Imagine you have built a complex piece of software — perhaps an air traffic control system, a medical device, or a nuclear reactor controller. You have tested it exhaustively, written thousands of unit tests, and run it through months of quality assurance. Yet a nagging question persists: have you truly covered every possible execution path? Every conceivable sequence of events? Edmund Merrill Clarke Jr. spent his career answering that question, and his answer changed the way humanity builds reliable systems forever. His invention, model checking, gave engineers a mathematically rigorous method to explore every single state a system can reach — automatically, exhaustively, and with a proof when something goes wrong.
Early Life and Academic Foundations
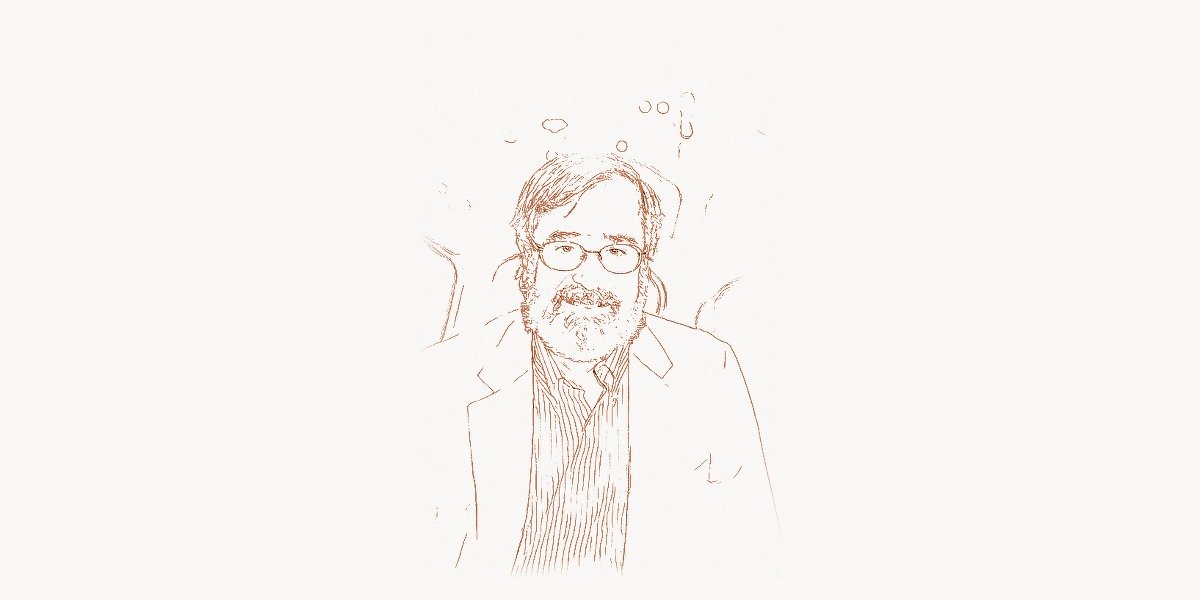
Edmund Clarke was born on July 27, 1945, in Greer, South Carolina. Growing up in the American South during the postwar era, Clarke showed an early affinity for mathematics and logical reasoning. He pursued his undergraduate studies at the University of Virginia, where he earned a Bachelor of Arts in mathematics in 1967. His academic trajectory then carried him to Duke University, where he completed a Master of Arts in mathematics in 1968.
The pivotal turn came when Clarke moved to Cornell University for his doctoral work. Under the supervision of Robert Constable, he completed his PhD in computer science in 1976. Cornell at the time was a hotbed of research in programming languages, formal methods, and theoretical computer science. The intellectual environment there planted the seeds for what would become Clarke’s life work — the application of mathematical logic to the practical problem of software and hardware correctness.
After completing his doctorate, Clarke joined the faculty at Harvard University, where he began exploring the intersection of logic and program verification. It was during this period that he started wrestling with the fundamental question that would define his career: could a machine automatically verify whether a finite-state system satisfies a given specification?
The Birth of Model Checking
In 1981, Edmund Clarke and his graduate student E. Allen Emerson published a groundbreaking paper that introduced the concept of model checking. Working independently, Jean-Pierre Queille and Joseph Sifakis in France developed a similar approach around the same time. The core idea was elegantly simple in principle yet profoundly powerful in practice: given a finite-state model of a system and a property expressed in temporal logic, automatically and exhaustively verify whether the model satisfies the property.
Before model checking, formal verification relied heavily on theorem proving — a laborious, manual process where a human expert would construct mathematical proofs that a system met its specifications. This was the domain of pioneers like Tony Hoare, whose axiomatic semantics provided a foundation for reasoning about program correctness. While theorem proving was powerful, it required deep expertise and significant human effort, making it impractical for large industrial systems.
Model checking offered a radical alternative. Instead of asking a human to construct a proof, the model checker would systematically explore every reachable state of the system, checking at each state whether the desired property held. If the property was violated, the tool would produce a counterexample — a concrete execution trace showing exactly how the system could reach the offending state. This counterexample generation proved to be one of model checking’s most valuable features in practice, because it gave engineers a precise diagnosis of the bug rather than just a binary pass-or-fail verdict.
Temporal Logic: The Language of System Properties
At the heart of model checking lies temporal logic — a formal language for expressing properties about how systems behave over time. Clarke and Emerson adopted and extended Computation Tree Logic (CTL), which allows engineers to specify properties such as “the system will eventually reach a safe state,” “a request is always eventually followed by a response,” and “the system can never simultaneously grant access to two competing processes.”
CTL reasons over the branching tree of all possible future computations from any given state. It uses path quantifiers (A for “all paths” and E for “there exists a path”) combined with temporal operators (G for “globally,” F for “eventually,” X for “next state,” and U for “until”). This combination gives engineers a remarkably expressive vocabulary for describing correctness properties.
Consider a simple mutual exclusion protocol — a system where two processes compete for access to a shared resource. A critical safety property is that both processes must never be in their critical section simultaneously. In CTL, this property can be expressed as:
AG ¬(process1_in_critical ∧ process2_in_critical)This formula reads: “For All paths, Globally, it is never the case that process 1 is in its critical section and process 2 is in its critical section at the same time.” The model checker then explores every reachable state of the system to verify this property holds universally, or provides a counterexample trace if it does not.
A liveness property — ensuring the system makes progress — might be expressed as:
AG (request → AF grant)This states: “For All paths, Globally, whenever a request occurs, then on All paths from that point, the grant will eventually (Finally) happen.” These specifications, while compact, capture deep behavioral requirements that would be extremely difficult to test for using conventional methods. The work Clarke did on temporal logic specifications shares intellectual roots with the theoretical foundations laid by Alan Turing, whose formalization of computation made such reasoning about machine behavior possible in the first place.
The State Explosion Problem and Symbolic Model Checking
The elegance of model checking came with a formidable challenge: the state explosion problem. Real-world systems with multiple interacting components generate an astronomically large number of possible states. A system with just 30 Boolean variables has over one billion reachable states. Industrial hardware designs with thousands of state variables produce state spaces that dwarf the number of atoms in the observable universe.
Early model checking algorithms used explicit state enumeration — literally storing and visiting each state individually. This approach worked well for small systems but crumbled under the weight of realistic designs. The field might have remained an academic curiosity if not for a breakthrough that Clarke achieved in collaboration with his students Ken McMillan, David Dill, and others in the late 1980s and early 1990s.
The breakthrough was symbolic model checking, which used Binary Decision Diagrams (BDDs) to represent sets of states and transition relations compactly. Instead of enumerating individual states, symbolic model checking manipulated entire sets of states simultaneously using Boolean operations. A BDD could represent a set of billions of states in a data structure that fit comfortably in memory, and operations on these sets — union, intersection, complement — could be performed efficiently.
This innovation expanded the reach of model checking from systems with thousands of states to systems with more than 1020 states. Suddenly, model checking could handle real industrial hardware designs — integrated circuits, bus protocols, cache coherence mechanisms. The impact was immediate and transformative. Companies like Intel, IBM, and Cadence began integrating symbolic model checking into their design verification workflows.
The algorithmic thinking behind symbolic model checking shares a philosophical kinship with the work of Edsger Dijkstra, who championed the idea that rigorous mathematical reasoning should guide the construction and verification of programs. Both Clarke and Dijkstra believed that correctness should not be an afterthought but a fundamental design concern.
Counterexample-Guided Abstraction Refinement
Even with symbolic methods, many real-world systems remained beyond the reach of model checking. Software systems, in particular, posed enormous challenges because they operate over infinite or extremely large data domains. Clarke’s response was another paradigm-shifting contribution: Counterexample-Guided Abstraction Refinement, or CEGAR.
The CEGAR framework, introduced by Clarke along with Orna Grumberg, Somesh Jha, Yuan Lu, and Helmut Veith in 2000, provided an automated approach to managing the complexity of model checking. The key insight was to start with a coarse, abstract model of the system — one that was small enough to model-check efficiently but might introduce spurious behaviors not present in the original system. When the model checker found a counterexample in the abstract model, the CEGAR loop would check whether this counterexample corresponded to a real behavior in the concrete system. If it did, a genuine bug had been found. If it did not (a spurious counterexample), the abstraction was automatically refined to eliminate the spurious behavior, and the process repeated.
CEGAR became one of the most influential ideas in automated verification, spawning an entire family of techniques used in software model checking, program analysis, and even automated theorem proving. Tools like SLAM (developed at Microsoft Research for verifying Windows device drivers) and BLAST employed CEGAR-based approaches to verify real software at scale. The impact on software reliability in critical systems was substantial — Microsoft used CEGAR-inspired technology to catch thousands of bugs in device drivers before they shipped to customers.
The Turing Award: Recognition of a Revolution
In 2007, the Association for Computing Machinery awarded the A.M. Turing Award — widely considered the Nobel Prize of computing — to Edmund Clarke, E. Allen Emerson, and Joseph Sifakis “for their role in developing model checking into a highly effective verification technology that is widely adopted in the hardware and software industries.” The award recognized not just the theoretical elegance of model checking but its profound practical impact.
By the time Clarke received the Turing Award, model checking had become an indispensable part of the hardware design process. Every major semiconductor company used model checking tools as part of their verification methodology. The technique had also made significant inroads into software verification, protocol analysis, and even biological systems modeling. Clarke joined the ranks of computing luminaries like Donald Knuth, whose contributions fundamentally shaped how computer scientists think about their craft.
Clarke’s Turing Award lecture emphasized the practical nature of model checking’s contributions. He described how the technique had found bugs in designs that had passed extensive simulation testing — bugs that would have been virtually impossible to discover through testing alone. These were not toy examples but real defects in production hardware from major manufacturers, some of which could have caused system crashes or data corruption in deployed products.
Industrial Impact: From Silicon to Safety-Critical Systems
The industrial adoption of model checking represents one of the most successful transfers of technology from academic computer science to engineering practice. In the hardware industry, model checking tools became integral to the design verification flow for microprocessors, memory controllers, and communication protocols. The infamous Pentium FDIV bug of 1994, which cost Intel approximately 475 million dollars, served as a powerful catalyst for the adoption of formal verification methods in chip design.
Intel, in particular, became a major adopter of model checking techniques following the FDIV incident. The company invested heavily in formal verification infrastructure, and model checking became a standard part of the process for verifying critical arithmetic units and control logic. Other semiconductor companies — including AMD, IBM, ARM, and Cadence — similarly integrated model checking into their workflows.
Beyond hardware, model checking found applications in verifying communication protocols, security protocols, and safety-critical systems. The technique was used to verify aspects of the IEEE 1394 (FireWire) protocol, the PCI bus protocol, and various cache coherence protocols. In the aerospace and automotive industries, model checking became part of the certification process for safety-critical software, helping to ensure that flight control systems, braking systems, and other life-critical components met their specifications. Teams working on such complex, multi-component projects often benefit from systematic task management approaches to coordinate verification efforts across engineering disciplines.
Software Model Checking and Beyond
While model checking began in the hardware domain, Clarke was deeply committed to extending its reach to software verification. Software posed fundamentally different challenges — programs operate over unbounded data domains, use recursive procedures, allocate dynamic memory, and interact with complex operating system environments. The state spaces of software systems are not merely large; they are often infinite.
Clarke’s CEGAR framework was a crucial step toward making software model checking practical. His group at Carnegie Mellon developed tools that could automatically verify properties of C programs, handling features like pointer arithmetic, dynamic memory allocation, and concurrency. This work built on and extended the theoretical foundations established by researchers like John McCarthy, whose early work on formal reasoning about programs helped establish the field.
The Bounded Model Checking (BMC) approach, which Clarke helped develop, provided another avenue for applying model checking to software. Instead of verifying properties for all possible executions, BMC searches for property violations within executions of a bounded length. This transforms the verification problem into a Boolean satisfiability (SAT) problem, leveraging the remarkable advances in SAT solver technology that occurred in the early 2000s. BMC proved highly effective at finding bugs in both hardware and software, and its integration with modern SAT and SMT (Satisfiability Modulo Theories) solvers made it a practical tool for industrial use.
Code Example: Exploring State Spaces
To illustrate the fundamental concept behind model checking, consider a simplified state-space exploration algorithm. The following pseudocode demonstrates how a model checker systematically explores all reachable states of a system to verify a safety property:
// Simplified explicit-state model checking algorithm
// Verifies: AG safe_property (property holds in ALL reachable states)
function modelCheck(initialState, transitionRelation, safetyProperty):
visited = emptySet()
worklist = queue()
worklist.enqueue(initialState)
while worklist is not empty:
currentState = worklist.dequeue()
if currentState in visited:
continue
visited.add(currentState)
// Check if safety property holds in current state
if NOT safetyProperty(currentState):
// Property violated — generate counterexample
trace = reconstructPath(initialState, currentState)
return Failure(counterexample: trace)
// Explore all successor states
for each nextState in transitionRelation(currentState):
if nextState not in visited:
worklist.enqueue(nextState)
// All reachable states explored, property holds everywhere
return Success("Property AG safe verified for all reachable states")
// Example: Verifying mutual exclusion for 2-process system
// States: (pc1, pc2, turn) where pc ∈ {idle, waiting, critical}
initialState = (idle, idle, 1)
function transitions(state):
(pc1, pc2, turn) = state
successors = []
// Process 1 transitions
if pc1 == idle: successors.add((waiting, pc2, turn))
if pc1 == waiting AND (pc2 != waiting OR turn == 1):
successors.add((critical, pc2, turn))
if pc1 == critical: successors.add((idle, pc2, 2))
// Process 2 transitions (symmetric)
if pc2 == idle: successors.add((pc1, waiting, turn))
if pc2 == waiting AND (pc1 != waiting OR turn == 2):
successors.add((pc1, critical, turn))
if pc2 == critical: successors.add((pc1, idle, 1))
return successors
function mutualExclusion(state):
(pc1, pc2, turn) = state
return NOT (pc1 == critical AND pc2 == critical)
result = modelCheck(initialState, transitions, mutualExclusion)This simple algorithm captures the essence of what Clarke’s tools do at a much larger scale. The power of the approach becomes clear when you consider that this exhaustive exploration guarantees correctness — if the algorithm terminates with success, no execution of the system can ever violate the property. This stands in stark contrast to testing, which can only demonstrate the presence of bugs, never their absence.
Academic Legacy and Mentorship
Edmund Clarke spent the majority of his career at Carnegie Mellon University, where he joined the faculty in 1982 and remained until his retirement. At CMU, he held the FORE Systems University Professor of Computer Science and Electrical and Computer Engineering chair. His research group became one of the premier centers for formal verification research in the world.
Clarke’s influence extended far beyond his own research contributions. He mentored dozens of PhD students and postdoctoral researchers, many of whom went on to become leaders in formal verification and related fields. Ken McMillan, whose PhD thesis under Clarke’s supervision introduced symbolic model checking with BDDs, became a leading figure in formal verification at Cadence and later Microsoft Research. The collaborative, intellectually generous environment Clarke fostered at CMU produced a generation of researchers who carried model checking into new domains and applications.
His academic rigor mirrored the disciplined approach advocated by Leslie Lamport, another giant of formal methods whose work on distributed systems specification with TLA+ complemented Clarke’s contributions to automated verification. Together, their work represented two pillars of the formal methods community — Lamport’s approach emphasizing human-guided specification and Clarke’s focusing on automated verification.
Clarke received numerous honors throughout his career, including fellowship in the Association for Computing Machinery, the IEEE, and the American Academy of Arts and Sciences. He was elected to the National Academy of Engineering and the National Academy of Sciences. In addition to the Turing Award, he received the IEEE Harry H. Goode Memorial Award, the ACM Paris Kanellakis Theory and Practice Award, and multiple honorary doctorates from universities across Europe.
The Broader Impact on Computing
Model checking’s influence extends far beyond the specific domain of hardware and software verification. The techniques Clarke developed have been applied to biological systems modeling, where researchers use model checking to analyze the behavior of genetic regulatory networks and signal transduction pathways. In cybersecurity, model checking has been used to verify cryptographic protocols and discover vulnerabilities in security mechanisms.
The concept of exhaustive state-space exploration has influenced fields as diverse as artificial intelligence planning, robotics, and autonomous systems verification. As autonomous vehicles and AI systems become increasingly prevalent, the need for rigorous verification techniques has never been greater. Clarke’s work provides the intellectual foundation for much of this ongoing research. Organizations developing complex, multi-disciplinary technology products can benefit from structured project management methodologies that incorporate formal verification milestones into their development lifecycles.
The field Clarke helped create has also evolved in response to new challenges. Probabilistic model checking extends the classical framework to handle systems with stochastic behavior. Runtime verification applies model checking principles to monitoring running systems. Parametric model checking deals with systems whose behavior depends on unspecified parameters. Each of these extensions builds on the foundation Clarke laid in the early 1980s.
The philosophical impact of model checking on software engineering culture cannot be overstated. Before model checking, the dominant attitude in the industry was that testing was sufficient for quality assurance. Clarke’s work demonstrated convincingly that exhaustive verification was not only possible but practical, shifting the conversation from “have we tested enough?” to “have we verified the critical properties?” This shift in mindset — echoing the intellectual precision championed by Edsger Dijkstra in his advocacy for structured programming — has led to higher standards of reliability in safety-critical systems.
Final Years and Passing
Edmund Clarke passed away on December 22, 2020, at the age of 75. His death came during the global COVID-19 pandemic, a time when the reliability of technology infrastructure — from hospital systems to vaccine distribution logistics — underscored the importance of the verification techniques he had championed. The computing community mourned the loss of a visionary whose work had saved countless lives by ensuring the correctness of critical systems.
Clarke’s legacy lives on through the tools, techniques, and intellectual frameworks he created. Model checking continues to be an active and vibrant area of research, with new algorithms, tools, and applications emerging regularly. The annual Computer Aided Verification (CAV) conference, which Clarke helped nurture throughout his career, remains one of the premier venues for formal verification research. His former students and collaborators continue to push the boundaries of what automated verification can accomplish.
Frequently Asked Questions
What is model checking and why is it important?
Model checking is an automated technique for verifying whether a finite-state system satisfies a given property expressed in temporal logic. Unlike testing, which can only examine a finite number of execution paths, model checking exhaustively explores every reachable state of the system. This makes it capable of providing mathematical guarantees of correctness. It is particularly important for safety-critical systems — such as medical devices, aircraft control systems, and nuclear plant controllers — where a single undetected bug could have catastrophic consequences. When a property is violated, the model checker produces a counterexample trace showing exactly how the system can reach the error state, making it invaluable for debugging as well as verification.
How does model checking differ from traditional software testing?
Traditional software testing executes a system with specific inputs and checks whether the outputs match expectations. No matter how many test cases are written, testing can only cover a tiny fraction of all possible execution paths in a complex system. Model checking, by contrast, explores every reachable state of the system systematically. If a property holds, model checking provides a mathematical proof that no execution can violate it. If a property fails, it provides a precise counterexample. The key trade-off is that model checking requires a formal model of the system and works best on finite-state systems, while testing can be applied to any running program without a formal model.
What was Edmund Clarke’s most significant contribution to computer science?
Clarke’s most significant contribution was the co-invention of model checking in 1981, along with E. Allen Emerson, and independently by Joseph Sifakis. Beyond the initial invention, Clarke made critical follow-up contributions that made model checking practical for industrial use. Symbolic model checking using Binary Decision Diagrams expanded the technique’s capacity from thousands to billions of states. The CEGAR (Counterexample-Guided Abstraction Refinement) framework enabled model checking to be applied to software systems. These contributions collectively earned Clarke the 2007 Turing Award and transformed the verification practices of the entire semiconductor and safety-critical software industries.
What is the state explosion problem in model checking?
The state explosion problem refers to the exponential growth in the number of states that must be explored as the number of components or variables in a system increases. A system with n Boolean variables can have up to 2n reachable states. When multiple components run concurrently, the total state space is the product of the individual component state spaces. For realistic industrial systems with hundreds or thousands of state variables, the resulting state space can be astronomically large — far too large for explicit enumeration. Clarke addressed this challenge through symbolic model checking (using BDDs to represent state sets compactly) and abstraction refinement techniques (CEGAR), which remain the primary strategies for managing state explosion today.
How is model checking used in industry today?
Model checking is widely used across multiple industries. In semiconductor design, every major chip manufacturer — including Intel, AMD, ARM, and NVIDIA — uses model checking tools as part of their verification workflow to catch design bugs before fabrication. In software, Microsoft’s Static Driver Verifier uses model-checking techniques to verify Windows device drivers. In aerospace, companies use model checking to verify flight control software and comply with certification standards such as DO-178C. The automotive industry applies model checking to verify safety-critical embedded systems for braking, steering, and autonomous driving functions. Telecommunications companies use model checking to verify network protocols, and cybersecurity researchers use it to analyze cryptographic and authentication protocols for vulnerabilities.