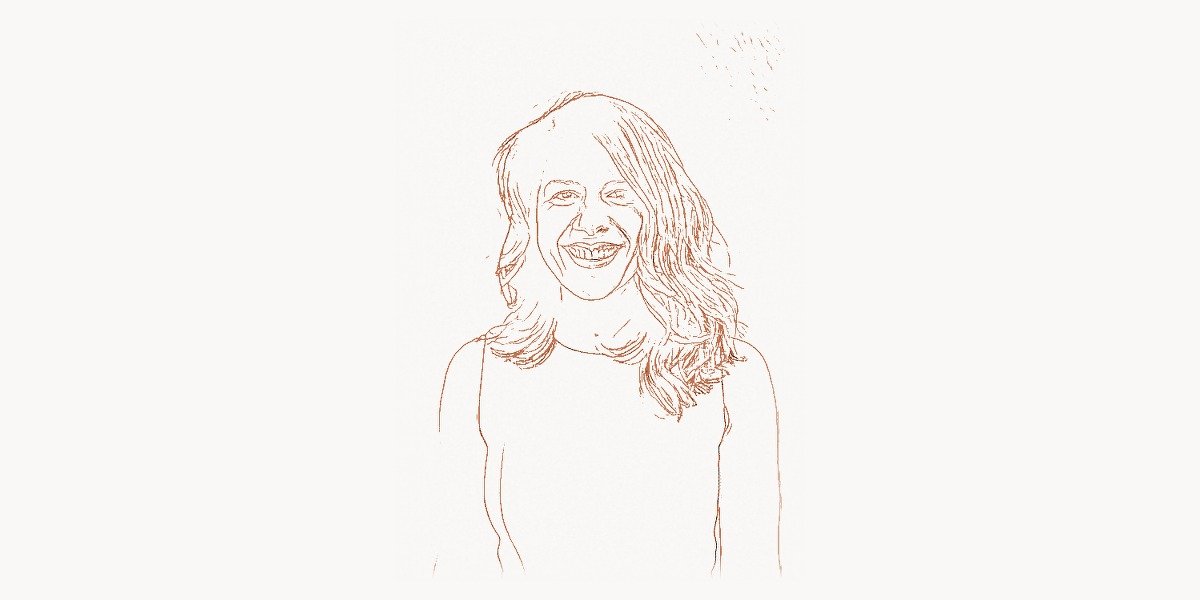
In the world of cybersecurity, where titles like “Chief Information Security Officer” and “Principal Threat Analyst” dominate LinkedIn profiles, one of the most influential security leaders in tech history chose a decidedly different title for her business card: Security Princess. Parisa Tabriz earned that self-given moniker not through whimsy, but through a decade-and-a-half of relentless work making Google Chrome — the browser used by billions of people worldwide — one of the most secure pieces of software ever shipped. As Vice President of Chrome Engineering at Google, Tabriz has shaped how the modern web handles encryption, sandboxing, certificate validation, and vulnerability disclosure. Her journey from a curious teenager hand-coding HTML to overseeing the security posture of the planet’s most popular browser is a masterclass in what happens when technical brilliance meets a genuine passion for protecting people.
Early Life and Education
Parisa Tabriz was born in 1983 in Chicago, Illinois, to an Iranian-American family. Growing up in the suburbs of Chicago, she developed an early fascination with computers. Her father, an Iranian immigrant and physician, encouraged her curiosity. As a teenager, Tabriz taught herself HTML and built websites, discovering not just how to create things on the web but how to break them — a curiosity that would define her career.
Tabriz enrolled at the University of Illinois at Urbana-Champaign (UIUC), one of the top computer science programs in the world. At UIUC, she studied computer science and quickly gravitated toward security research. She became involved in hands-on security work, participating in capture-the-flag competitions and vulnerability research that gave her practical experience far beyond what coursework alone could provide. She earned her Master’s degree in Computer Science with a focus on security, completing research on web application vulnerabilities and cross-site scripting (XSS) attacks — the very class of bugs she would later spend years helping to eradicate at scale.
Her time at UIUC also instilled a collaborative spirit. She frequently worked in teams, contributed to open-source security tools, and developed a belief that security was fundamentally about people — not just code. This human-centric perspective would become one of the defining aspects of her approach to engineering leadership.
Career and Technical Contributions
Tabriz joined Google in 2007 as an information security engineer, initially working on the company’s internal security team. Her early projects involved security reviews of Google products, penetration testing, and incident response. She quickly stood out for her combination of deep technical ability and her talent for communicating complex security concepts to non-security engineers.
By 2012, she had transitioned to leading the security efforts for Google Chrome, which was rapidly becoming the world’s dominant web browser. This was a pivotal moment — Chrome was not merely a browser but a platform through which billions of users accessed the internet. Making Chrome secure meant making the web itself more secure.
Technical Innovation
Tabriz’s contributions to Chrome security span multiple foundational areas of browser and web security. Her team drove several initiatives that fundamentally changed how the internet operates.
HTTPS Everywhere and Certificate Transparency. Perhaps the most visible impact of Tabriz’s leadership was Chrome’s aggressive push toward universal HTTPS adoption. Under her direction, Chrome began marking HTTP sites as “Not Secure” starting in 2017 — a move that dramatically accelerated the web’s migration to encrypted connections. Before this initiative, less than 50% of web traffic was encrypted; by 2023, over 95% of Chrome traffic used HTTPS. Her team also championed Certificate Transparency, an open framework for monitoring and auditing SSL/TLS certificates. This system makes it nearly impossible for certificate authorities to issue fraudulent certificates without detection. The implementation involved creating an append-only log infrastructure that anyone can audit:
# Simplified example of Certificate Transparency log verification
# Demonstrates the Merkle tree hash chain concept used in CT logs
import hashlib
import json
class CTLogVerifier:
"""Verifies certificate entries against Certificate Transparency logs."""
def __init__(self, log_url):
self.log_url = log_url
def compute_leaf_hash(self, cert_entry):
"""Compute the Merkle tree leaf hash for a certificate entry.
RFC 6962 specifies: hash(0x00 || timestamp || entry_type || cert_data)
"""
leaf_input = b'\x00' # leaf hash prefix
leaf_input += cert_entry['timestamp'].to_bytes(8, 'big')
leaf_input += cert_entry['entry_type'].to_bytes(2, 'big')
leaf_input += cert_entry['cert_data']
return hashlib.sha256(leaf_input).hexdigest()
def verify_inclusion_proof(self, leaf_hash, proof, tree_size, root_hash):
"""Verify a Merkle inclusion proof for a certificate.
This ensures the certificate was actually logged in the CT log.
"""
computed = bytes.fromhex(leaf_hash)
for i, node in enumerate(proof):
node_bytes = bytes.fromhex(node)
if self._is_left_child(i, tree_size):
computed = hashlib.sha256(b'\x01' + computed + node_bytes).digest()
else:
computed = hashlib.sha256(b'\x01' + node_bytes + computed).digest()
return computed.hex() == root_hash
# Chrome enforces CT compliance: certificates issued after April 2018
# must appear in multiple CT logs to be trusted by the browserSite Isolation and Process Sandboxing. One of the most technically ambitious security projects Tabriz’s team delivered was Site Isolation, a Chrome architecture change that ensures every website runs in its own separate operating system process. This was a direct response to the Spectre and Meltdown CPU vulnerabilities discovered in 2018, which showed that malicious websites could potentially read data from other sites running in the same process. Implementing Site Isolation required re-architecting significant portions of Chrome’s rendering engine and was one of the largest security-motivated engineering efforts in browser history.
Chrome’s Bug Bounty Program. Tabriz was instrumental in scaling Google’s Vulnerability Reward Program (VRP) for Chrome, which has paid out millions of dollars to security researchers who responsibly disclose bugs. Under her leadership, the program expanded its scope and raised its maximum payouts significantly, attracting top security talent from around the world to find and report vulnerabilities before they could be exploited.
Safe Browsing and Phishing Protection. Tabriz’s team enhanced Chrome’s Safe Browsing capabilities, building machine-learning models that could detect phishing pages and malicious downloads in real time. This technology protects not just Chrome users but the entire web ecosystem, as the Safe Browsing API is used by Firefox, Safari, and many other applications.
Why It Mattered
The cumulative impact of these technical contributions is difficult to overstate. Chrome is used by approximately 3.5 billion people worldwide. Every security improvement Tabriz’s team shipped — from HTTPS enforcement to Site Isolation to improved phishing detection — directly protected a significant fraction of all internet users. The push for HTTPS fundamentally changed the economics of web encryption, making TLS certificates freely available through initiatives like Let’s Encrypt and pressuring hosting providers to offer HTTPS by default.
Certificate Transparency, meanwhile, created an entirely new accountability layer for the web’s trust infrastructure. Before CT, compromised or corrupt certificate authorities could issue fraudulent certificates with minimal risk of detection. After CT, every certificate is logged publicly and can be audited by anyone — a radical transparency mechanism that has caught real-world abuse multiple times. Tabriz’s work aligns well with modern project management approaches that emphasize transparency and accountability in complex technical operations.
Other Notable Contributions
Project Zero. While not directly part of her Chrome team, Tabriz was a strong internal advocate for Google’s Project Zero, an elite team of security researchers dedicated to finding zero-day vulnerabilities in widely-used software — not just Google’s products. Project Zero’s 90-day disclosure policy (giving vendors 90 days to fix a vulnerability before public disclosure) set a new industry standard for responsible disclosure timelines.
Security Key and FIDO2/WebAuthn. Tabriz’s team drove Chrome’s early adoption of hardware security keys and the FIDO2/WebAuthn authentication standard. Chrome was one of the first browsers to support these phishing-resistant authentication methods, pushing the industry toward a passwordless future. The implementation details of WebAuthn credential creation illustrate the sophistication of modern browser security APIs:
// WebAuthn credential creation — the phishing-resistant authentication
// standard that Chrome championed under Tabriz's leadership
async function registerSecurityKey(userId, userName) {
// The browser binds the credential to the exact origin,
// making phishing fundamentally impossible
const publicKeyOptions = {
challenge: crypto.getRandomValues(new Uint8Array(32)),
rp: {
name: "Example Corp",
id: "example.com" // Credential is cryptographically bound to this origin
},
user: {
id: new TextEncoder().encode(userId),
name: userName,
displayName: userName
},
pubKeyCredParams: [
{ alg: -7, type: "public-key" }, // ES256 (ECDSA w/ P-256)
{ alg: -257, type: "public-key" } // RS256 (RSASSA-PKCS1-v1_5)
],
authenticatorSelection: {
authenticatorAttachment: "cross-platform",
residentKey: "required",
userVerification: "required"
},
timeout: 60000,
attestation: "direct"
};
try {
const credential = await navigator.credentials.create({
publicKey: publicKeyOptions
});
// The credential.response contains the attestation object
// proving the key was generated by genuine hardware
console.log("Security key registered:", credential.id);
return credential;
} catch (err) {
console.error("Registration failed:", err.message);
}
}
// Chrome's implementation ensures credentials cannot be extracted
// or replayed across different origins — the core anti-phishing guaranteeDiversity and Inclusion in Security. Tabriz has been one of the most visible advocates for diversity in cybersecurity. As one of the most senior women in Google engineering, she has consistently used her platform to mentor underrepresented engineers and speak at events focused on bringing more women and minorities into security. She has spoken publicly about being one of the only women in security meetings early in her career and how that experience motivated her to actively work on changing the demographics of the field.
Conference Talks and Public Education. Tabriz has delivered keynotes and talks at major security conferences including Black Hat, DEF CON, RSA Conference, and Google I/O. Her presentations are known for blending deep technical content with accessible explanations, making complex security topics understandable to broader audiences. Her 2018 Black Hat keynote on the state of browser security was particularly influential in framing browser vendors as the front line of defense for internet users.
Philosophy and Key Principles
Tabriz’s approach to security leadership is built on several core principles that distinguish her from many of her peers.
Security should be invisible. Tabriz has consistently argued that the best security is security users never have to think about. Rather than burdening users with complex security decisions, Chrome should make secure defaults the path of least resistance. This philosophy drove decisions like auto-upgrading HTTP navigations to HTTPS and hiding complex certificate details behind simple visual indicators.
Defenders must think like attackers. Tabriz’s background in penetration testing shaped her belief that security teams must deeply understand offensive techniques to build effective defenses. She has encouraged her teams to participate in CTF competitions, conduct red-team exercises, and engage with the broader security research community. This aligns with the adversarial thinking exemplified by pioneers like Daniel J. Bernstein, who approached cryptographic design from a rigorous adversarial perspective.
Transparency builds trust. From Certificate Transparency to Chrome’s public security bug tracker, Tabriz has championed openness in security processes. She believes that exposing security mechanisms to public scrutiny — rather than relying on security through obscurity — produces stronger, more trustworthy systems. This mirrors the open-source security philosophy long advocated by the cryptography community.
Security is a team sport. Tabriz has frequently emphasized that securing a product as complex as Chrome requires collaboration across many disciplines — not just security specialists, but also UX designers, product managers, and infrastructure engineers. She has built organizational structures that embed security expertise directly into feature teams rather than keeping it siloed. Effective security management, much like comprehensive digital project management, requires coordination across diverse teams and clear communication channels.
Empathy for users and developers. Unlike security leaders who view users as liabilities, Tabriz approaches security design with empathy. She recognizes that developers under deadline pressure will take shortcuts, and that users will click on phishing links — not because they are careless, but because attackers are skilled. Her security designs account for human behavior rather than demanding humans change.
Legacy and Impact
Parisa Tabriz’s legacy extends far beyond Google Chrome. Her work has reshaped the security posture of the entire web.
The HTTPS transition she spearheaded is one of the most significant infrastructure changes in internet history. By using Chrome’s market dominance as leverage to pressure websites toward encryption, Tabriz and her team effectively made mass surveillance of web browsing dramatically harder. This had geopolitical implications, particularly for users in countries where government monitoring of internet traffic is commonplace.
Her advocacy for bug bounties helped legitimize vulnerability research as a profession. The Chrome VRP, along with programs at other major companies, created a legal and economic framework for security researchers to report bugs rather than exploit or sell them. This shift in incentives has prevented countless security breaches.
Site Isolation stands as an engineering marvel — a response to hardware-level vulnerabilities (Spectre/Meltdown) that was implemented at the software layer, protecting billions of users from a class of attacks that the hardware itself could not prevent. The architectural patterns established by Site Isolation have influenced how other browsers and applications approach process isolation.
Tabriz’s visible leadership as a woman of Iranian descent in one of the most senior security roles in the tech industry has had an outsized cultural impact. She has been named to Forbes’ “30 Under 30” and Wired’s list of people shaping the future of security. Her “Security Princess” title — playfully chosen when a Google executive told her she could put any title on her business card — became an internationally recognized symbol of making cybersecurity more approachable and inclusive.
Her influence on the web security ecosystem resonates with the work of other pioneers who shaped how the internet handles trust and communication — from the standards work that defined HTML5 to the browser innovations that first made the web accessible to mainstream users.
As Chrome continues to evolve — with new privacy features, post-quantum cryptography preparation, and AI-assisted threat detection — Tabriz’s foundational work on browser security architecture ensures that these advances are built on a robust, well-defended platform. Her career demonstrates that security leadership is not about locking things down; it is about building systems that empower people to use the web safely, freely, and without fear.
Key Facts
| Category | Detail |
|---|---|
| Full Name | Parisa Tabriz |
| Born | 1983, Chicago, Illinois, USA |
| Education | B.S. and M.S. in Computer Science, University of Illinois at Urbana-Champaign |
| Known For | Vice President of Chrome Engineering at Google; “Security Princess” |
| Key Projects | Chrome HTTPS enforcement, Certificate Transparency, Site Isolation, Chrome Bug Bounty (VRP), Safe Browsing, WebAuthn/FIDO2 support |
| HTTPS Impact | Drove web HTTPS adoption from ~50% to over 95% of Chrome traffic |
| Users Protected | Approximately 3.5 billion Chrome users worldwide |
| Notable Title | “Security Princess” (self-chosen Google business card title) |
| Recognition | Forbes “30 Under 30”, Wired security influencer, Black Hat / DEF CON keynote speaker |
| Joined Google | 2007 |
Frequently Asked Questions
Why is Parisa Tabriz called the “Security Princess”?
When Tabriz was early in her career at Google, a senior executive told her she could choose any title for her business card. Instead of opting for a conventional corporate title, she chose “Security Princess” — a deliberate move to make cybersecurity feel more approachable and to challenge the stereotypically intimidating image of the field. The title stuck and became internationally known, symbolizing both her technical authority and her commitment to making security accessible. Despite the playful title, Tabriz holds one of the most senior engineering positions at Google as Vice President of Chrome Engineering.
What was Parisa Tabriz’s most impactful contribution to web security?
While Tabriz has driven numerous major security initiatives, her leadership of Chrome’s push for universal HTTPS adoption is arguably her most far-reaching contribution. By marking HTTP sites as “Not Secure” in Chrome’s address bar starting in 2017, her team created powerful economic and social incentives for website operators to adopt encryption. This single decision helped shift the web from roughly half-encrypted to over 95% encrypted traffic, fundamentally improving the privacy and security of billions of internet users. The initiative also accelerated the growth of free certificate authorities like Let’s Encrypt, democratizing access to web encryption.
How did Chrome’s Site Isolation protect users from Spectre and Meltdown?
The Spectre and Meltdown vulnerabilities, disclosed in January 2018, revealed that malicious code running on a CPU could potentially read data from other processes sharing the same processor resources. For browsers, this meant a malicious website could theoretically read data (cookies, passwords, form data) from other sites open in adjacent tabs. Tabriz’s team responded by implementing Site Isolation in Chrome, which places each website in its own dedicated operating system process with separate memory space. This architectural change meant that even if a Spectre-style attack executed in one tab, the process boundaries enforced by the operating system would prevent it from accessing data belonging to other sites. The effort required changes to Chrome’s rendering pipeline, network stack, and memory management — one of the most complex security-motivated re-architecture efforts in browser history.
What role did Parisa Tabriz play in Google’s bug bounty program?
Tabriz was a key advocate and leader in expanding Google’s Vulnerability Reward Program (VRP) for Chrome. Under her guidance, the program significantly increased its maximum payouts — reaching up to $250,000 for critical Chrome vulnerabilities — attracting top-tier security researchers from around the world. She pushed for faster response times, clearer communication with researchers, and broader scope for the program. The Chrome VRP has paid out tens of millions of dollars in total, and the model it established has been widely adopted across the tech industry. Tabriz has spoken publicly about how bug bounty programs create a virtuous cycle: they incentivize talented researchers to find and report vulnerabilities rather than sell them on the black market, making everyone safer.