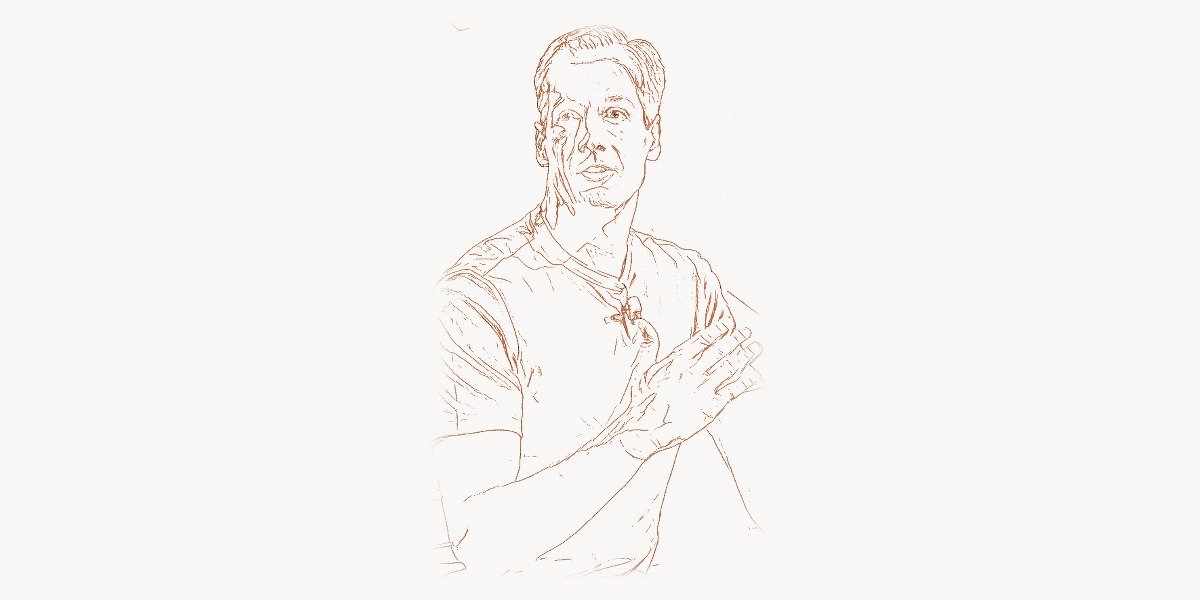
In the world of operating systems, few people have ever achieved the kind of deep, almost surgical understanding of Windows internals that Mark Russinovich has demonstrated throughout his career. While most developers work at the application layer — building software that sits comfortably on top of the OS — Russinovich dove into the kernel, the drivers, the registry, and the undocumented corners of the Windows architecture that even Microsoft’s own engineers sometimes struggled to explain. His creation of the Sysinternals suite of tools didn’t just help millions of IT professionals diagnose and fix problems; it fundamentally changed the relationship between Microsoft and its technical community. And when he famously used his own tools to expose Sony BMG’s rootkit scandal in 2005, he proved that deep systems knowledge isn’t just an academic exercise — it’s a form of power that can hold even the largest corporations accountable. Today, as CTO of Microsoft Azure, Russinovich applies that same relentless curiosity and precision to one of the largest cloud platforms on the planet, overseeing an infrastructure that generates more than $60 billion in annual revenue.
Early Life and Path to Technology
Mark Eugene Russinovich was born on December 22, 1966, and grew up during a time when personal computing was transitioning from a hobbyist curiosity into a mainstream force. His early fascination with computers led him to pursue a rigorous academic path that would set the foundation for everything that followed. He earned his Bachelor’s degree in computer engineering, but it was his doctoral work at Carnegie Mellon University — one of the most prestigious computer science programs in the world — that truly shaped his career trajectory.
At Carnegie Mellon, Russinovich immersed himself in operating systems research. His PhD work focused on operating system design and performance, giving him the kind of low-level systems expertise that few programmers ever develop. This wasn’t the era of high-level abstractions and managed runtimes — this was the world of C programming and Unix-style systems thinking pioneered by Dennis Ritchie and Ken Thompson, where understanding memory management, process scheduling, and kernel architecture was essential. The theoretical foundations laid by researchers like Edsger Dijkstra in algorithms and structured programming influenced the rigorous approach Russinovich would bring to systems analysis.
After completing his PhD, Russinovich could have followed a conventional academic path. Instead, he found himself drawn to a practical problem that would define his career: the Windows NT operating system was growing in complexity and importance, yet the tools available for understanding its behavior were woefully inadequate. Windows was becoming the dominant platform for enterprise computing, but its internals remained largely opaque to the developers and administrators who needed to work with it daily. This gap between Windows’ growing complexity and the community’s ability to understand it became the problem Russinovich was uniquely positioned to solve.
The Breakthrough: Creating Sysinternals
In 1996, Mark Russinovich and his colleague Bryce Cogswell launched a website called NTInternals.com — later renamed to Sysinternals.com — that would become one of the most important resources in the history of Windows system administration. What started as a collection of free utilities for examining Windows internals grew into a comprehensive toolkit that fundamentally changed how professionals diagnosed, monitored, and secured Windows systems.
The Technical Innovation
The genius of Sysinternals wasn’t any single tool — it was the philosophy behind the entire collection. Each utility was designed to expose what Windows was actually doing under the hood, bypassing the sanitized view that standard tools provided. Process Explorer replaced the basic Task Manager with a tool that showed the complete hierarchy of processes, their loaded DLLs, open handles, network connections, and resource consumption. Process Monitor (originally two separate tools — Filemon and Regmon) captured every file system operation, registry access, and network event in real time, creating a comprehensive audit trail of system activity.
Consider how Process Explorer reveals system activity at a level that the built-in Task Manager never could:
# Using Sysinternals tools from the command line
# PsExec - execute processes remotely (revolutionary for its time)
PsExec.exe \\remote-server -u admin -p password cmd.exe
# Autoruns command-line version - show ALL auto-start entries
autorunsc.exe -a * -c -h -s -v -vt | ConvertFrom-Csv |
Where-Object { $_.'Image Path' -ne '' -and $_.'Enabled' -eq 'enabled' } |
Select-Object 'Entry Location', 'Image Path', 'Launch String' |
Format-Table -AutoSize
# Sigcheck - verify digital signatures and check VirusTotal
sigcheck.exe -u -e C:\Windows\System32\*.dll |
Select-String "Unsigned"
# Handle - find which process has a file locked
handle.exe "database.mdf" -accepteula
# ListDLLs - show DLLs loaded by a process (useful for DLL hijacking detection)
listdlls.exe -u | Select-String "unsigned"What made these tools revolutionary was their ability to hook into undocumented Windows APIs and kernel interfaces. Russinovich reverse-engineered significant portions of the Windows kernel to understand how the OS managed processes, memory, the file system, and the registry. This wasn’t just clever programming — it required the kind of deep systems understanding that comes from years of studying operating system theory and then applying it to a real, production kernel with all its quirks and undocumented behaviors.
The tools themselves were written primarily in C and C++, leveraging the Windows API at its lowest levels. Russinovich’s code frequently used Native API calls — the undocumented layer between the Win32 API and the kernel — to extract information that was simply invisible through standard interfaces. Here’s a simplified example of the kind of low-level approach his tools employed:
/* Simplified example of querying system process information
using the Native API — the approach Sysinternals tools pioneered */
#include <windows.h>
#include <winternl.h>
typedef NTSTATUS (NTAPI *pNtQuerySystemInformation)(
SYSTEM_INFORMATION_CLASS SystemInformationClass,
PVOID SystemInformation,
ULONG SystemInformationLength,
PULONG ReturnLength
);
void EnumerateProcesses() {
HMODULE hNtdll = GetModuleHandleW(L"ntdll.dll");
pNtQuerySystemInformation NtQuerySystemInfo =
(pNtQuerySystemInformation)GetProcAddress(
hNtdll, "NtQuerySystemInformation"
);
ULONG bufferSize = 1024 * 1024; // 1MB initial buffer
PVOID buffer = VirtualAlloc(NULL, bufferSize,
MEM_COMMIT, PAGE_READWRITE);
/* SystemProcessInformation (5) returns detailed info about
every running process — far more than EnumProcesses() */
NTSTATUS status = NtQuerySystemInfo(
SystemProcessInformation, buffer, bufferSize, NULL
);
if (NT_SUCCESS(status)) {
PSYSTEM_PROCESS_INFORMATION procInfo =
(PSYSTEM_PROCESS_INFORMATION)buffer;
while (TRUE) {
wprintf(L"PID: %lu Threads: %lu Name: %wZ\n",
HandleToULong(procInfo->UniqueProcessId),
procInfo->NumberOfThreads,
&procInfo->ImageName);
if (procInfo->NextEntryOffset == 0) break;
procInfo = (PSYSTEM_PROCESS_INFORMATION)
((PBYTE)procInfo + procInfo->NextEntryOffset);
}
}
VirtualFree(buffer, 0, MEM_RELEASE);
}This approach of using native, undocumented APIs to surface hidden system information was both technically impressive and practically invaluable. It gave system administrators and security professionals visibility into Windows behavior that was previously accessible only to Microsoft’s own kernel developers.
Why It Mattered
Before Sysinternals, Windows troubleshooting was often a frustrating exercise in guesswork. When a server was slow, a process was hanging, or a system was behaving erratically, administrators had limited visibility into what was actually happening. The built-in tools — Task Manager, Event Viewer, Performance Monitor — provided only a surface-level view. Sysinternals changed this by giving every IT professional access to kernel-level diagnostic capabilities.
The impact was enormous. Process Explorer became the de facto replacement for Task Manager across the industry. Autoruns became the go-to tool for analyzing startup items and identifying malware persistence mechanisms. TCPView provided real-time network connection monitoring. PsExec enabled remote administration before PowerShell remoting existed. These weren’t just useful utilities — they became essential infrastructure for anyone managing Windows systems at scale. Enterprise teams managing complex infrastructures — the kind of environments where tools like Taskee now help coordinate technical operations — relied on Sysinternals daily for incident response and system diagnostics.
The tools were also entirely free, which was crucial. Russinovich and Cogswell could have built a commercial product and charged enterprise prices for their toolkit. Instead, they made everything available for free download, building an enormous community of users and establishing themselves as the definitive authorities on Windows internals. This decision to give away tools that had obvious commercial value was reminiscent of the open-source philosophy championed by Linus Torvalds with Linux and Git — the idea that making powerful tools freely available creates more value than restricting access ever could.
The Sony BMG Rootkit Scandal
On October 31, 2005, Russinovich published a blog post that would send shockwaves through the technology industry and beyond. While testing a new version of one of his Sysinternals utilities — RootkitRevealer — on his own computer, he discovered a rootkit. But this wasn’t malware from some underground hacker group. It was software deliberately installed by Sony BMG as part of their digital rights management (DRM) system on music CDs.
The rootkit, developed by a company called First 4 Internet and included on millions of Sony BMG music CDs, used sophisticated kernel-level techniques to hide itself from the user. It installed a filter driver that intercepted all directory listing calls, hiding any file or folder that started with the prefix “$sys$”. It also installed a background service that communicated with Sony’s servers, transmitting information about what music was being played. Worse, because the rootkit’s cloaking mechanism hid anything with the “$sys$” prefix, malware authors quickly realized they could use the same prefix to hide their own malicious software.
Russinovich’s discovery and detailed public analysis — complete with technical evidence gathered using his own tools — transformed what could have been a quiet technical finding into a major international scandal. Sony BMG was forced to recall millions of CDs. Multiple class-action lawsuits were filed. The Federal Trade Commission and several state attorneys general took action. The incident became a landmark case in the debate over digital rights management and corporate overreach, and it demonstrated the critical importance of the kind of deep systems analysis that Russinovich had spent years enabling.
The broader lesson was that operating system transparency isn’t just a technical nicety — it’s a fundamental requirement for security and trust in computing. This philosophy echoes the arguments that Andrew Tanenbaum made about operating system design and the importance of understanding what software is actually running on your machine.
Windows Internals: The Definitive Reference
Alongside his tool development, Russinovich became co-author of what many consider the definitive technical reference on the Windows operating system: “Windows Internals.” Originally written by Helen Custer and later continued by David Solomon, the book became a collaboration between Solomon and Russinovich, who brought his unparalleled practical knowledge of Windows kernel behavior to the project.
The “Windows Internals” books are not casual reading. They are deep technical references that cover process management, memory management, the I/O system, security mechanisms, networking internals, and virtually every other aspect of the Windows kernel and executive. For Windows kernel developers, security researchers, and advanced system administrators, these books are considered essential reading — the equivalent of what Brian Kernighan‘s works represent for the C programming language and Unix environment.
What makes the books particularly valuable is that they don’t just describe how Windows works in theory — they explain the actual implementation details, complete with data structures, algorithms, and the kinds of insights that can only come from someone who has spent years reverse-engineering and testing the real system. In the tradition of Bjarne Stroustrup, who documented C++ with the authority of its creator, Russinovich wrote about Windows internals with the authority of someone who arguably understood the system better than most people who had actually built it.
Microsoft Azure and Cloud Leadership
In 2006, Microsoft acquired Sysinternals, and Russinovich joined the company as a Technical Fellow — one of the highest technical positions in Microsoft’s engineering hierarchy. While many feared that the acquisition would lead to the tools being commercialized or abandoned, Russinovich ensured they remained free and continued to be actively developed. The Sysinternals suite is still freely available on Microsoft’s website and continues to be widely used.
But Russinovich’s role at Microsoft quickly expanded far beyond Sysinternals. He became the Chief Technology Officer of Microsoft Azure, taking on responsibility for the technical direction of Microsoft’s cloud computing platform. This was not a ceremonial appointment — Azure was in its early stages and needed exactly the kind of deep systems expertise that Russinovich possessed. Building a hyperscale cloud platform involves many of the same challenges he had been working on for years: process isolation, resource management, security boundaries, and the ability to diagnose problems in enormously complex distributed systems.
Under Russinovich’s technical leadership, Azure grew from a relatively small player in the cloud market into a platform generating over $60 billion annually, competing directly with Amazon Web Services and Google Cloud. The platform now spans hundreds of data centers across the globe, runs millions of virtual machines, and supports everything from small web applications to the world’s largest enterprise workloads. Managing this kind of complexity demands the same networking fundamentals that Vint Cerf pioneered with TCP/IP, scaled to an almost incomprehensible degree.
Russinovich’s influence on Azure extends to its approach to confidential computing, where virtual machines can run in encrypted enclaves that even the cloud provider cannot inspect. This focus on security and trust boundaries is a natural extension of his career-long work on system transparency and his experience exposing the Sony rootkit — the principle that users should always be able to understand and verify what software is doing on their systems applies equally to cloud environments.
The Techno-Thriller Novelist
In a surprising but fitting creative outlet, Russinovich has also written three techno-thriller novels: “Zero Day” (2011), “Trojan Horse” (2012), and “Rogue Code” (2014). These books draw directly on his deep technical knowledge, featuring realistic cybersecurity scenarios involving malware, infrastructure attacks, and digital espionage. Unlike many tech-themed thrillers that get the details wrong, Russinovich’s novels are praised for their technical accuracy — hardly surprising given that the author has spent decades understanding exactly how systems can be compromised.
The novels serve as an interesting bridge between Russinovich’s technical work and public awareness of cybersecurity issues. They explore scenarios — critical infrastructure attacks, financial system manipulation, nation-state cyber operations — that have become increasingly relevant in the years since they were published. In many ways, the books are a continuation of the same mission that drove the Sony rootkit discovery: making the public aware of the real security challenges that exist in our increasingly connected world.
Philosophy and Engineering Approach
Mark Russinovich’s career reveals a consistent set of engineering principles that have guided his work from Sysinternals to Azure. His approach stands as a model for how deep technical expertise combined with a commitment to transparency can create lasting impact. For engineers and technical leaders building products today — whether using comprehensive development platforms like Toimi or working directly at the system level — Russinovich’s principles offer valuable guidance.
Key Principles
Transparency Above All. The central theme of Russinovich’s entire career is that systems should be observable and understandable. Whether it’s creating tools that expose what Windows is doing, writing books that explain kernel internals, or discovering hidden rootkits, his work consistently pushes toward giving users and administrators complete visibility into the systems they depend on. This principle is especially critical in the cloud era, where the temptation to treat infrastructure as an opaque black box is even greater.
Go Deeper Than the Documentation. Russinovich built his reputation by understanding systems at a level that went far beyond official documentation. He reverse-engineered undocumented APIs, mapped kernel data structures, and explored behavior that Microsoft itself hadn’t fully documented. This willingness to go beyond the official story — to understand not just what a system is supposed to do but what it actually does — is what made his tools and his analysis so valuable. It echoes the approach of systems programmers in the Unix tradition, like Rob Pike, who insisted on understanding the full stack from hardware to application.
Give Tools Away. By making Sysinternals free, Russinovich built a community and established trust that no amount of marketing could have achieved. The tools became industry standards precisely because there was no barrier to adoption. This approach created a positive feedback loop: widespread use led to bug reports and feature requests, which led to better tools, which led to even wider adoption.
Security Requires Courage. The Sony rootkit discovery wasn’t just a technical achievement — it required the willingness to publicly challenge a major corporation with detailed evidence of wrongdoing. Russinovich could have reported it quietly or chosen not to get involved. Instead, he published a detailed technical analysis that made the issue impossible to ignore. This principle — that security research carries a responsibility to the public — has influenced the entire field of responsible disclosure.
Scale Demands Fundamentals. Moving from desktop utilities to managing one of the world’s largest cloud platforms might seem like a radical change, but it’s fundamentally about the same thing: understanding complex systems at a deep level. The kernel-level thinking that made Sysinternals possible is exactly the kind of thinking required to architect a hyperscale cloud platform. The lesson is that deep fundamentals — the kind taught in rigorous computer science programs and embodied in the work of pioneers like Alan Turing — never become obsolete, even as the scale changes dramatically.
Legacy and Modern Relevance
Mark Russinovich’s legacy operates on multiple levels. Most immediately, the Sysinternals tools remain in active use more than 25 years after their creation. They are still freely available, still regularly updated, and still considered essential by Windows system administrators and security professionals worldwide. Process Explorer, Process Monitor, and Autoruns are among the first tools that incident responders reach for when investigating a compromised system.
At a broader level, Russinovich helped establish the principle that operating system transparency is not optional — it’s a requirement for security and trust. Before Sysinternals, the idea that anyone outside of Microsoft could build tools that provided better visibility into Windows than Microsoft’s own offerings was almost unthinkable. After Sysinternals, it became clear that the community’s ability to inspect, analyze, and understand operating system behavior was essential to the entire ecosystem’s health.
His transition to Azure CTO demonstrates something important about career evolution in technology: deep expertise doesn’t have to be narrow. The same skills that made Russinovich the world’s foremost Windows internals expert — rigorous analysis, comfort with complexity, ability to debug systems at the lowest level — translated directly to the challenge of building and running a hyperscale cloud platform. In an industry that often valorizes breadth over depth, Russinovich’s career is a powerful argument for the value of going deep.
The languages and systems that Russinovich has worked with throughout his career reflect the evolution of systems programming itself. From the C language foundations established by Ritchie and Thompson, through the C++ systems code that powers much of Windows, to the modern systems languages like Rust that Azure now increasingly adopts for security-critical components — Russinovich has navigated each transition while maintaining his core focus on understanding what systems actually do at their lowest level.
Perhaps most importantly, Russinovich embodies the idea that technical excellence and public service are not mutually exclusive. His tools helped millions of people. His rootkit discovery protected millions of consumers. His books educated a generation of systems programmers. And his leadership at Azure provides the infrastructure that powers a significant fraction of the world’s digital economy. In each case, the common thread is a commitment to understanding systems deeply and using that understanding for the benefit of the broader community.
Key Facts
- Full name: Mark Eugene Russinovich
- Born: December 22, 1966
- Education: PhD in Computer Engineering from Carnegie Mellon University
- Co-founded: Sysinternals (originally NTInternals.com) in 1996 with Bryce Cogswell
- Key tools created: Process Explorer, Process Monitor (Filemon + Regmon), Autoruns, TCPView, PsExec, PsTools suite, RootkitRevealer, Sigcheck, and dozens more
- Famous discovery: Exposed the Sony BMG rootkit in October 2005 using RootkitRevealer
- Books: Co-author of “Windows Internals” (with David Solomon, originally by Helen Custer) — the definitive technical reference on Windows OS architecture
- Novels: “Zero Day” (2011), “Trojan Horse” (2012), “Rogue Code” (2014) — cybersecurity techno-thrillers
- Microsoft: Joined in 2006 when Microsoft acquired Sysinternals; holds the rank of Technical Fellow
- Current role: Chief Technology Officer of Microsoft Azure
- Azure scale: Under his technical leadership, Azure grew to a $60+ billion annual revenue platform
- Awards: Multiple Microsoft Gold Star awards; widely regarded as one of the foremost Windows internals experts in the world
Frequently Asked Questions
What is Sysinternals and why is it important for Windows administration?
Sysinternals is a collection of free system utilities created by Mark Russinovich and Bryce Cogswell starting in 1996. The suite includes tools like Process Explorer (an advanced task manager), Process Monitor (which tracks file system, registry, and process activity in real time), Autoruns (which shows every auto-start program on the system), and dozens of other specialized utilities. These tools provide visibility into Windows internals that goes far beyond what the operating system’s built-in tools offer. They are widely considered essential for Windows system administration, troubleshooting, and security analysis, used by IT professionals, incident responders, and malware analysts worldwide. Microsoft acquired Sysinternals in 2006 but kept all the tools free, and they continue to be actively maintained and updated.
How did Mark Russinovich discover the Sony BMG rootkit?
In October 2005, Russinovich was testing his RootkitRevealer tool — a Sysinternals utility designed to detect rootkit-like behavior on Windows systems — when it flagged suspicious hidden files on his own personal computer. Upon investigation, he traced the rootkit to a Sony BMG music CD he had recently played. The CD had silently installed digital rights management software that used kernel-level cloaking techniques to hide its presence, intercepting system calls to make its files and registry entries invisible to the user. Russinovich published a detailed technical analysis on his blog, documenting exactly how the rootkit worked and the security risks it created. The post triggered a massive public backlash, leading to class-action lawsuits, government investigations, and a recall of millions of CDs — becoming one of the most significant digital rights management controversies in history.
What does Mark Russinovich do as CTO of Microsoft Azure?
As Chief Technology Officer of Microsoft Azure, Russinovich is responsible for the overall technical strategy and architecture of Microsoft’s cloud computing platform. This includes overseeing the design of Azure’s infrastructure — the global network of data centers, the virtualization layer, the networking stack, and the security architecture that allows millions of customers to run workloads in a shared environment with strong isolation guarantees. He has been particularly focused on advancing confidential computing, which uses hardware-based encryption to protect data even while it’s being processed, ensuring that neither other tenants nor the cloud provider itself can access customer data. Under his technical leadership, Azure has grown into one of the world’s largest cloud platforms, competing with Amazon Web Services and serving enterprise customers across every industry. His deep background in operating system internals makes him uniquely qualified for this role, as building a hyperscale cloud platform is fundamentally an exercise in large-scale systems engineering.