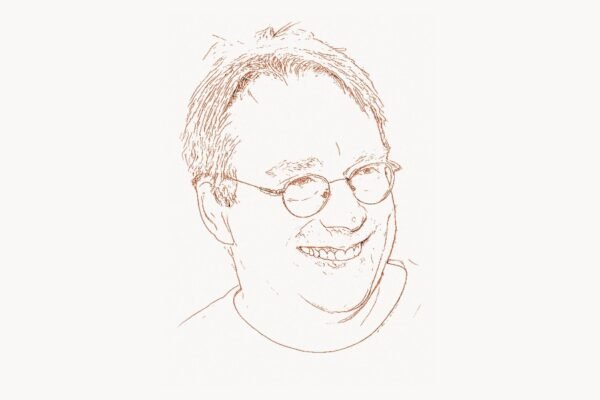
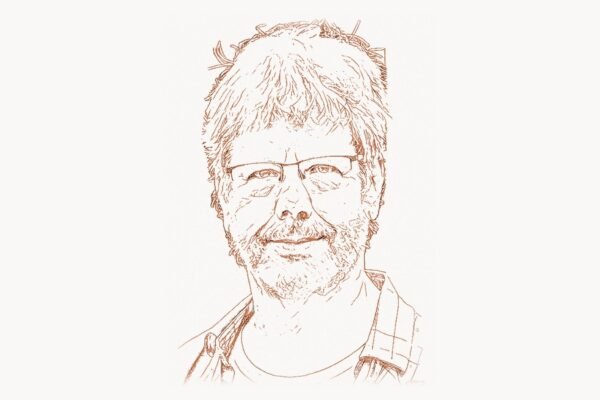
In 2014, a solo developer released a command-line tool that let engineers describe their entire cloud infrastructure in a single text file and deploy it with one command. That tool was Terraform, and that developer was Mitchell Hashimoto. Within five years, Terraform became the de facto standard for infrastructure-as-code, used by tens of thousands of companies from startups to Fortune 500 enterprises. But Terraform was only one piece of a larger vision. Hashimoto co-founded HashiCorp and personally created or co-created six major open-source tools — Vagrant, Packer, Terraform, Vault, Consul, and Nomad — each addressing a different layer of the infrastructure stack, and each becoming a category leader in its domain. Before HashiCorp, provisioning cloud infrastructure meant clicking through web consoles or writing fragile, provider-specific scripts. After HashiCorp, infrastructure became software — versionable, testable, reviewable, and reproducible. In 2023, after a decade of building infrastructure tooling, Hashimoto stepped away from HashiCorp to pursue a completely different passion project: building Ghostty, a high-performance terminal emulator written in Zig. The shift from cloud infrastructure to terminal rendering might seem abrupt, but it reveals the consistent thread in Hashimoto’s career: an obsession with the tools that developers use every day, and a belief that those tools can always be made fundamentally better.
Early Life and Education
Mitchell Hashimoto grew up in the United States and developed an interest in programming at an early age. He studied computer science at the University of Washington, where he was drawn to systems programming and the practical challenges of building reliable software infrastructure. During his university years, Hashimoto was already deeply involved in the open-source community, contributing to Ruby projects and building developer tools in his spare time.
His first major open-source project, Vagrant, began as a side project in 2010 while he was still in college. The problem Vagrant solved was immediately recognizable to any developer who had ever heard the phrase “it works on my machine.” Setting up a development environment — installing the right database version, configuring the correct runtime, matching production settings — was a tedious, error-prone process that consumed hours at the start of every project. Vagrant automated the creation of reproducible virtual machine environments using a simple Ruby-based configuration file called a Vagrantfile. A developer could run vagrant up and have a fully configured virtual machine running in minutes, identical to every other developer’s environment on the team.
Vagrant’s success was both a product of Hashimoto’s technical ability and his instinct for identifying pain points that developers tolerated without realizing they could be solved. This pattern — observing a manual, fragile process that the industry had accepted as normal, then building an opinionated tool that automated it through a declarative configuration file — would define his entire career.
The Infrastructure-as-Code Breakthrough
Technical Innovation
Terraform, released in 2014, was Hashimoto’s most consequential technical contribution. The core idea was deceptively simple: describe your desired infrastructure state in a configuration file, and let the tool figure out how to reach that state. But the implementation required solving several hard problems simultaneously.
Terraform introduced the HashiCorp Configuration Language (HCL), a declarative language purpose-built for describing infrastructure. Unlike JSON or YAML, HCL was designed to be both human-readable and machine-parseable, with support for variables, functions, conditionals, and loops. A Terraform configuration could describe an entire cloud deployment — virtual machines, networks, databases, DNS records, load balancers, security policies — in a single file or a set of modules:
# Terraform configuration — declaring cloud infrastructure as code
# This creates an AWS VPC with a public subnet and an EC2 instance
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.0"
}
}
}
provider "aws" {
region = "us-east-1"
}
resource "aws_vpc" "main" {
cidr_block = "10.0.0.0/16"
enable_dns_hostnames = true
tags = {
Name = "production-vpc"
Environment = "production"
ManagedBy = "terraform"
}
}
resource "aws_subnet" "public" {
vpc_id = aws_vpc.main.id
cidr_block = "10.0.1.0/24"
map_public_ip_on_launch = true
availability_zone = "us-east-1a"
tags = {
Name = "public-subnet-1a"
}
}
resource "aws_instance" "web_server" {
ami = "ami-0c55b159cbfafe1f0"
instance_type = "t3.medium"
subnet_id = aws_subnet.public.id
root_block_device {
volume_size = 30
volume_type = "gp3"
}
tags = {
Name = "web-server-production"
Role = "web"
}
}The critical architectural innovation was Terraform’s provider model. Rather than building direct integrations with every cloud platform, Hashimoto designed Terraform as a core engine that communicated with external provider plugins through a standardized RPC interface. Each provider — AWS, Google Cloud, Azure, DigitalOcean, Cloudflare, and hundreds of others — was a separate binary that implemented a defined set of operations: plan, apply, and destroy for each resource type. This design decision had enormous consequences. It meant that anyone could write a Terraform provider, and the ecosystem of supported infrastructure grew organically. By 2026, the Terraform registry lists over 4,000 providers, covering not just cloud platforms but SaaS services, databases, monitoring systems, DNS providers, and even physical hardware.
Terraform’s execution model was equally important. When a developer ran terraform plan, the tool compared the desired state described in the configuration files against the actual state of the deployed infrastructure (stored in a state file) and computed a precise execution plan: which resources needed to be created, modified, or destroyed. The developer could review this plan before applying it. This plan-then-apply workflow brought the rigor of code review to infrastructure changes — a team could review a Terraform plan the same way they reviewed a pull request, understanding exactly what would change before anything was modified in production.
The second code example shows how Terraform modules enable reusable infrastructure patterns — a concept that brought software engineering’s principle of modularity to cloud provisioning:
# Reusable Terraform module for a web application stack
# modules/web-app/main.tf
variable "app_name" {
type = string
description = "Name of the application"
}
variable "environment" {
type = string
default = "staging"
}
variable "instance_count" {
type = number
default = 2
}
resource "aws_lb" "app" {
name = "${var.app_name}-${var.environment}-lb"
internal = false
load_balancer_type = "application"
subnets = var.subnet_ids
tags = {
Application = var.app_name
Environment = var.environment
}
}
resource "aws_instance" "app" {
count = var.instance_count
ami = var.ami_id
instance_type = "t3.small"
subnet_id = var.subnet_ids[count.index % length(var.subnet_ids)]
user_data = templatefile("${path.module}/scripts/init.sh", {
app_name = var.app_name
environment = var.environment
})
tags = {
Name = "${var.app_name}-${var.environment}-${count.index}"
}
}
# Using the module in a root configuration
module "production_api" {
source = "./modules/web-app"
app_name = "payments-api"
environment = "production"
instance_count = 4
ami_id = "ami-0c55b159cbfafe1f0"
subnet_ids = aws_subnet.private[*].id
}State management was another area where Terraform broke new ground. The tool maintained a state file that recorded the mapping between resources declared in configuration and actual resources deployed in the cloud. This state file served as Terraform’s source of truth about what it had created, enabling it to detect drift (when someone modified infrastructure outside of Terraform) and to compute minimal change sets. Remote state backends — S3, Google Cloud Storage, Terraform Cloud — allowed teams to share state safely, with locking mechanisms to prevent concurrent modifications.
Why It Mattered
Before Terraform, cloud infrastructure provisioning was a landscape of fragmented, provider-specific tools. AWS had CloudFormation. Google Cloud had Deployment Manager. Azure had ARM templates. Each used a different syntax, a different execution model, and different concepts. An organization using multiple cloud providers — which became increasingly common through the 2010s — had to maintain expertise in multiple provisioning systems with no shared abstractions.
Terraform unified this fragmented landscape under a single tool and a single language. An engineer who learned HCL and Terraform’s resource model could provision infrastructure on any supported platform without learning a new tool. Multi-cloud deployments, which had been operationally expensive, became tractable. More importantly, Terraform brought software engineering practices — version control, code review, testing, modularity — to infrastructure management. Infrastructure configurations could be stored in Git alongside application code, reviewed through pull requests, tested with automated pipelines, and composed from reusable modules. This was the real meaning of “infrastructure-as-code”: not just that infrastructure was described in text files, but that it was subject to the same engineering discipline as application code.
The impact on the industry was transformational. DevOps teams adopted Terraform as their primary provisioning tool. Cloud certifications began including Terraform knowledge. A cottage industry of Terraform modules, best practices guides, and consulting firms emerged. HashiCorp itself grew from a two-person company in 2012 to a publicly traded corporation (IPO in December 2021) valued at billions of dollars, with Terraform as its flagship product. The concept of infrastructure-as-code, which Terraform did more than any other tool to popularize, became a foundational practice in modern software engineering — as fundamental as version control or continuous integration. Much as Solomon Hykes revolutionized application packaging with Docker, Hashimoto revolutionized how those containerized applications were actually deployed and managed in the cloud.
Other Major Contributions
While Terraform was Hashimoto’s most widely adopted tool, his broader achievement was creating an integrated suite of infrastructure tools that addressed every major layer of the operations stack. Each tool followed the same design philosophy: a single binary, a declarative configuration language, a clear operational workflow, and a focus on one specific problem.
Vagrant (2010) was Hashimoto’s first major project and the one that established his reputation. By automating the creation of development environments through simple configuration files, Vagrant eliminated the “works on my machine” problem for thousands of development teams. Vagrant’s Vagrantfile became the template for how developers expected tools to work: declare what you want, run a single command, and let the tool handle the details. Vagrant was a direct precursor to Docker’s approach to environment isolation — indeed, many teams migrated from Vagrant to Docker when containerization replaced full virtual machines for development environments. Vagrant proved that developers would eagerly adopt infrastructure tools if those tools were designed with good user experience as a priority.
Packer (2013) solved the machine image problem. Before Packer, creating a server image — an AMI for AWS, a VM image for Google Cloud, a box for Vagrant — required manual steps: launching a base image, installing software, configuring settings, and snapshotting the result. This process was slow, non-reproducible, and provider-specific. Packer automated image creation through a JSON (later HCL) configuration file that specified a base image, a set of provisioning steps (shell scripts, Ansible playbooks, Chef recipes), and target platforms. A single Packer configuration could produce identical images for multiple clouds simultaneously, ensuring consistency across environments.
Consul (2014) addressed service discovery and configuration in distributed systems. As applications moved from monolithic architectures to microservices, the question of how services found each other became critical. Consul provided a distributed, highly available service registry with built-in health checking, key-value storage, and a service mesh capability for securing service-to-service communication with mutual TLS. Consul’s gossip protocol (based on the SWIM algorithm) allowed it to scale to thousands of nodes while maintaining eventual consistency — a design choice that reflected Hashimoto’s pragmatic approach to distributed systems.
Vault (2015) tackled secrets management — one of the most persistently difficult problems in operations. Applications need access to database passwords, API keys, TLS certificates, and encryption keys, but storing these secrets in configuration files, environment variables, or version control is a security disaster. Vault provided a centralized secrets management system with dynamic secret generation (creating short-lived database credentials on demand), automatic key rotation, audit logging, and pluggable authentication backends. Vault became the industry standard for secrets management, adopted by organizations from startups to banks, and its design influenced how the entire industry thinks about credential lifecycle management. For development teams managing complex infrastructure alongside application code, platforms like Taskee help coordinate the operational workflows that tools like Vault integrate into.
Nomad (2015) was HashiCorp’s container orchestration platform — a direct competitor to Kubernetes. Where Kubernetes aimed for comprehensive functionality, Nomad focused on simplicity and operational ease. Nomad was a single binary that could schedule not just Docker containers but also raw executables, Java applications, and batch jobs. It used the same declarative HCL configuration as Terraform, reducing the learning curve for teams already in the HashiCorp ecosystem. Nomad never achieved Kubernetes’ market dominance, but it found a loyal user base among organizations that valued operational simplicity over feature completeness — a reasonable tradeoff that reflected Hashimoto’s belief that tools should be easy to operate in production, not just impressive in demos.
Departure from HashiCorp (2023). In December 2023, after more than a decade building infrastructure tooling, Hashimoto announced that he was leaving HashiCorp. By that point, HashiCorp had over 2,000 employees, was publicly traded on NASDAQ, and had revenues exceeding $500 million annually. The company Hashimoto co-founded with Armon Dadgar in a San Francisco apartment had become an enterprise software giant. But Hashimoto’s interests had shifted. In his departure announcement, he described his desire to return to hands-on technical work — writing code rather than managing an organization. The move was consistent with his identity as a builder rather than a corporate executive.
Ghostty (2024). Hashimoto’s post-HashiCorp project was Ghostty, a GPU-accelerated terminal emulator written in Zig. The choice of project might seem surprising — terminal emulators are not typically associated with infrastructure pioneers — but it aligned perfectly with Hashimoto’s core obsession: developer tools. A terminal emulator is the most fundamental tool in a developer’s workflow, the interface through which they interact with every other tool. Ghostty aimed to be the fastest, most correct, and most platform-native terminal emulator available, with proper Unicode support, GPU-accelerated rendering, and native macOS and Linux integration. The project attracted significant attention from the developer community, with thousands of GitHub stars before its public release. Writing it in Zig rather than Rust or C++ was a deliberate choice — Hashimoto was drawn to Zig’s philosophy of simplicity and explicit control, much as he had been drawn to Go for HashiCorp’s tools.
Philosophy and Approach
Key Principles
Mitchell Hashimoto’s engineering philosophy is visible in the design decisions shared across every tool he has built. Several principles recur consistently.
Declarative over imperative. Every major HashiCorp tool uses a declarative configuration model: the user describes what they want, not how to achieve it. Vagrantfiles describe the desired virtual machine state. Terraform configurations describe the desired infrastructure state. Consul configurations describe the desired service mesh topology. Vault policies describe the desired access control rules. This declarative approach has a profound operational advantage: configurations are idempotent. Running terraform apply twice with the same configuration produces the same result. Running it after someone manually modifies a resource corrects the drift. The system converges toward the declared state regardless of the starting point. This philosophy echoes the approach that Chris Lattner brought to compiler tooling — defining the desired outcome and letting the system determine the optimal path to reach it.
Single binary distribution. Every HashiCorp tool is distributed as a single static binary with no external dependencies. There is no package manager to configure, no runtime to install, no library path to set. You download one file, make it executable, and run it. This design choice reflects Hashimoto’s belief that operational simplicity starts at installation. A tool that is difficult to install will not be adopted, regardless of how powerful it is. The single-binary approach also simplifies deployment, upgrades, and air-gapped installations — all critical concerns in the enterprise environments where HashiCorp’s tools are used.
Workflow-centric design. Hashimoto has consistently designed tools around explicit, named workflows rather than exposing raw APIs. Terraform’s workflow is init, plan, apply. Vagrant’s workflow is init, up, provision, destroy. Packer’s workflow is init, build. Each step has a clear purpose, a predictable output, and a natural integration point for automation. This workflow-centric approach makes tools self-documenting — a new team member can understand the operational model by reading the names of the commands — and makes it easy to integrate tools into CI/CD pipelines. Teams at agencies like Toimi leverage workflow-centric infrastructure tools to maintain consistent deployment processes across multiple client projects.
Pluggable architecture. Terraform’s provider model, Vault’s plugin system for secret backends and authentication methods, Consul’s pluggable service mesh data plane, and Nomad’s task driver architecture all follow the same pattern: a stable core engine that communicates with external plugins through a well-defined interface. This design enables ecosystem growth without core complexity growth. The Terraform team does not need to understand every cloud provider’s API — they only need to maintain the provider interface contract. The community handles the rest. By 2026, this ecosystem-driven approach has produced thousands of community-maintained providers and plugins across the HashiCorp suite.
Solve one problem well. Each HashiCorp tool addresses exactly one operational concern: Vagrant handles development environments, Packer handles image building, Terraform handles provisioning, Consul handles service discovery, Vault handles secrets, Nomad handles scheduling. This Unix-philosophy approach — small, focused tools that compose well — stands in contrast to the “platform” approach taken by competitors like Kubernetes, which attempts to solve orchestration, service discovery, secrets management, and configuration management in a single system. Hashimoto’s bet was that focused tools with clear boundaries are easier to understand, easier to operate, and easier to replace individually as needs evolve. The success of the HashiCorp suite validated this approach for a significant segment of the market.
Legacy and Impact
Mitchell Hashimoto’s impact on modern software engineering extends far beyond the specific tools he built. He fundamentally changed how the industry thinks about infrastructure, transforming it from an operational concern managed through manual processes and ad-hoc scripts into a software engineering discipline with its own practices, patterns, and professional specialization.
The phrase “infrastructure-as-code” existed before Terraform — tools like Chef, Puppet, and Ansible had pioneered configuration management — but Terraform expanded the concept from server configuration to entire infrastructure topologies. Before Terraform, “infrastructure-as-code” meant automating what you installed on a server. After Terraform, it meant automating the existence of the server itself, along with its network, storage, DNS, security policies, and every other cloud resource. This shift from configuration management to infrastructure provisioning was a qualitative leap, and Terraform was the tool that made it practical for the mainstream.
The HashiCorp ecosystem also shaped the career trajectory of an entire generation of operations engineers. The “DevOps engineer” role, which barely existed in 2010, became one of the most in-demand positions in tech by 2020, and proficiency with HashiCorp tools — particularly Terraform and Vault — became a near-universal requirement for the role. HashiCorp’s certification program, launched in 2019, became one of the most recognized credentials in the infrastructure space. The community around HashiCorp tools — HashiConf conferences, Terraform module registries, community forums — created a professional ecosystem comparable to what Brendan Eich’s JavaScript created for frontend development or what Guido van Rossum’s Python created for data science.
Hashimoto’s departure from HashiCorp in 2023 and his pivot to Ghostty revealed another dimension of his influence: the cultural model of the founder-engineer. In an industry where successful founders typically transition into executive roles, Hashimoto chose to return to writing code. His post-departure technical writing — detailed blog posts about terminal rendering, font rasterization, and Zig programming — demonstrated an engineering depth unusual among founders of billion-dollar companies. This choice reinforced a narrative important to the developer community: that building things is more valuable than managing things, and that technical excellence retains its worth regardless of corporate success.
Looking at the full arc of Hashimoto’s career — from Vagrant in a college dorm to Terraform powering global infrastructure to Ghostty rendering pixels on a screen — the consistent thread is an unwavering focus on developer experience. Every tool he built started with the same question: what manual, fragile, frustrating process are developers tolerating today, and how can it be replaced with something declarative, reproducible, and simple? That question, applied persistently across a decade and a half, produced tools that millions of developers depend on daily. The infrastructure that runs the modern internet — the virtual machines, the containers, the networks, the secrets, the service meshes — is, to a remarkable degree, described in the language and managed by the tools that Mitchell Hashimoto created.
Key Facts
- Full name: Mitchell Hashimoto
- Education: Computer Science, University of Washington
- Known for: Co-founding HashiCorp, creating Terraform, Vagrant, Vault, Consul, Packer, and Nomad
- Co-founder: HashiCorp (2012, with Armon Dadgar) — IPO December 2021 on NASDAQ
- Key projects: Vagrant (2010), Packer (2013), Terraform (2014), Consul (2014), Vault (2015), Nomad (2015), Ghostty (2024)
- HashiCorp Configuration Language (HCL): Created the declarative language used across all HashiCorp tools
- Terraform providers: Over 4,000 community and official providers in the Terraform registry by 2026
- Post-HashiCorp: Left in December 2023 to focus on Ghostty, a GPU-accelerated terminal emulator written in Zig
- Programming languages: Go (HashiCorp tools), Ruby (Vagrant), Zig (Ghostty)
- Philosophy: Declarative configuration, single-binary distribution, workflow-centric design, focused tools over monolithic platforms
FAQ
What is Terraform and why did it become the standard for infrastructure-as-code?
Terraform is an open-source infrastructure-as-code tool that allows engineers to define cloud infrastructure — servers, networks, databases, DNS records, and thousands of other resource types — in declarative configuration files written in HashiCorp Configuration Language (HCL). When a developer runs terraform apply, the tool computes the difference between the declared desired state and the actual current state of the infrastructure, generates an execution plan, and applies only the necessary changes. Terraform became the industry standard for several reasons: it supports multiple cloud providers through a pluggable provider architecture (over 4,000 providers by 2026), enabling multi-cloud strategies with a single tool; its plan-then-apply workflow provides safety and predictability for infrastructure changes; its state management system tracks deployed resources and detects configuration drift; and its module system enables reusable, composable infrastructure components. Before Terraform, each cloud provider had its own proprietary provisioning tool with incompatible syntax and concepts. Terraform unified the infrastructure provisioning landscape under a single, cloud-agnostic tool.
How did Mitchell Hashimoto’s work relate to the container revolution led by Docker?
Hashimoto’s work and Solomon Hykes’ Docker addressed complementary layers of the infrastructure problem. Docker solved application packaging — how to bundle an application and its dependencies into a portable, reproducible unit. Terraform solved infrastructure provisioning — how to create and manage the cloud resources (virtual machines, networks, load balancers, Kubernetes clusters) on which those containers run. In practice, a modern deployment pipeline typically uses Packer to build machine images, Terraform to provision the infrastructure, Docker to package the application, and either Nomad or Kubernetes to orchestrate the containers. The HashiCorp stack and the container ecosystem are deeply intertwined rather than competitive. Hashimoto recognized early that containers would need sophisticated infrastructure management, and Terraform’s support for Docker, Kubernetes, and every major container orchestration platform reflects this understanding.
Why did Mitchell Hashimoto leave HashiCorp to build a terminal emulator?
Hashimoto’s departure from HashiCorp in December 2023 and his subsequent focus on Ghostty reflected his identity as a builder rather than an executive. As HashiCorp grew to over 2,000 employees and became a publicly traded company, Hashimoto’s role necessarily shifted from writing code to organizational leadership. His departure announcement emphasized his desire to return to hands-on engineering work. The choice of a terminal emulator as his next project was consistent with his career-long focus on developer tools — the terminal is the most fundamental interface through which developers interact with all other tools, including the HashiCorp suite itself. Ghostty, written in Zig with GPU-accelerated rendering and comprehensive Unicode support, aims to be the fastest and most correct terminal emulator available. The project demonstrated that Hashimoto’s passion was always for the craft of building developer tools rather than for any specific domain like cloud infrastructure.
What is HCL and how does it differ from YAML and JSON for configuration?
HashiCorp Configuration Language (HCL) is a declarative configuration language created by Hashimoto specifically for describing infrastructure and operational configurations. Unlike JSON, which lacks comments and is verbose for human authoring, and unlike YAML, which is prone to subtle indentation errors and has limited expressiveness, HCL was designed from the ground up for infrastructure configuration. It supports comments, multi-line strings, variable interpolation, conditional expressions, loops (for_each, count), functions, and module composition. HCL is both human-readable (it looks like a clean, structured configuration format) and machine-parseable (HashiCorp provides official parsers in Go and other languages). The language strikes a deliberate balance between the simplicity of a data format and the expressiveness of a programming language — powerful enough to express complex infrastructure topologies, but constrained enough to remain declarative and predictable. HCL is used across all major HashiCorp tools: Terraform, Packer, Vault, Consul, Nomad, and Waypoint.