In the mid-1980s, when the world of public-key cryptography was dominated by RSA and its resource-hungry computations, a pure mathematician with no background in computer engineering proposed an elegant alternative that would eventually secure billions of digital transactions. Neal Koblitz did not set out to revolutionize cybersecurity — he was simply fascinated by the deep arithmetic properties of elliptic curves. His 1985 paper suggesting that elliptic curves over finite fields could serve as the basis for cryptographic systems opened a pathway to smaller keys, faster computations, and a fundamentally different approach to protecting data. Four decades later, elliptic curve cryptography (ECC) underpins TLS certificates, cryptocurrency wallets, secure messaging apps, and embedded devices around the world. Koblitz’s story is one of mathematical beauty meeting practical necessity, and of a scholar who has never been afraid to challenge the consensus of his own field.
Early Life and Education
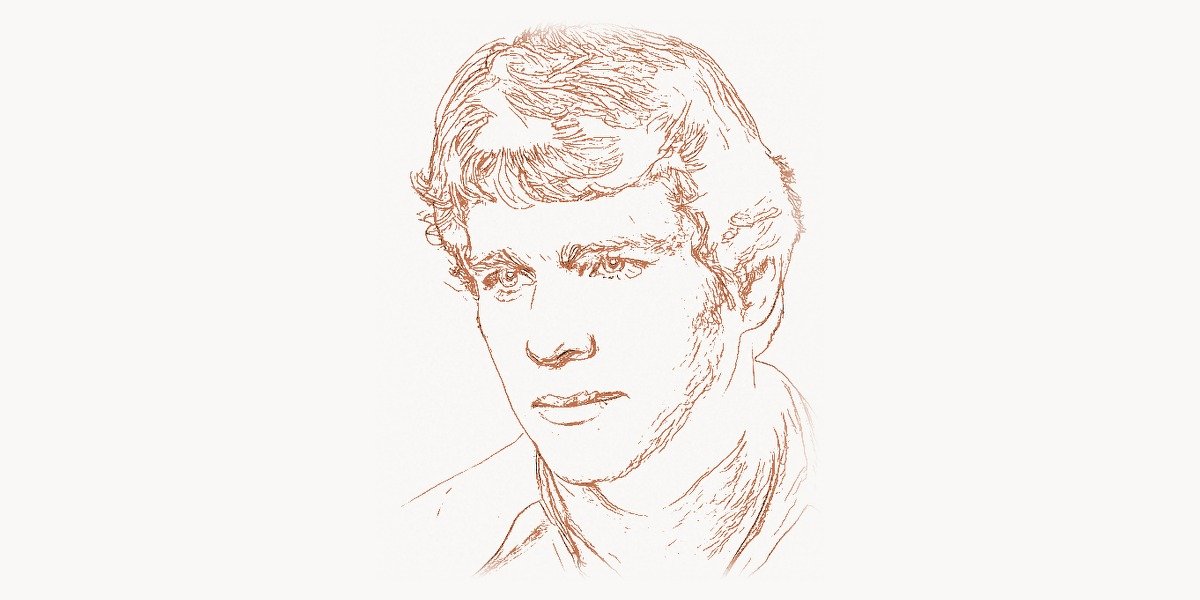
Neal Ivan Koblitz was born on December 24, 1948, in Rochester, New York. His father was a chemist, and his mother a teacher, and both encouraged an early appreciation for abstract reasoning. Koblitz showed extraordinary aptitude in mathematics from a young age, breezing through standard curricula and seeking out problems far beyond his grade level. He enrolled at Harvard University, where he studied mathematics and graduated summa cum laude in 1969.
From Harvard, Koblitz moved to Princeton University for his doctoral work, one of the most prestigious mathematics departments in the world. He worked under the supervision of Nickolas Katz, a leading figure in algebraic geometry and number theory. His doctoral dissertation focused on p-adic analysis and its connections to modular forms — a deeply theoretical area that would later prove unexpectedly relevant to cryptographic applications. Koblitz earned his Ph.D. in 1974 and soon after joined the faculty at the University of Washington in Seattle, where he has remained for over five decades.
During the late 1970s and early 1980s, Koblitz immersed himself in number theory, algebraic geometry, and the arithmetic of elliptic curves. It was this expertise — cultivated through years of pure mathematical research — that positioned him uniquely to see what engineers and computer scientists had missed: elliptic curves were not just beautiful abstract objects, but powerful engines for practical cryptography. His path mirrored the journey of other mathematicians like Edgar F. Codd, whose theoretical insights reshaped entire industries.
Career and Technical Contributions
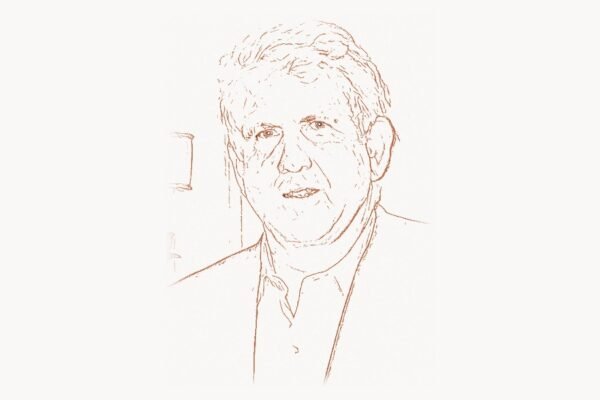
Koblitz joined the University of Washington’s Department of Mathematics in 1979 and quickly established himself as one of the leading number theorists in the country. His early work explored connections between p-adic analysis, modular forms, and the zeta functions of algebraic varieties. He published influential textbooks on these topics that became standard references for graduate students worldwide.
But it was a pivotal insight in 1985 that would define his career in the eyes of the wider world. Koblitz realized that the mathematical group structure of elliptic curves over finite fields could be harnessed for public-key cryptography — an insight that arrived independently and simultaneously from Victor Miller at IBM. The two men, working without knowledge of each other’s efforts, published proposals that would eventually converge into what we now call elliptic curve cryptography (ECC).
Technical Innovation: Elliptic Curve Cryptography
To understand Koblitz’s innovation, it helps to recall the landscape of public-key cryptography in the mid-1980s. The dominant system was RSA, invented in 1977 by Ron Rivest, Adi Shamir, and Leonard Adleman. RSA’s security relies on the difficulty of factoring large integers — a problem that, while hard, requires increasingly massive key sizes as computational power grows. By the 2000s, RSA keys needed to be 2048 bits or more to remain secure.
Koblitz and Miller proposed an alternative rooted in a different mathematical problem: the elliptic curve discrete logarithm problem (ECDLP). Given an elliptic curve E over a finite field and two points P and Q = kP on that curve, finding the integer k is computationally infeasible when the curve and field are chosen properly. Crucially, no sub-exponential algorithm is known for solving ECDLP on well-chosen curves — unlike integer factorization, which can be attacked by the number field sieve.
This difference in hardness translates directly into key sizes. A 256-bit ECC key provides roughly the same security as a 3072-bit RSA key. This dramatic reduction in key size has cascading benefits: less bandwidth consumption, faster handshakes, lower power usage, and feasibility on constrained devices like smart cards and IoT sensors.
The mathematical foundation can be illustrated through a simplified key exchange. Here is a conceptual implementation of an elliptic curve Diffie-Hellman (ECDH) key exchange in Python using standard libraries:
from cryptography.hazmat.primitives.asymmetric import ec
from cryptography.hazmat.primitives import hashes
from cryptography.hazmat.primitives.kdf.hkdf import HKDF
# Alice generates her ECC private key on the NIST P-256 curve
alice_private = ec.generate_private_key(ec.SECP256R1())
alice_public = alice_private.public_key()
# Bob generates his ECC private key on the same curve
bob_private = ec.generate_private_key(ec.SECP256R1())
bob_public = bob_private.public_key()
# Both compute the shared secret via ECDH
alice_shared = alice_private.exchange(ec.ECDH(), bob_public)
bob_shared = bob_private.exchange(ec.ECDH(), alice_public)
# Derive a symmetric key from the shared secret
derived_key = HKDF(
algorithm=hashes.SHA256(),
length=32,
salt=None,
info=b"ecdh-key-exchange",
).derive(alice_shared)
# alice_shared == bob_shared — both arrive at the same secret
# A 256-bit ECC key here provides ~128-bit security level
# Equivalent RSA would require a 3072-bit key for similar strength
print(f"Shared secret derived: {derived_key.hex()[:32]}...")This code leverages the same mathematical principles that Koblitz and Miller identified in 1985. The curve SECP256R1 (also known as P-256) is one of the most widely deployed elliptic curves today, used in everything from TLS handshakes to code signing. The key insight — that elliptic curve point multiplication is a one-way function — is what makes the entire scheme work. The work of Whitfield Diffie and Martin Hellman in establishing public-key cryptography laid the essential groundwork upon which Koblitz built his elliptic curve proposal.
Why It Mattered
When Koblitz first published his proposal, the reaction from the cryptographic community was cautious. RSA was well-understood, widely implemented, and backed by significant corporate investment. ECC was seen as mathematically exotic and unproven in practice. It took over a decade for the engineering world to catch up with the mathematics.
The turning point came in the late 1990s and 2000s, when the need for efficient cryptography on mobile devices, embedded systems, and resource-constrained environments became urgent. The advantages of ECC — smaller keys, faster operations, lower bandwidth — made it the natural choice. The NSA’s Suite B cryptographic standards, published in 2005, endorsed ECC as the preferred algorithm for protecting classified information up to the Top Secret level. This endorsement was a watershed moment: it signaled to the entire industry that ECC was not merely an academic curiosity, but a battle-tested technology suitable for the most sensitive applications.
Today, ECC is the backbone of modern internet security. When you connect to a website over HTTPS, your browser likely performs an ECDHE key exchange. Bitcoin and Ethereum use the secp256k1 elliptic curve for digital signatures. Signal Protocol — the encryption layer behind Moxie Marlinspike’s Signal app and WhatsApp — relies heavily on ECC. Apple’s Secure Enclave, Android’s Keystore, and hardware security modules across the globe all depend on the mathematics that Koblitz helped introduce to the world.
For teams building secure applications today, understanding the cryptographic primitives that protect user data is essential. Modern project management tools that handle sensitive business information depend on exactly these kinds of encryption protocols to maintain data integrity and confidentiality across distributed teams.
Other Notable Contributions
While ECC remains his most widely known contribution, Koblitz’s mathematical output extends far beyond a single 1985 paper. He has been a prolific author of textbooks that bridge pure mathematics and applied cryptography, making abstruse topics accessible to graduate students and practitioners alike.
His books include A Course in Number Theory and Cryptography (1987), Algebraic Aspects of Cryptography (1998), and Introduction to Elliptic Curves and Modular Forms (1984). These texts have trained generations of cryptographers and remain in print decades after their initial publication. Koblitz has a rare gift for exposition: he can move seamlessly between rigorous proofs and intuitive explanations, a quality that has made his writing enduringly popular.
Koblitz also contributed to the development of hyperelliptic curve cryptography, exploring whether curves of higher genus could offer cryptographic advantages. While hyperelliptic systems have not achieved the widespread adoption of standard ECC, the research pushed the boundaries of what mathematical structures could be applied to secure communication.
Another significant contribution is the Koblitz curve family — specific elliptic curves defined over binary fields (GF(2m)) that allow particularly efficient point multiplication. These curves, sometimes called anomalous binary curves, enable hardware implementations that are notably faster than general curves. A simplified configuration for an OpenSSL setup using modern ECC looks like this:
# Generate an ECC private key using the P-256 curve
openssl ecparam -genkey -name prime256v1 -out server-ecc.key
# Create a certificate signing request
openssl req -new -key server-ecc.key \
-out server-ecc.csr \
-subj "/CN=example.com/O=MyOrg/C=US"
# Self-sign the certificate (valid for 365 days)
openssl x509 -req -days 365 \
-in server-ecc.csr \
-signkey server-ecc.key \
-out server-ecc.crt
# Verify the key details — note the 256-bit key size
openssl ec -in server-ecc.key -text -noout
# Output shows: ASN1 OID: prime256v1 (NIST P-256)
# Private Key: 256 bit
# This tiny key provides security comparable to RSA-3072
# Compare file sizes — ECC certificates are dramatically smaller
ls -la server-ecc.key # ~240 bytes (ECC)
# vs. typical RSA-2048 key: ~1,700 bytesThis practical difference in key and certificate size is directly traceable to Koblitz and Miller’s theoretical insight. Every time a TLS handshake completes in milliseconds rather than seconds, it is partly because the underlying mathematics permits smaller, faster cryptographic operations.
Philosophy and Key Principles
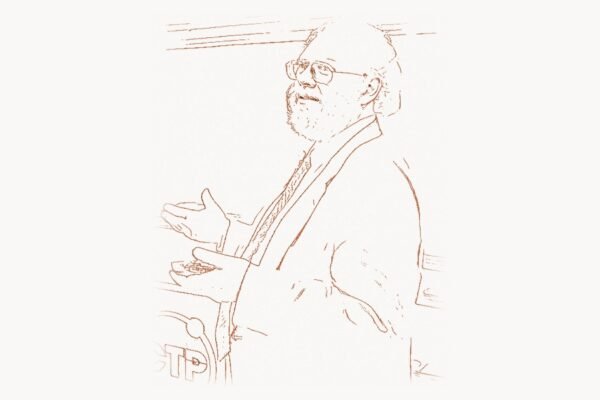
Neal Koblitz is almost as well known for his intellectual combativeness as for his mathematical contributions. He is one of the most outspoken critics of the culture of formal security proofs in cryptography — a position that has made him both respected and controversial within the field.
Koblitz, often writing with his frequent collaborator Alfred Menezes, has published a series of provocative papers arguing that the security “proofs” common in academic cryptography are frequently misleading. Their central argument is that these proofs often rely on idealized assumptions (such as the random oracle model) that do not hold in practice, and that the reduction bounds are typically so loose as to be practically meaningless. A system might be “provably secure” in theory while being entirely breakable in practice, because the proof guarantees nothing useful about real-world parameters.
This skepticism extends to what Koblitz sees as a broader cultural problem in academic cryptography: a tendency to value mathematical formalism over engineering rigor, to confuse the existence of a proof with the existence of actual security. He has argued that the emphasis on provable security has created a false sense of confidence and has sometimes distracted researchers from more productive lines of inquiry.
His views echo a broader philosophical tradition in mathematics and engineering — the recognition that formal models are only as good as their assumptions, and that elegance in theory does not guarantee robustness in practice. This intellectual stance connects him to thinkers like Donald Knuth, who similarly insisted on meticulous attention to the gap between abstraction and implementation. Security researchers like Bruce Schneier have expressed related concerns about the distance between theoretical guarantees and real-world security outcomes.
Koblitz has also been a vocal advocate for mathematical education in developing countries. He co-founded the Koblitz Scholarship Fund, which supports mathematics students in Vietnam, and has spent significant time teaching and mentoring in Latin America and Southeast Asia. This commitment to global mathematical literacy reflects a belief that access to advanced mathematics should not be the exclusive province of wealthy nations — a principle that guides his broader view of science as a fundamentally human and humanistic endeavor.
For organizations looking to implement robust digital security strategies, understanding the mathematical foundations that experts like Koblitz championed is invaluable. Agencies specializing in web development and digital strategy increasingly emphasize cryptographic best practices as a core component of any serious technology deployment.
Legacy and Impact
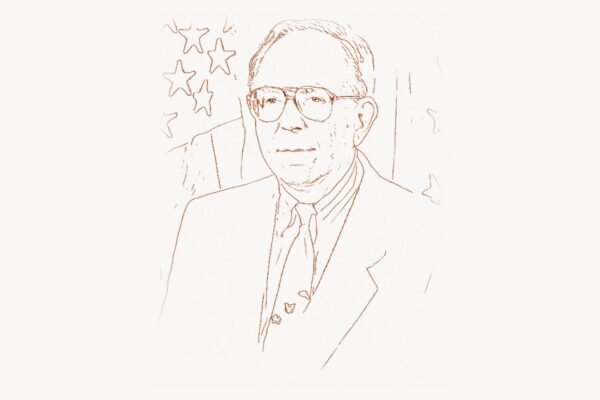
The impact of Neal Koblitz’s work is measured in billions of secure connections established every day. ECC is now the default or strongly preferred cryptographic mechanism in all major web browsers, operating systems, and communication protocols. The migration from RSA to ECC — a process that accelerated dramatically after 2010 — represents one of the most significant infrastructure transitions in the history of the internet.
Koblitz’s influence extends into the cryptocurrency revolution. Bitcoin’s entire transaction signing mechanism is built on the secp256k1 elliptic curve. Every Bitcoin address, every signed transaction, every proof of ownership traces its mathematical lineage back to the ideas that Koblitz and Miller articulated in 1985. The same is true of Ethereum, Solana, and most other blockchain platforms. The cryptographic foundations that Phil Zimmermann brought to the masses through PGP now operate at a global scale through elliptic curves.
In hardware security, ECC has enabled entire categories of devices that would be impractical with RSA. Contactless payment cards, electronic passports, automotive key fobs, and medical implants all rely on ECC because its small key sizes and fast operations fit within tight power and memory budgets. The expansion of the Internet of Things — billions of connected sensors and actuators — would face severe bottlenecks without the efficiency that ECC provides.
The post-quantum cryptography era now looming on the horizon adds another dimension to Koblitz’s legacy. While standard ECC is vulnerable to Shor’s algorithm on a sufficiently powerful quantum computer, the research directions that Koblitz helped open — including work on algebraic curves and lattice-based systems — continue to inform the search for quantum-resistant alternatives. Researchers like Tanja Lange are building directly on foundations that Koblitz helped establish.
At the University of Washington, Koblitz has mentored dozens of doctoral students who have gone on to careers in academia, industry, and government cryptographic agencies. His textbooks remain in active use at universities worldwide. His willingness to challenge established orthodoxies — whether in the form of overblown security claims or the neglect of mathematical education in developing nations — has made him an enduring, if sometimes prickly, presence in the mathematical community.
Neal Koblitz did not simply propose an algorithm. He demonstrated that pure mathematical research, pursued with rigor and intellectual honesty, can transform the infrastructure of global communication. In an era when digital security is synonymous with economic security, personal privacy, and even national defense, his contribution stands as one of the most consequential in the history of applied mathematics.
Key Facts
| Detail | Information |
|---|---|
| Full Name | Neal Ivan Koblitz |
| Born | December 24, 1948, Rochester, New York, USA |
| Education | A.B. Harvard University (1969); Ph.D. Princeton University (1974) |
| Doctoral Advisor | Nickolas Katz |
| Primary Affiliation | University of Washington, Department of Mathematics |
| Key Innovation | Independently proposed elliptic curve cryptography (ECC) in 1985 |
| Notable Works | A Course in Number Theory and Cryptography; Introduction to Elliptic Curves and Modular Forms |
| Known For | ECC, Koblitz curves, hyperelliptic curve cryptography, critique of provable security |
| Awards | Fulbright Scholar; Guggenheim Fellow |
| ECC Key Size Advantage | 256-bit ECC ≈ 3072-bit RSA security |
Frequently Asked Questions
What is elliptic curve cryptography and why is it important?
Elliptic curve cryptography (ECC) is a public-key encryption approach based on the algebraic structure of elliptic curves over finite fields. Its importance lies in efficiency: ECC achieves the same level of security as older systems like RSA but with dramatically smaller key sizes. A 256-bit ECC key offers comparable protection to a 3072-bit RSA key, which translates to faster computations, less bandwidth usage, and better performance on resource-constrained devices like smartphones, smart cards, and IoT sensors. Today, ECC secures the majority of HTTPS connections, cryptocurrency transactions, and secure messaging protocols worldwide.
How does Koblitz’s contribution differ from Victor Miller’s?
Neal Koblitz and Victor Miller independently proposed using elliptic curves for cryptography in 1985. Both recognized that the elliptic curve discrete logarithm problem offered a harder mathematical foundation than integer factorization for comparable key sizes. Koblitz approached the problem from the perspective of a pure mathematician deeply versed in number theory and algebraic geometry, while Miller came from the applied research environment at IBM. Their proposals were complementary, and both are credited as co-founders of ECC. Koblitz went on to develop additional contributions including Koblitz curves optimized for binary fields and authored several influential textbooks on the mathematical foundations.
Why is Koblitz critical of formal security proofs in cryptography?
Koblitz, often collaborating with Alfred Menezes, has argued that many security “proofs” in academic cryptography provide a misleading sense of confidence. Their critique focuses on several issues: the proofs frequently rely on idealized models (like the random oracle model) that do not accurately represent real-world conditions; the reduction bounds are often so loose that they say nothing meaningful about practical security parameters; and the academic incentive structure rewards the production of proofs regardless of their practical relevance. Koblitz contends that this culture can distract from genuine security analysis and create a false sense of invulnerability in systems that may still be vulnerable in practice.
Is ECC still secure in the era of quantum computing?
Standard ECC, like RSA, is theoretically vulnerable to quantum computers running Shor’s algorithm, which could solve the elliptic curve discrete logarithm problem in polynomial time. However, building a quantum computer powerful enough to break ECC-256 requires thousands of error-corrected logical qubits — a capability that does not yet exist and may not for years or decades. In the meantime, the cryptographic community is developing post-quantum alternatives, including lattice-based, hash-based, and code-based systems. NIST finalized its first set of post-quantum standards in 2024. Koblitz’s broader legacy — the idea of finding new hard mathematical problems for cryptography — directly informs this ongoing search for quantum-resistant systems.