries per second, each for a different nonexistent subdomain, simultaneously sending forged responses with guessed transaction IDs. The forged responses included not just an answer for the nonexistent subdomain, but — critically — a delegation record that redirected the resolver’s cache for the entire parent domain to an attacker-controlled nameserver.
The following example demonstrates the conceptual structure of how DNS resolution works and where the cache poisoning vulnerability existed. This is a simplified educational model — not an exploit:
"""
DNS Resolution Model — Educational demonstration of the
transaction ID vulnerability that Dan Kaminsky discovered.
This illustrates WHY the 16-bit transaction ID was insufficient
and how querying random subdomains bypassed cache protections.
"""
import random
import hashlib
class SimplifiedDNSResolver:
"""
Model of a pre-patch DNS resolver showing the structural
vulnerability Kaminsky identified in 2008.
"""
def __init__(self):
self.cache = {} # domain -> (ip_address, ttl_expiry)
self.pending_queries = {} # txn_id -> queried_domain
def generate_transaction_id(self):
"""
Pre-2008 resolvers used a 16-bit transaction ID.
Only 65,536 possible values — Kaminsky showed this
was far too small a keyspace to resist brute-force
when an attacker could open unlimited race windows.
"""
return random.randint(0, 65535) # 16-bit space
def send_query(self, domain):
"""Simulate sending a DNS query."""
txn_id = self.generate_transaction_id()
self.pending_queries[txn_id] = domain
return txn_id
def receive_response(self, txn_id, domain, ip_address):
"""
Accept a response only if the transaction ID matches.
THE VULNERABILITY: With only 65,536 possible IDs,
an attacker sending floods of guessed responses
has a high probability of matching within seconds.
"""
if txn_id in self.pending_queries:
if self.pending_queries[txn_id] == domain:
self.cache[domain] = ip_address
del self.pending_queries[txn_id]
return True
return False
def is_cached(self, domain):
return domain in self.cache
def demonstrate_kaminsky_insight():
"""
Kaminsky's key insight: query RANDOM subdomains to
bypass the cache protection that blocked earlier attacks.
Old attack: query www.bank.com → if you lose the race,
the legitimate answer is cached and blocks retries
for hours (until TTL expires).
Kaminsky attack: query random1.bank.com, random2.bank.com,
random3.bank.com... Each is a NEW query with a fresh
race window. You get unlimited attempts per second.
"""
resolver = SimplifiedDNSResolver()
target_domain = "bank.com"
# Old attack: one chance, then blocked by cache
old_attack_queries = ["www.bank.com"] # Just one shot
# Kaminsky attack: unlimited fresh chances
kaminsky_queries = [
f"{hashlib.md5(str(i).encode()).hexdigest()[:8]}.{target_domain}"
for i in range(1000) # Thousands of unique subdomains
]
# Each generates a new pending query with a guessable 16-bit txn_id
# Forged responses include NS delegation for the parent domain
# Probability of guessing at least one txn_id correctly:
# With 1000 attempts × ~100 guesses each = 100,000 total guesses
# Against a 65,536-value space → near-certain success
attempts_per_subdomain = 100
total_guesses = len(kaminsky_queries) * attempts_per_subdomain
probability = 1 - ((65535 / 65536) ** total_guesses)
return f"Success probability: {probability:.6f}" # ≈ 1.0
print(demonstrate_kaminsky_insight())This was the breakthrough: by turning a single-chance attack into an unlimited-attempts attack, Kaminsky had reduced DNS cache poisoning from a theoretical concern to a practical, reliable exploit. The 16-bit transaction ID space, which had been considered adequate protection for decades, was suddenly revealed as catastrophically insufficient when an attacker could make thousands of independent guessing attempts per second.
Why It Mattered
DNS is not just one protocol among many — it is the foundation on which virtually all internet communication is built. Every web request, every email delivery, every API call, every software update check begins with a DNS lookup. If an attacker could control DNS responses, they could redirect any internet traffic to any destination without the user having any visible indication that something was wrong. The browser would still show the correct URL in the address bar. The connection might even use HTTPS — but if the attacker controlled the DNS response, they could direct the initial connection to their own server and attempt to intercept or manipulate it.
The implications were staggering. Banking websites could be silently redirected to perfect phishing replicas. Email could be rerouted through surveillance servers. Software update mechanisms — which many operating systems and applications rely on — could be hijacked to deliver malware instead of legitimate patches. Corporate VPN connections could be redirected to attacker-controlled endpoints. The attack was universal, invisible, and devastating.
Kaminsky understood immediately that he could not simply publish the vulnerability. Unlike a bug in a single vendor’s software, this affected every DNS implementation on the internet. There was no one organization that could fix it. He made the decision to coordinate a secret, multi-vendor patch effort — something that had never been attempted at this scale. In March 2008, Kaminsky contacted Paul Vixie, the author of BIND (the most widely deployed DNS software), and together they organized a secret meeting at Microsoft’s campus that included engineers from Cisco, Sun Microsystems, and other major technology companies. The participants were sworn to secrecy while patches were developed simultaneously across all major DNS implementations.
On July 8, 2008, the coordinated disclosure went public. Patches were released simultaneously by every major DNS vendor — Microsoft, BIND, Cisco, Nominum, and others. The patches implemented source port randomization, which expanded the effective keyspace an attacker would need to guess from 16 bits (65,536 values) to approximately 32 bits (over 4 billion values) by randomizing the UDP source port of DNS queries in addition to the transaction ID. It was the largest coordinated security patch in internet history, and it worked because Kaminsky chose responsibility over glory. The coordination model Kaminsky established anticipated the kind of structured vulnerability management that modern development platforms like Toimi now facilitate as standard practice in software teams.
The disclosure was not without drama. Two weeks before Kaminsky’s planned full disclosure at Black Hat 2008, the security researcher Halvar Flake independently deduced the attack technique from the limited details in the advisory and published it. The exploit was then accidentally leaked in full by the Matasano Security blog, forcing the security community into emergency mode. Despite this, the coordinated patching had given the internet a critical two-week head start, and the majority of major resolvers had already been patched by the time the full details became public.
Other Contributions
While the DNS discovery was Kaminsky’s most famous work, it represented only one chapter in a career filled with significant contributions to internet security. His research consistently focused on the gap between how protocols were supposed to work and how they actually behaved in practice — a perspective shaped by the foundational internet architecture designed by pioneers like Vint Cerf.
Kaminsky was an early and influential researcher on the security implications of NAT (Network Address Translation) traversal techniques. He developed tools and techniques for understanding how firewalls and NAT devices affected network security, work that was particularly relevant as the internet moved from a model where every device had a public IP address to one where most devices sat behind NAT gateways. His research revealed that many assumptions about network security boundaries were invalid in a NAT-heavy world.
He made significant contributions to the analysis of rootkits and malware, developing forensic tools that could detect the presence of sophisticated system-level compromises. His approach to malware analysis was characteristically creative — instead of focusing on signature-based detection, he looked for anomalies in system behavior that indicated something was wrong at a fundamental level. This anomaly-detection philosophy influenced a generation of security tools.
Kaminsky also conducted important research on the security of SSL/TLS certificates, the foundation of web encryption. He identified weaknesses in how certificate authorities validated domain ownership and how browsers processed certificate chains. This work contributed to the broader push for certificate transparency and improved validation practices that eventually led to initiatives like Let’s Encrypt, which made HTTPS certificates freely available and helped encrypt the majority of web traffic — building on the cryptographic foundations that researchers like Phil Zimmermann had fought to make publicly accessible.
In his later years, Kaminsky turned his attention to improving internet infrastructure at a fundamental level. He worked on projects to improve the security of BGP (Border Gateway Protocol), the routing protocol that determines how traffic flows between networks on the internet. BGP has many of the same structural vulnerabilities as pre-patch DNS — it relies on trust between network operators without strong cryptographic verification. Kaminsky advocated for DNSSEC (DNS Security Extensions) and RPKI (Resource Public Key Infrastructure) as necessary upgrades to internet infrastructure, even though he was realistic about the deployment challenges these technologies faced.
He also explored the intersection of security and usability, arguing that security tools that were difficult to use were effectively no security at all. He built tools designed to make security analysis accessible to a broader audience, including visual network analysis tools that could represent complex protocol interactions in intuitive ways. This philosophy of making security accessible echoed the work of Moxie Marlinspike, who applied similar thinking to encrypted messaging — recognizing that the best cryptography in the world is useless if ordinary people cannot use it.
Kaminsky was also a passionate advocate for DNSSEC adoption and spent considerable effort developing tools and educational materials to help network administrators deploy it. He understood that while source port randomization had mitigated the immediate threat of his 2008 discovery, it was fundamentally a band-aid — a probabilistic defense that increased the cost of attack without eliminating the underlying vulnerability. Only cryptographic authentication of DNS responses, as provided by DNSSEC, could truly solve the problem. This perspective — that temporary mitigations must not become permanent substitutes for proper fixes — was one of his most important contributions to security thinking.
Philosophy and Principles
Kaminsky’s technical brilliance was matched by a deeply considered philosophy about the role of security research in society. He was one of the most articulate voices in the cybersecurity community on questions of ethics, responsibility, and the purpose of security work. His views were shaped by his experience with the DNS vulnerability — the moment when he held a secret capable of disrupting the global internet and had to decide what to do with it.
Key Principles
Security exists to protect people, not systems. Kaminsky consistently argued that the purpose of cybersecurity was not to protect abstract systems or corporate assets, but to protect the people who depended on those systems. This perspective shaped his approach to vulnerability disclosure — he chose coordinated disclosure for the DNS flaw not because he was concerned about the DNS protocol in the abstract, but because billions of people depended on it working correctly. He extended this principle to his advocacy for internet accessibility, arguing that security measures that excluded people from using the internet were themselves a form of harm.
Complexity is the enemy of security. Kaminsky was a vocal critic of unnecessarily complex systems, arguing that every additional layer of complexity created new attack surface. He advocated for simple, well-understood protocols and implementations, and was skeptical of security solutions that added complexity in the name of protection. This aligned with the foundational principles of the web itself — the simplicity and openness that Tim Berners-Lee built into the web’s original architecture was, in Kaminsky’s view, a security feature as much as a usability one.
Responsible disclosure is a moral obligation. Kaminsky believed that security researchers who discovered serious vulnerabilities had a moral duty to ensure those vulnerabilities were fixed before they could be exploited. He was critical of both full disclosure extremists (who published exploits immediately with no coordination) and of researchers who sold vulnerabilities to governments or criminal organizations. He argued for a middle path — coordinated disclosure that gave vendors time to patch while ensuring that the public was eventually informed. His handling of the DNS vulnerability became the gold standard for responsible disclosure in the security community.
The internet is critical infrastructure that belongs to everyone. Kaminsky was deeply committed to the idea that the internet was a shared resource — not owned by governments or corporations but belonging to all of humanity. He opposed efforts to fragment or control the internet, whether through government censorship, corporate walled gardens, or surveillance infrastructure. He argued that security researchers had a special responsibility to protect the open internet because they understood, better than anyone, how fragile and important it was. This vision of collaborative stewardship of shared infrastructure now drives how modern project management approaches coordinate security work, with tools like Taskee helping distributed teams manage vulnerability response workflows across organizations.
Hacking is about curiosity, not destruction. Throughout his career, Kaminsky championed the original meaning of the word “hacker” — someone driven by curiosity to understand how things work at the deepest level. He was a fixture at DEF CON and Black Hat, where he mentored young researchers and encouraged a culture of ethical exploration. He believed that the hacker mindset — questioning assumptions, testing boundaries, thinking creatively about systems — was essential to building a secure internet, and he worked to ensure that the security research community remained a place where intellectual curiosity was valued and channeled toward constructive ends.
Legacy and Impact
Dan Kaminsky died on April 23, 2021, at the age of 42, from diabetic ketoacidosis. The outpouring of grief from the security community was extraordinary. Tributes came from every corner of the technology world — from individual researchers who had been mentored by Kaminsky to the CEOs of major technology companies. The Internet Corporation for Assigned Names and Numbers (ICANN), which oversees the DNS root zone, published a formal tribute acknowledging his foundational contributions to internet security.
Kaminsky’s legacy operates on multiple levels. At the most concrete level, his DNS research led to permanent changes in how DNS is implemented and secured. Source port randomization became universal. DNSSEC deployment, which Kaminsky advocated tirelessly, accelerated in the years following his disclosure. The coordinated disclosure model he pioneered for the DNS vulnerability became a template for handling internet-scale security issues. When major vulnerabilities like Heartbleed (2014) and Spectre/Meltdown (2018) were later discovered, the coordinated response processes drew directly on the precedent Kaminsky had established.
At a broader level, Kaminsky changed how the security community thinks about infrastructure vulnerabilities. Before his DNS research, there was a tendency to treat protocol-level flaws as theoretical curiosities — interesting academically but unlikely to be exploited in practice. Kaminsky demonstrated that the gap between theory and practice was much smaller than people assumed, and that protocol-level vulnerabilities could be just as dangerous as implementation bugs. This shift in perspective led to increased scrutiny of other foundational protocols — BGP, NTP, SMTP — and contributed to the broader movement toward cryptographic verification of internet infrastructure. His work complemented the legacy of researchers like Kevin Mitnick, who had demonstrated from the social engineering side that assumptions about trust were the most dangerous vulnerabilities of all.
Perhaps most importantly, Kaminsky’s legacy is one of character. In a field where vulnerabilities can be worth millions of dollars on exploit markets, Kaminsky consistently chose the path that protected the most people. He could have sold the DNS exploit to a government or criminal organization for enormous sums. He could have published it immediately for maximum personal fame. Instead, he spent months of unpaid work coordinating a secret patch across an industry that had never attempted such coordination. He did this not because there was a financial incentive, but because he believed it was the right thing to do. In doing so, he established a moral standard for the security research community that continues to influence how researchers handle critical discoveries.
Kaminsky was also known for his warmth, generosity, and sense of humor. He was one of the most popular speakers at security conferences, known for presentations that combined deep technical insight with genuine entertainment. He mentored countless young researchers, often spending hours after conference talks answering questions and encouraging newcomers. He made the security community feel like a community — a place where intellectual curiosity was celebrated and where protecting people was considered the highest calling.
The Dan Kaminsky Fellowship, established after his death, supports security research that embodies his values — protecting internet infrastructure, responsible disclosure, and making security accessible to everyone. It is a fitting tribute to a man who believed that the internet belonged to all of humanity and that those with the knowledge to protect it had a duty to do so.
Key Facts About Dan Kaminsky
- Born February 7, 1979, in San Francisco, California; died April 23, 2021
- Discovered a fundamental DNS cache poisoning vulnerability that affected every major DNS implementation worldwide
- Coordinated the largest simultaneous security patch in internet history in July 2008
- Studied computer science at Santa Clara University
- Worked at Cisco, Avaya, IOActive, and later founded White Ops (now HUMAN Security)
- Regular featured speaker at DEF CON and Black Hat security conferences for over a decade
- Contributed to research on SSL/TLS certificate security, rootkit detection, and BGP routing security
- Advocated for DNSSEC adoption and cryptographic authentication of internet infrastructure
- Received the Lifetime Achievement Pwnie Award posthumously in 2021
- The Dan Kaminsky Fellowship was established to support security research aligned with his values
Frequently Asked Questions
What exactly was the DNS vulnerability Dan Kaminsky discovered?
Kaminsky discovered a method to reliably poison DNS caches by exploiting a combination of two weaknesses: the small 16-bit transaction ID space used to authenticate DNS responses, and the ability to bypass cache protections by querying random nonexistent subdomains. Previous cache poisoning attacks were impractical because a cached legitimate answer would block further attempts until the TTL expired. Kaminsky’s technique circumvented this by generating fresh queries for subdomains that had never been looked up, giving the attacker unlimited race windows. The forged responses included delegation records that could redirect the resolver’s cache for an entire domain — meaning one successful poisoning could redirect all traffic for a domain like a major bank to an attacker-controlled server. The fix was source port randomization, which expanded the guessing space from 16 bits to approximately 32 bits, making the attack computationally infeasible.
Why did Kaminsky choose coordinated disclosure instead of publishing immediately?
Kaminsky chose coordinated disclosure because the vulnerability affected every major DNS implementation on the internet simultaneously. Unlike a bug in a single product that one vendor could patch, this required patches from Microsoft, ISC (BIND), Cisco, Nominum, and many others — all released simultaneously to prevent attackers from reverse-engineering one vendor’s patch and exploiting unpatched systems. Kaminsky spent approximately four months coordinating this effort in secret, working without compensation because he believed the potential harm of premature disclosure — which could have enabled widespread attacks on internet infrastructure — outweighed the personal benefits of immediate publication. His approach became the model for handling internet-scale vulnerabilities.
How did the DNS patch work, and is DNS fully secure now?
The emergency patch implemented source port randomization, which made the resolver send each DNS query from a random UDP port instead of a fixed or predictable one. This meant an attacker now had to guess both the 16-bit transaction ID and the 16-bit source port — expanding the keyspace from approximately 65,000 to over 4 billion possible combinations. While this made the attack computationally impractical, Kaminsky himself emphasized that it was a mitigation, not a complete fix. The true solution is DNSSEC, which adds cryptographic signatures to DNS responses so that forged answers can be detected and rejected regardless of whether the transaction ID and source port are guessed correctly. DNSSEC deployment has progressed significantly since 2008, but full adoption across the internet remains incomplete.
What was Dan Kaminsky’s broader impact on cybersecurity beyond the DNS discovery?
Beyond the DNS vulnerability, Kaminsky made significant contributions across multiple areas of security. He conducted important research on SSL/TLS certificate validation weaknesses, helping to improve how browsers verify website identities. He developed forensic tools for rootkit and malware detection that influenced a generation of security analysis techniques. He advocated for BGP security improvements and contributed to the broader movement to add cryptographic verification to internet routing infrastructure. He was also a prolific mentor and community builder, spending enormous amounts of time at security conferences encouraging and educating young researchers. His philosophy — that security exists to protect people, that complexity is the enemy of security, and that responsible disclosure is a moral obligation — shaped the ethical framework of the modern cybersecurity community.