In the early 1960s, while most computer scientists were busy writing programs that solved practical problems, a young Venezuelan-born mathematician was asking a far more radical question: what makes a problem inherently hard? Manuel Blum did not just want to know if a particular algorithm was slow — he wanted to understand whether the difficulty was woven into the mathematical fabric of the problem itself. That question, deceptively simple in its phrasing, ignited an entire discipline. Decades later, the same intellectual current led Blum and his collaborators to create CAPTCHA — a system that turned computational hardness into a tool for distinguishing humans from machines across billions of web interactions every day.
Manuel Blum’s career stretches across more than six decades of theoretical computer science. His work on axiomatic complexity theory earned him the Turing Award in 1995, and his contributions to cryptography, program checking, and human-computation systems have shaped the way we think about what computers can and cannot do. This is the story of a mind that found profound beauty in the limits of computation.
Early Life and the Road to MIT
Manuel Blum was born on April 26, 1938, in Caracas, Venezuela. His parents were Jewish immigrants who had fled Europe, and the household placed a strong emphasis on education and intellectual curiosity. Blum showed an early aptitude for mathematics, but it was engineering that first drew him to the United States. He enrolled at the Massachusetts Institute of Technology, where he earned his Bachelor of Science in Electrical Engineering and Computer Science in 1959, followed by a Master’s degree in Mathematics in 1961.
It was at MIT that Blum encountered the towering figure of Marvin Minsky, one of the founders of artificial intelligence. Blum pursued his doctoral research under Minsky’s supervision, but rather than following the mainstream AI path of building intelligent systems, Blum turned his attention to the theoretical foundations of computation. His 1964 PhD thesis, “A Machine-Independent Theory of the Complexity of Recursive Functions,” laid the groundwork for what would become axiomatic complexity theory — a framework for reasoning about computational difficulty without reference to any specific machine model.
This was a bold intellectual move. Alan Turing had shown that universal computation was possible; Edsger Dijkstra and others were developing practical algorithms and structured programming techniques. Blum, however, wanted to understand the abstract landscape of computational resources — time, space, and everything in between — in a way that transcended hardware and implementation details.
Axiomatic Complexity Theory: The Blum Axioms
The cornerstone of Blum’s early theoretical work is the Blum complexity measure, published in his landmark 1967 paper “A Machine-Independent Theory of the Complexity of Recursive Functions.” The idea was breathtakingly elegant: rather than defining complexity in terms of a specific machine (like a Turing machine counting tape moves), Blum proposed a set of axioms that any reasonable complexity measure must satisfy.
The Two Axioms
Blum’s axiomatic framework rests on two deceptively simple conditions. Given an effective enumeration of partial recursive functions φ₀, φ₁, φ₂, … a complexity measure is a sequence of partial recursive functions Φ₀, Φ₁, Φ₂, … satisfying:
Axiom 1 (Domain Agreement): Φᵢ(x) is defined if and only if φᵢ(x) is defined. In other words, the complexity of a computation is defined exactly when the computation itself halts.
Om 2 (Decidability): The predicate “Φᵢ(x) = t” is decidable. Given a program i, an input x, and a time bound t, we can algorithmically determine whether the complexity of running program i on input x equals exactly t.
From these two axioms alone, Blum derived powerful theorems. The Blum Speedup Theorem showed that there exist problems for which any algorithm can be dramatically sped up — yet no optimal algorithm exists. The Gap Theorem demonstrated that there are arbitrarily large “gaps” in the complexity hierarchy where no problems live. These results revealed that the landscape of computational difficulty is far stranger and more counterintuitive than anyone had imagined.
This work had immediate implications for the broader field. It influenced the development of the P vs NP question and provided theoretical tools that researchers like Donald Knuth drew upon when analyzing algorithms. The idea that complexity could be studied independently of any particular machine model became a foundational principle of theoretical computer science.
Connection to Modern Complexity Classes
While Blum’s axioms operate at a high level of abstraction, they provided the philosophical and mathematical foundation for the concrete complexity classes that dominate modern theory: P, NP, PSPACE, BPP, and dozens of others. The insight that complexity is an intrinsic property of problems — not merely a feature of particular algorithms — remains one of the most important ideas in computer science.
Cryptography and Zero-Knowledge Proofs
By the 1980s, Blum had moved to Carnegie Mellon University, where he joined a remarkable group of theoretical computer scientists and cryptographers. His work took a new direction: applying computational complexity theory to cryptographic protocols.
Blum made fundamental contributions to the theory of pseudorandom number generation. Together with his wife Lenore Blum and Mike Shub, he developed the Blum Blum Shub (BBS) generator in 1986. The BBS generator produces sequences that are provably unpredictable under certain number-theoretic assumptions — specifically, the difficulty of factoring large integers. This was a landmark result because it connected the practical need for randomness in cryptographic systems to the deep theory of computational hardness.
The generator works by iterating the function x_{n+1} = x_n² mod M, where M is a product of two large primes, and outputting the least significant bit at each step. Its security rests on the quadratic residuosity assumption, which is related to the hardness of integer factorization — the same foundational problem that underpins Ron Rivest’s RSA cryptosystem.
Blum also contributed to the development of zero-knowledge proofs, a concept pioneered by Shafi Goldwasser and Silvio Micali (both of whom were Blum’s students at MIT and CMU). Zero-knowledge proofs allow one party to prove knowledge of a secret without revealing the secret itself — a notion that has become central to modern blockchain systems and privacy-preserving computation.
Below is a simplified illustration of how a zero-knowledge proof protocol works, using the classic “graph coloring” example. In this model, a prover demonstrates they possess a valid 3-coloring of a graph without revealing the actual coloring:
"""
Zero-Knowledge Proof: Graph 3-Coloring Protocol (Simplified)
The prover knows a valid 3-coloring of graph G.
In each round, the prover randomly permutes the color labels,
commits to the permuted coloring, and reveals only two adjacent
nodes when challenged — enough to verify validity without
leaking the full coloring.
"""
import random
import hashlib
def commit(value, nonce):
"""Create a cryptographic commitment to a value."""
data = f"{value}:{nonce}".encode()
return hashlib.sha256(data).hexdigest()
def zero_knowledge_round(graph_edges, true_coloring):
"""
One round of the ZK graph-coloring protocol.
graph_edges: list of (u, v) tuples representing edges
true_coloring: dict mapping node -> color (0, 1, or 2)
"""
# Step 1: Prover creates a random permutation of colors
perm = list(range(3))
random.shuffle(perm)
permuted = {node: perm[color] for node, color in true_coloring.items()}
# Step 2: Prover commits to each node's permuted color
nonces = {node: random.randint(0, 2**128) for node in permuted}
commitments = {
node: commit(permuted[node], nonces[node])
for node in permuted
}
# Step 3: Verifier picks a random edge to challenge
edge = random.choice(graph_edges)
u, v = edge
# Step 4: Prover reveals colors and nonces for challenged edge
revealed = {
u: (permuted[u], nonces[u]),
v: (permuted[v], nonces[v])
}
# Step 5: Verifier checks commitments and color inequality
for node in (u, v):
color_val, nonce_val = revealed[node]
expected = commit(color_val, nonce_val)
assert expected == commitments[node], "Commitment mismatch!"
assert revealed[u][0] != revealed[v][0], "Adjacent nodes share color!"
return True # Round passed
# Example usage
edges = [(0,1), (1,2), (2,0), (1,3), (2,3)]
coloring = {0: 0, 1: 1, 2: 2, 3: 0}
# Run 100 rounds — probability of cheating: (1 - 1/|E|)^100
rounds_passed = sum(
zero_knowledge_round(edges, coloring) for _ in range(100)
)
print(f"Passed {rounds_passed}/100 rounds — coloring is valid with high probability")This protocol illustrates the core principle Blum helped establish: computational hardness can be constructive, providing privacy guarantees rather than merely posing obstacles.
Program Checking and Self-Testing
In the late 1980s and early 1990s, Blum introduced another influential concept: program checking. The central question was deceptively simple — if you run a program and it gives you an answer, how do you know the answer is correct? You could write a second program to verify the first, but then who verifies the verifier?
Blum’s solution was the notion of a checker: a program that, given an input and the output of another program, determines whether the output is correct — without solving the problem from scratch. This was a fundamentally different approach from traditional testing or formal verification. Checkers exploit the structure of problems to verify solutions far more efficiently than recomputing them.
This idea had deep practical implications. It influenced the development of probabilistically checkable proofs (PCPs) and laid intellectual groundwork for results like the PCP theorem, which transformed our understanding of approximation algorithms and NP-hardness. The philosophy of program checking — trusting results through efficient verification rather than blind faith in implementation — resonates throughout modern software engineering, from unit testing to task management systems that verify deliverables at each stage of a project pipeline.
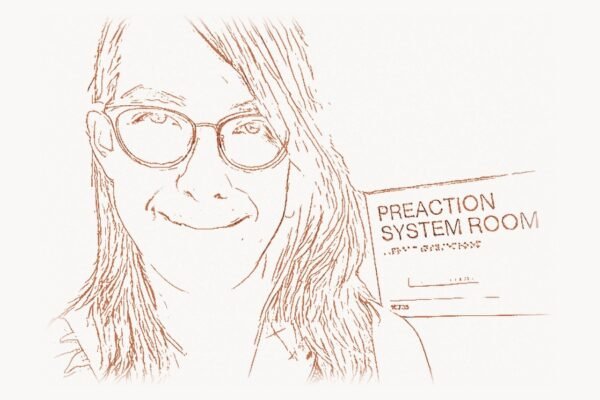
CAPTCHA: Turning Hardness Into a Human Filter
The work for which Manuel Blum is most widely known outside academia emerged around the year 2000 at Carnegie Mellon University. Blum, together with Luis von Ahn, John Langford, and Nicholas Hopper, developed the concept of CAPTCHA — Completely Automated Public Turing test to tell Computers and Humans Apart.
The intellectual roots of CAPTCHA run directly back to Blum’s lifelong preoccupation with computational hardness. The core idea is elegant: find a task that is easy for humans but computationally hard for machines, then use that asymmetry as a gatekeeper. In the original formulation, this meant presenting distorted text that human visual systems could parse but that optical character recognition (OCR) algorithms could not.
The Design Philosophy
CAPTCHA is, at its heart, an application of complexity theory to security. The system relies on a specific kind of computational gap: problems where humans have a cognitive advantage over algorithms. Blum and his team formalized this by defining CAPTCHAs in terms of three properties:
- Easy to generate: The challenge (e.g., distorted text) must be simple for a server to produce algorithmically.
- Easy for humans: A typical human should be able to solve the challenge correctly with high probability.
- Hard for machines: No known algorithm should be able to solve the challenge with significantly better probability than random guessing.
The third property is where Blum’s decades of complexity theory expertise proved essential. The hardness of CAPTCHA was not merely empirical — Blum insisted on grounding it in well-understood computational problems, particularly those related to pattern recognition under adversarial distortion.
A Simple CAPTCHA Verification System
Below is a conceptual implementation of a CAPTCHA generation and verification pipeline, illustrating the core architectural ideas behind the original CMU system:
"""
CAPTCHA Generation and Verification System (Conceptual)
Demonstrates the pipeline: generate distorted challenge,
store expected answer server-side, verify human response.
"""
import hashlib
import random
import string
import time
class CaptchaSystem:
"""
Server-side CAPTCHA management.
In production, distortion would use image transforms:
warping, noise injection, overlapping arcs, variable
kerning — all calibrated to exploit the gap between
human perception and OCR capability.
"""
def __init__(self, secret_key="server_secret"):
self.secret = secret_key
self.active_challenges = {} # token -> (answer, expiry)
def _generate_text(self, length=6):
"""Generate random alphanumeric string, excluding ambiguous chars."""
alphabet = "ABCDEFGHJKLMNPQRSTUVWXYZabcdefghjkmnpqrstuvwxyz23456789"
return ''.join(random.choices(alphabet, k=length))
def _create_token(self, challenge_text):
"""Create a secure token binding challenge to server state."""
timestamp = str(time.time())
raw = f"{self.secret}:{challenge_text}:{timestamp}"
return hashlib.sha256(raw.encode()).hexdigest()[:16]
def generate_challenge(self, ttl_seconds=300):
"""
Generate a new CAPTCHA challenge.
Returns:
token: unique identifier for this challenge
display_text: the text to render as distorted image
In a real system, display_text would be rendered with:
- Random affine transforms per character
- Gaussian and salt-and-pepper noise
- Overlapping bezier curve distractors
- Variable font size, rotation, and spacing
"""
text = self._generate_text()
token = self._create_token(text)
expiry = time.time() + ttl_seconds
self.active_challenges[token] = (text.lower(), expiry)
self._cleanup_expired()
return token, text
def verify(self, token, user_response):
"""
Verify a user's CAPTCHA response.
Returns:
(bool, str): success flag and message
"""
if token not in self.active_challenges:
return False, "Challenge expired or invalid"
expected, expiry = self.active_challenges[token]
# Remove challenge after single attempt (prevent replay)
del self.active_challenges[token]
if time.time() > expiry:
return False, "Challenge expired"
if user_response.lower().strip() == expected:
return True, "Verification passed — human confirmed"
return False, "Incorrect response"
def _cleanup_expired(self):
"""Remove expired challenges to prevent memory leaks."""
now = time.time()
expired = [t for t, (_, exp) in self.active_challenges.items() if now > exp]
for t in expired:
del self.active_challenges[t]
# --- Demonstration ---
captcha = CaptchaSystem()
# Server generates challenge
token, display = captcha.generate_challenge()
print(f"CAPTCHA challenge: '{display}' (token: {token})")
# Human solves it (simulated correct response)
success, msg = captcha.verify(token, display)
print(f"Result: {msg}")
# Replay attack fails — token already consumed
success2, msg2 = captcha.verify(token, display)
print(f"Replay attempt: {msg2}")The real-world impact of CAPTCHA was immediate and enormous. Within a few years of its introduction, CAPTCHA became a ubiquitous feature of the web — protecting email registrations, online polls, e-commerce checkouts, and comment systems from automated abuse. Millions of CAPTCHAs were being solved every day, which led Blum’s student Luis von Ahn to develop reCAPTCHA, a system that channeled that human effort into digitizing books and, later, training machine learning models.
The Blum School: A Legacy of Students
One of Manuel Blum’s most remarkable contributions to computer science is not a theorem or a system but a lineage. His PhD students at UC Berkeley and Carnegie Mellon read like a roster of the field’s most important figures:
- Shafi Goldwasser — Turing Award winner (2012) for foundational work on cryptographic complexity
- Silvio Micali — Turing Award winner (2012) for co-inventing zero-knowledge proofs
- Luis von Ahn — Creator of reCAPTCHA and Duolingo, MacArthur Fellow
- Gary Miller — Developer of the Miller-Rabin primality test
- Umesh Vazirani — Pioneer in quantum computing theory
- Ravindran Kannan — Knuth Prize winner for algorithmic contributions
- Dan Spielman — Nevanlinna Prize winner for work on coding theory and graph algorithms
Blum’s mentoring style was legendary. He was known for posing deceptively simple questions that contained hidden depths, encouraging students to find their own problems rather than assigning topics. This Socratic approach produced independent thinkers who went on to define entire subfields. The fact that two of his students shared the Turing Award for work on zero-knowledge proofs — a concept deeply connected to Blum’s own research on computational hardness — illustrates how his intellectual influence radiated outward through generations.
In professional web development and digital project management, a similar pattern holds: the most impactful leaders are often those who cultivate strong teams and establish frameworks that others can build upon, rather than those who try to do everything themselves.
The Turing Award and Recognition
In 1995, the Association for Computing Machinery awarded Manuel Blum the A.M. Turing Award — computer science’s highest honor — for his contributions to the foundations of computational complexity theory and its applications to cryptography and program checking. The award citation specifically recognized his axiomatic approach to complexity, his work on pseudorandom generation, and his pioneering ideas about program self-testing.
Blum joined the ranks of theoretical computer science luminaries like Alan Turing (the award’s namesake) and Donald Knuth, who had used mathematical rigor to illuminate the deep structure of computation. The Turing Award cemented Blum’s status as one of the most influential theorists in the history of the field, alongside cryptography pioneers like Whitfield Diffie who had similarly transformed abstract theory into practical security infrastructure.
Consciousness and Theoretical Neuroscience
In recent years, Blum has turned his attention to what may be the hardest problem of all: consciousness. Working with his wife Lenore Blum, he has developed a theoretical framework that attempts to model conscious experience using concepts from theoretical computer science — specifically, the theory of computation applied to neural architectures.
The Blums’ model proposes a “Conscious Turing Machine” (CTM) — a formal computational model that incorporates elements like a “stage” (analogous to working memory), “processors” (analogous to specialized brain regions), and “broadcast” mechanisms (inspired by Global Workspace Theory from cognitive science). The model does not claim to solve the hard problem of consciousness, but it provides a rigorous formal framework within which questions about consciousness can be posed and analyzed using the tools of theoretical computer science.
This work represents a fascinating full-circle moment in Blum’s career. He began by asking what makes computational problems hard; he now asks what makes subjective experience computationally possible. In both cases, the approach is the same — strip away implementation details and study the abstract structure of the phenomenon.
Lasting Impact on Computer Science
Manuel Blum’s influence on modern computer science operates on multiple levels:
Theoretical Foundations
His axiomatic complexity theory established that computational difficulty is an intrinsic property of problems, not an artifact of particular machines or algorithms. This insight is foundational to the entire field of computational complexity, including the P vs NP question — arguably the most important open problem in mathematics and computer science.
Cryptographic Security
The Blum Blum Shub generator and his contributions to zero-knowledge proofs helped build the theoretical infrastructure for modern cryptography. Every time you conduct a secure transaction online, you benefit from the intellectual tradition that Blum helped establish — the same tradition that produced RSA encryption and public-key cryptography.
Human-Computer Interaction
CAPTCHA transformed the abstract notion of computational hardness into a practical tool used by billions of people. It is perhaps the most visible application of complexity theory in everyday life, and it spawned an entire subfield of human-computation systems.
Academic Lineage
Through his students and their students, Blum’s intellectual DNA runs through a vast network of researchers, institutions, and companies. His mentoring philosophy — emphasize foundational thinking, encourage independence, choose hard problems — continues to shape how theoretical computer science is practiced and taught.
Frequently Asked Questions
What did Manuel Blum receive the Turing Award for?
Manuel Blum received the 1995 A.M. Turing Award for his foundational contributions to computational complexity theory. The award recognized his axiomatic approach to defining complexity measures (the Blum axioms), his work on pseudorandom number generation and cryptographic protocols, and his pioneering research on program checking and self-testing. These contributions established theoretical frameworks that remain central to computer science, cryptography, and the study of what makes computational problems inherently difficult.
How does CAPTCHA relate to computational complexity theory?
CAPTCHA is a direct application of computational complexity theory to web security. It exploits a specific complexity gap — tasks that are computationally easy for humans (recognizing distorted text, identifying objects in images) but hard for algorithms. Manuel Blum’s decades of research on what makes problems inherently difficult provided the theoretical foundation for designing challenges where human cognitive abilities reliably outperform automated solvers. The system essentially converts abstract hardness results into a practical mechanism for distinguishing humans from bots.
What is the Blum Blum Shub pseudorandom number generator?
The Blum Blum Shub (BBS) generator is a cryptographically secure pseudorandom number generator developed by Lenore Blum, Manuel Blum, and Michael Shub in 1986. It works by iterating the formula x_{n+1} = x_n² mod M, where M is a product of two large primes, and outputs the least significant bit of each iteration. Its security is provably reducible to the difficulty of the integer factorization problem — meaning that breaking BBS is at least as hard as factoring large numbers. This made BBS one of the first pseudorandom generators with a formal security proof based on a well-studied computational assumption.
Who were Manuel Blum’s most notable students?
Manuel Blum advised an extraordinary group of PhD students who went on to reshape computer science. His most notable students include Shafi Goldwasser and Silvio Micali, who shared the 2012 Turing Award for their work on zero-knowledge proofs and probabilistic encryption; Luis von Ahn, who created reCAPTCHA and founded Duolingo; Gary Miller, who developed the Miller-Rabin primality test; Umesh Vazirani, a pioneer in quantum computing theory; and Dan Spielman, who won the Nevanlinna Prize for contributions to coding theory and algorithms.
What is Manuel Blum working on now?
In recent years, Manuel Blum has been working on a theoretical model of consciousness with his wife Lenore Blum. Their “Conscious Turing Machine” (CTM) framework applies concepts from theoretical computer science — including computation, information broadcasting, and formal modeling — to the study of conscious experience. The model draws on Global Workspace Theory from cognitive science and attempts to formalize aspects of consciousness using rigorous computational abstractions, representing a fascinating intersection of complexity theory and neuroscience.