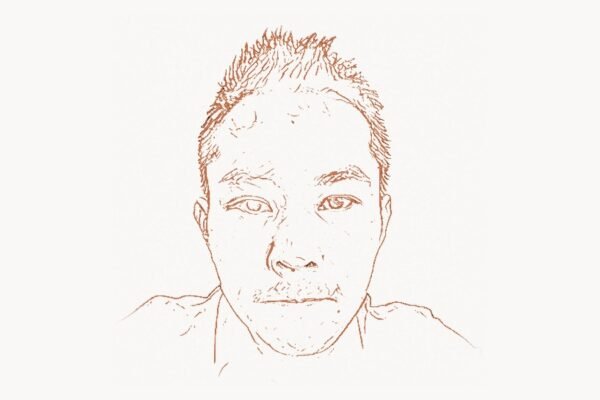
In 1995, a 24-year-old graduate student sued the United States government — and won. The weapon in question was not a firearm or classified document but a few pages of source code implementing an encryption algorithm. Daniel Julius Bernstein, known universally as djb, argued that software was speech and that restricting its publication violated the First Amendment. That case, Bernstein v. United States, rewrote the rules of cryptography export and opened the floodgates for the modern encrypted internet. But the court victory was only the beginning. Over the following three decades, Bernstein would produce some of the most important cryptographic primitives in use today — Curve25519, ChaCha20, Salsa20, Poly1305 — while simultaneously creating foundational internet infrastructure software like qmail and djbdns, all driven by an uncompromising philosophy that security must be correct by default, not bolted on as an afterthought.
Early Life and Education
Daniel Julius Bernstein was born on October 29, 1971, in East Palisades, New York. He showed exceptional mathematical aptitude from an early age and became fascinated with both number theory and computers during his high school years. He enrolled at New York University, where he studied mathematics and computer science, earning his bachelor’s degree in 1991. During his undergraduate years he was already exploring cryptographic algorithms, publishing early work on fast multiplication techniques that would later prove crucial to his cryptographic designs.
Bernstein continued his education at the University of California, Berkeley, where he pursued a Ph.D. in mathematics under the supervision of Hendrik Lenstra, a renowned number theorist. His doctoral research focused on computational number theory and the efficiency of integer factoring algorithms. It was during this period at Berkeley that Bernstein developed the Snuffle encryption system — a relatively simple algorithm that nonetheless became the centerpiece of one of the most consequential legal battles in the history of computing. Like Claude Shannon, who laid the mathematical foundations of information theory, Bernstein saw cryptography as fundamentally a mathematical discipline where elegance and provable properties trumped ad hoc complexity.
He completed his Ph.D. in 1995 and went on to hold positions at the University of Illinois at Chicago, where he became a professor of mathematics and computer science. In 2012 he also accepted a position as a research professor at Eindhoven University of Technology in the Netherlands, splitting his time between continents while maintaining a prodigious research output.
The Bernstein v. United States Breakthrough
Technical Innovation
The technical innovation at the heart of the case was the Snuffle encryption system, which Bernstein had developed as part of his research. Snuffle worked by converting a one-way hash function into an encryption function — a clever technique that demonstrated how fundamental the relationship between different cryptographic primitives was. The algorithm itself was not revolutionary, but its existence posed a direct challenge to U.S. export regulations that classified encryption software as a “munition” under the International Traffic in Arms Regulations (ITAR) and later the Export Administration Regulations (EAR).
Bernstein wanted to publish the Snuffle source code, present it at academic conferences, and teach it to students. The State Department told him he would need a license to do so — in effect, treating his mathematical research the same as exporting weapons to foreign adversaries. Bernstein, represented by the Electronic Frontier Foundation, filed suit in 1995 arguing that source code was a form of expressive speech protected by the First Amendment.
/* Simplified illustration of hash-to-cipher conversion concept
(inspired by Bernstein's Snuffle approach) */
#include <stdint.h>
#include <string.h>
void hash_function(const uint8_t *input, uint8_t *output, size_t len);
void snuffle_encrypt(const uint8_t *key, uint64_t nonce,
const uint8_t *plaintext, uint8_t *ciphertext,
size_t len)
{
uint8_t block[64];
uint8_t hash_input[48]; /* key(32) + nonce(8) + counter(8) */
memcpy(hash_input, key, 32);
memcpy(hash_input + 32, &nonce, 8);
for (size_t i = 0; i < len; i += 64) {
uint64_t counter = i / 64;
memcpy(hash_input + 40, &counter, 8);
/* Hash produces a pseudorandom keystream block */
hash_function(hash_input, block, 48);
size_t chunk = (len - i < 64) ? (len - i) : 64;
for (size_t j = 0; j < chunk; j++) {
ciphertext[i + j] = plaintext[i + j] ^ block[j];
}
}
}Why It Mattered
In 1996, Judge Marilyn Hall Patel ruled that source code was protected speech under the First Amendment and that the encryption export regulations constituted an unconstitutional prior restraint. The government appealed, and the Ninth Circuit Court of Appeals upheld the ruling in 1999 in a landmark decision. The case had seismic implications: it effectively ended the era in which the U.S. government could prevent researchers from publishing cryptographic code, paving the way for the widespread adoption of strong encryption in web browsers, email clients, and messaging applications.
The ripple effects of Bernstein v. United States are still felt today. Without that ruling, the open-source cryptography libraries that underpin modern internet security might never have been legally distributable. Technologies like TLS, SSH, and end-to-end encrypted messaging owe a debt to Bernstein’s willingness to challenge governmental authority through the courts. Much like Martin Hellman and Whitfield Diffie, who introduced public-key cryptography to the world in the face of NSA pressure, Bernstein demonstrated that the progress of cryptography depends as much on the courage of its practitioners as on the strength of their algorithms.
Other Major Contributions
Bernstein’s legal victory would have been enough to secure his reputation, but his technical contributions over the following decades have been equally transformative. His body of work spans cryptographic algorithms, internet infrastructure software, and advances in computational number theory.
Curve25519 and Ed25519. Perhaps his most widely deployed creation, Curve25519 is an elliptic curve designed for key agreement protocols. Published in 2006, it was built from the ground up to resist implementation errors — a design philosophy that set it apart from the NIST-recommended curves, which many cryptographers distrusted due to their opaque parameter generation. Ed25519, the associated signature scheme, provides fast and secure digital signatures. Together, they are now used in OpenSSH, Signal, WhatsApp, WireGuard, and countless other applications. The curve’s parameters were chosen to be “nothing up my sleeve” numbers, providing full transparency about why each constant was selected.
ChaCha20 and Salsa20. Bernstein designed the Salsa20 stream cipher in 2005 and its improved variant ChaCha20 in 2008. These ciphers are remarkably fast in software implementations and avoid the timing side-channel attacks that plagued AES on platforms without hardware acceleration. Google adopted ChaCha20-Poly1305 as a TLS cipher suite in Chrome in 2014, and it subsequently became an IETF standard (RFC 8439). Today ChaCha20-Poly1305 secures a substantial fraction of all HTTPS traffic on mobile devices. This work on authenticated encryption resonates with the broader challenges of building trustworthy software systems — a problem that Bruce Schneier has spent decades articulating to both technical and general audiences.
Poly1305. The Poly1305 message authentication code, designed to work alongside Salsa20 and ChaCha20, provides a fast and provably secure way to verify message integrity. Its design is elegant: Poly1305 computes a polynomial evaluation modulo a prime just slightly less than 2130, achieving both speed and strong security guarantees.
qmail. Released in 1996, qmail was a mail transfer agent designed as a secure replacement for sendmail, which had been plagued by an unending series of security vulnerabilities. Bernstein’s approach was radical: he decomposed the mail system into small, isolated modules with minimal privilege, applied rigorous input validation, and offered a security guarantee — a $500 bounty for anyone who could find a security hole. That bounty went unclaimed for over a decade. qmail demonstrated that it was possible to build internet-facing software that was both functional and genuinely secure, influencing the design philosophy of countless projects that followed.
djbdns. Following the same security-first philosophy, Bernstein released djbdns in 2001 as an alternative to BIND, the dominant DNS server software at the time. BIND had a notoriously poor security record, and djbdns offered a compact, auditable alternative. Its dnscache component became widely adopted for its resistance to DNS cache poisoning attacks — a threat that Dan Kaminsky would later demonstrate to be far more severe than anyone had imagined when he disclosed a fundamental flaw in DNS in 2008.
NaCl and TweetNaCl. In 2008, Bernstein, along with Tanja Lange and Peter Schwabe, introduced NaCl (Networking and Cryptography library), a high-level cryptographic library designed to make it easy for developers to use cryptography correctly. NaCl provides simple APIs for encryption, decryption, signing, and verification, hiding the dangerous complexity that leads to implementation bugs. TweetNaCl, a minimal version of NaCl fitting in 100 tweets worth of code, demonstrated that a complete, auditable cryptographic library could fit in just a few kilobytes of source code.
Post-quantum cryptography. Bernstein has been one of the most vocal and active researchers in post-quantum cryptography — developing cryptographic systems that resist attack by quantum computers. His submissions to the NIST Post-Quantum Cryptography standardization process, including lattice-based and code-based schemes, reflect his long-term thinking about the future of cryptographic security. He has also been publicly critical of aspects of the NIST process, consistent with his lifelong insistence on transparency in cryptographic standards.
Philosophy and Approach
Bernstein’s technical contributions are inseparable from a distinctive philosophy about how software and cryptography should be designed. His approach has influenced generations of security researchers and software engineers, even those who have never used his code directly.
Key Principles
- Security by default, not by configuration. Bernstein believes that software should be secure in its default state. If a user has to change a setting to be safe, the design has failed. This principle runs through qmail, djbdns, and NaCl alike.
- Minimize attack surface. His programs are famously compact. qmail’s entire codebase was small enough to be audited line by line. He decomposes complex systems into isolated, minimal-privilege components that limit the blast radius of any single vulnerability.
- Constant-time code. Long before timing attacks were mainstream knowledge, Bernstein insisted that cryptographic implementations must run in constant time regardless of input values, eliminating an entire class of side-channel vulnerabilities.
- Transparent parameter selection. Bernstein advocates for “nothing up my sleeve” numbers — parameters whose derivation is fully public and verifiable, in contrast to the opaque constants in some government-endorsed standards.
- Simplicity over generality. Rather than building frameworks that handle every possible use case, Bernstein builds tools that solve specific problems extremely well. His software tends to have fewer features but far fewer bugs.
- Public auditability. All of Bernstein’s major cryptographic designs come with complete specifications, security proofs, and reference implementations. He puts his money where his mouth is — literally, with bug bounties.
- Distrust of closed standards processes. Bernstein has been a persistent critic of standardization processes that lack transparency, arguing that backdoored or weakened standards are a greater threat than no standard at all.
# ChaCha20 quarter-round function — the core building block
# Demonstrates Bernstein's preference for simple, auditable operations:
# only 32-bit addition, XOR, and bit rotation — no table lookups,
# no data-dependent branches, no timing side channels.
def rotl32(v, n):
"""Left-rotate a 32-bit integer by n bits."""
return ((v << n) | (v >> (32 - n))) & 0xFFFFFFFF
def quarter_round(state, a, b, c, d):
"""ChaCha20 quarter-round: mixes four 32-bit state words."""
state[a] = (state[a] + state[b]) & 0xFFFFFFFF
state[d] ^= state[a]
state[d] = rotl32(state[d], 16)
state[c] = (state[c] + state[d]) & 0xFFFFFFFF
state[b] ^= state[c]
state[b] = rotl32(state[b], 12)
state[a] = (state[a] + state[b]) & 0xFFFFFFFF
state[d] ^= state[a]
state[d] = rotl32(state[d], 8)
state[c] = (state[c] + state[d]) & 0xFFFFFFFF
state[b] ^= state[c]
state[b] = rotl32(state[b], 7)
# Full ChaCha20 block function: 20 rounds (10 double-rounds)
# of quarter_round applications on a 4x4 matrix of 32-bit words.
# No S-boxes, no key-dependent table lookups — pure ARX design.Legacy and Impact
Daniel Bernstein’s influence on modern computing extends across three distinct domains: law, cryptography, and systems software. Few figures in the history of technology have made landmark contributions in even two of these areas; Bernstein has reshaped all three.
On the legal front, Bernstein v. United States established the principle that code is speech — a foundation upon which the entire open-source software movement rests. Without that precedent, the international collaboration that produces Linux, OpenSSL, and hundreds of other projects might have been legally impossible, or at least severely constrained. Richard Stallman fought for software freedom through licenses and philosophy; Bernstein fought for it in court.
In cryptography, the algorithms Bernstein designed have become the infrastructure of digital trust. Curve25519 and Ed25519 are the default key exchange and signature algorithms in OpenSSH. ChaCha20-Poly1305 protects mobile HTTPS connections worldwide. Signal Protocol, which provides end-to-end encryption for Signal, WhatsApp, and other messaging applications, relies on Curve25519. These are not niche tools; they are the bedrock of everyday privacy for billions of people.
In systems software, qmail and djbdns proved that internet-facing services could be built to be effectively impervious to remote exploitation. This was a radical claim in the late 1990s, when buffer overflows and privilege escalation bugs were practically expected. Bernstein’s modular, least-privilege architecture anticipated many of the principles that would later be formalized in containerization and microservices — ideas that Solomon Hykes would bring to the mainstream with Docker years later.
Bernstein continues to be active in research, focusing particularly on post-quantum cryptography and the long-term security of the internet against quantum computing threats. His work remains characterized by the same combination of mathematical rigor, engineering discipline, and willingness to challenge institutional authority that has defined his career from the start.
Key Facts
- Full name: Daniel Julius Bernstein
- Born: October 29, 1971, East Palisades, New York, USA
- Education: B.A. in Mathematics, New York University; Ph.D. in Mathematics, University of California, Berkeley
- Known for: Curve25519, Ed25519, ChaCha20, Salsa20, Poly1305, qmail, djbdns, NaCl
- Landmark case: Bernstein v. United States (1996–1999) — established source code as protected free speech
- Positions: Professor at University of Illinois at Chicago; Research Professor at Eindhoven University of Technology
- Awards: Levchin Prize for Real-World Cryptography (2017)
- Philosophy: Security by default, minimal attack surface, constant-time execution, transparent standards
- Active research: Post-quantum cryptography, lattice-based and code-based cryptosystems
Frequently Asked Questions
What is Curve25519 and why is it important?
Curve25519 is an elliptic curve designed by Daniel Bernstein specifically for use in Diffie-Hellman key exchange. It was published in 2006 and quickly became one of the most widely used curves in cryptography. Its importance lies in several design choices: it is resistant to common implementation mistakes such as invalid-curve attacks, it operates in constant time to prevent timing side-channel leaks, and its parameters are fully transparent rather than chosen through an opaque process. Curve25519 is now used in SSH, TLS, Signal, WireGuard, Tor, and many other protocols. Its companion signature scheme, Ed25519, provides fast and secure digital signatures used in everything from code signing to blockchain protocols.
How did Bernstein v. United States change cryptography?
Before the case, the U.S. government classified strong encryption software as a munition, subject to the same export restrictions as weapons systems. This meant that researchers could not freely publish their encryption code, open-source cryptography projects could not be distributed internationally, and web browsers were limited to weak 40-bit encryption for international users. Bernstein’s lawsuit challenged this classification on First Amendment grounds, arguing that source code is a form of expressive speech. The courts agreed, and the resulting legal precedent forced the U.S. government to relax its encryption export controls significantly by the year 2000. This liberalization enabled the global adoption of strong encryption in web browsers, email, VPNs, and messaging applications that we take for granted today.
What is ChaCha20-Poly1305 and where is it used?
ChaCha20-Poly1305 is an authenticated encryption with associated data (AEAD) construction that combines the ChaCha20 stream cipher for encryption with the Poly1305 message authentication code for integrity verification. It was standardized by the IETF as RFC 8439. Google adopted it for use in Chrome and Android in 2014 as an alternative to AES-GCM, particularly for devices without hardware AES acceleration where ChaCha20 is significantly faster. It is now used across TLS, SSH (OpenSSH), WireGuard, the Noise protocol framework, and many other applications. Its design avoids the timing side channels and implementation pitfalls that can affect AES-based constructions on platforms without dedicated hardware support.
Why did Bernstein create qmail and djbdns?
Bernstein created qmail (1996) and djbdns (2001) because the dominant alternatives — sendmail and BIND, respectively — had appalling security records. Sendmail was one of the most frequently exploited programs in the history of Unix, and BIND suffered from a constant stream of remotely exploitable vulnerabilities. Bernstein took a fundamentally different design approach: decomposing each system into isolated, minimal-privilege components; rigorously validating all inputs; and keeping the codebases small enough to be auditable. He backed his confidence with a public security guarantee — offering monetary bounties for anyone who could find a security flaw in qmail. These projects proved that security-critical internet infrastructure could be built correctly and helped establish the design principles of privilege separation and minimal trusted computing base that are now standard practice in security engineering.