In 1994, a mathematician at AT&T Bell Labs published a paper that sent shockwaves through the worlds of computer science, mathematics, and national security simultaneously. Peter Shor demonstrated that a sufficiently powerful quantum computer could factor large integers in polynomial time — a feat that would render RSA encryption, the backbone of internet security, completely obsolete. Overnight, quantum computing went from being a theoretical curiosity explored by a handful of physicists to a strategic priority for governments and corporations around the globe. Shor’s algorithm didn’t just solve an abstract mathematical puzzle; it proved that quantum computers could do something no classical computer ever could, and in doing so, it redefined the entire landscape of computation and cryptography.
Early Life and Mathematical Foundations
Peter Williston Shor was born on August 14, 1959, in New York City. He grew up in Washington, D.C., in a household that valued intellectual pursuit. His father, S. W. Shor, was a corporate executive, and his mother had a background in education. From an early age, Peter exhibited an extraordinary aptitude for mathematics, the kind of intuitive grasp of abstract structures that teachers recognize immediately but struggle to nurture within a standard curriculum.
Shor attended Caltech for his undergraduate studies, earning a Bachelor of Science in Mathematics in 1981. At Caltech, he was immersed in an environment where physics and mathematics intersected constantly — a formative experience that would later prove crucial when he bridged the gap between quantum mechanics and computational complexity. He went on to MIT for his doctoral work, completing his Ph.D. in Applied Mathematics in 1985 under the supervision of Tom Leighton, who would later co-found Akamai Technologies. His dissertation focused on probabilistic analysis of bin-packing algorithms, a classical combinatorics problem far removed from quantum mechanics but deeply rooted in the kind of algorithmic thinking that would define his career.
After completing his doctorate, Shor joined AT&T Bell Labs, the legendary research institution that had already produced breakthroughs by luminaries like Claude Shannon and numerous Nobel laureates. Bell Labs provided the rare combination of intellectual freedom and world-class colleagues that allows fundamental research to flourish. It was here, surrounded by mathematicians, physicists, and computer scientists working at the frontiers of their disciplines, that Shor would make his most famous contribution.
The State of Quantum Computing Before Shor
To understand the magnitude of Shor’s achievement, it helps to appreciate the landscape of quantum computing in the early 1990s. The field was still in its infancy. Richard Feynman had proposed the idea of quantum simulation in 1982, suggesting that quantum systems might be best simulated by other quantum systems. David Deutsch at Oxford had formalized the concept of a universal quantum computer in 1985 and demonstrated that quantum parallelism could, in principle, offer computational advantages.
However, by the early 1990s, the practical advantages of quantum computing remained largely theoretical. Daniel Simon had shown a problem where quantum computers offered an exponential speedup over classical ones, but it was a contrived, artificial problem with no obvious real-world application. The question that haunted the field was deceptively simple: could a quantum computer solve any practical problem dramatically faster than a classical one?
Meanwhile, the complexity-theoretic landscape was well understood on the classical side. Alan Turing had laid the foundations of computability theory decades earlier, and researchers like Avi Wigderson were pushing the boundaries of what we understood about computational complexity and randomness. Integer factorization sat in an uncomfortable position — not known to be in P (solvable in polynomial time) on classical computers, but also not proven to be NP-complete. The best classical algorithms, like the general number field sieve, ran in sub-exponential but super-polynomial time. RSA encryption, designed by Ron Rivest, Adi Shamir, and Leonard Adleman, bet the security of the entire internet on the assumption that factoring large numbers was computationally intractable.
The Breakthrough: Shor’s Algorithm
In 1994, Peter Shor presented his algorithm at the IEEE Symposium on Foundations of Computer Science. The paper, titled “Algorithms for Quantum Computation: Discrete Logarithms and Factoring,” demonstrated that a quantum computer could factor an n-bit integer in O(n3) time using O(n) qubits — an exponential speedup over the best known classical algorithms. The result was electrifying.
Shor’s algorithm works by reducing the factoring problem to the problem of finding the period of a function, and then using the quantum Fourier transform to find that period efficiently. The elegance of the approach lies in how it exploits quantum superposition and interference to extract global properties of a function (its period) without having to evaluate the function at every possible input.
The Mathematical Core: Period Finding
The connection between factoring and period finding comes from number theory. To factor an integer N, you pick a random integer a less than N and compute gcd(a, N). If they share a common factor, you’ve already found a nontrivial factor. If not, you need to find the order r of a modulo N — that is, the smallest positive integer r such that ar ≡ 1 (mod N). Once you know r, if it is even, then ar/2 + 1 and ar/2 − 1 each share a nontrivial factor with N (with high probability), and you can extract it using the Euclidean algorithm.
Classical computers struggle with finding this period r because the function f(x) = ax mod N has a period that can be exponentially large, and there is no known classical shortcut. But a quantum computer can prepare a superposition of all possible inputs, evaluate the function in parallel, and then apply the quantum Fourier transform to extract the period from the interference pattern.
The Quantum Fourier Transform
The quantum Fourier transform (QFT) is the heart of Shor’s algorithm. It is the quantum analog of the discrete Fourier transform, but it operates on quantum amplitudes rather than classical data. The key insight is that while a classical DFT on N points requires O(N log N) operations, the quantum version can be performed on a quantum register of n = log2 N qubits using only O(n2) = O(log2 N) quantum gates — an exponential improvement.
The QFT transforms a quantum state encoding a periodic signal into one where the period can be read off by measurement. Specifically, if you have a state that is a superposition with period r, the QFT concentrates the probability amplitude on states that are multiples of N/r, allowing you to determine r through a classical post-processing step involving continued fraction expansion.
Here is a simplified representation of the quantum Fourier transform circuit for n qubits, expressed as a quantum circuit construction:
def quantum_fourier_transform(qubits, n):
"""
Apply the Quantum Fourier Transform to an n-qubit register.
The QFT maps computational basis states to frequency basis:
|j⟩ → (1/√N) Σ_k exp(2πijk/N) |k⟩ where N = 2^n
Circuit structure for n qubits:
- For each qubit j (from most significant to least):
1. Apply Hadamard gate to qubit j
2. Apply controlled phase rotations R_k from qubit j,
controlled by qubits j+1, j+2, ..., n-1
where R_k adds phase exp(2πi / 2^k)
- Reverse the order of qubits (SWAP operations)
"""
for j in range(n):
# Hadamard on qubit j creates superposition
hadamard(qubits[j])
# Controlled rotations: each subsequent qubit
# controls a finer phase rotation
for k in range(1, n - j):
# R_(k+1) rotation: phase angle = 2π / 2^(k+1)
controlled_phase_rotation(
control=qubits[j + k],
target=qubits[j],
angle=2 * math.pi / (2 ** (k + 1))
)
# Reverse qubit order to match standard DFT convention
for i in range(n // 2):
swap(qubits[i], qubits[n - 1 - i])
# Total gate count: n Hadamards + n(n-1)/2 controlled rotations
# = O(n^2) gates, exponentially fewer than classical O(N log N)Period Finding in Practice
The full period-finding subroutine combines several quantum and classical steps. Here is a conceptual implementation showing how the pieces fit together:
def shors_period_finding(a, N):
"""
Quantum period-finding subroutine for Shor's algorithm.
Given: integer a and composite number N (with gcd(a,N) = 1)
Returns: the order r of a modulo N (i.e., smallest r where a^r ≡ 1 mod N)
Steps:
1. Initialize two quantum registers
2. Create superposition in the first register
3. Compute modular exponentiation into second register
4. Apply QFT to the first register
5. Measure and use continued fractions to extract r
"""
# Choose n such that N^2 ≤ 2^n < 2*N^2 (for sufficient precision)
n = math.ceil(2 * math.log2(N))
Q = 2 ** n # Size of the first register
# STEP 1: Initialize |0⟩|0⟩ in two registers
# First register: n qubits, Second register: ceil(log2(N)) qubits
reg1 = quantum_register(n) # Input register
reg2 = quantum_register(n) # Output register
# STEP 2: Apply Hadamard to create uniform superposition
# |0⟩ → (1/√Q) Σ_{x=0}^{Q-1} |x⟩
apply_hadamard_all(reg1)
# STEP 3: Compute f(x) = a^x mod N into second register
# State becomes: (1/√Q) Σ_x |x⟩|a^x mod N⟩
# This uses O(n^3) gates via modular exponentiation circuit
modular_exponentiation(reg1, reg2, a, N)
# STEP 4: Apply QFT to first register
# Transforms periodic structure into peaks at multiples of Q/r
quantum_fourier_transform(reg1, n)
# STEP 5: Measure first register → get value m ≈ j*(Q/r)
m = measure(reg1)
# STEP 6: Classical post-processing
# Use continued fraction expansion of m/Q to find r
# m/Q ≈ j/r for some integer j, so convergents give r
fraction = continued_fraction_expansion(m, Q)
r_candidate = fraction.denominator
# Verify: check if a^r ≡ 1 (mod N)
if pow(a, r_candidate, N) == 1:
return r_candidate
# If verification fails, repeat with new measurement
# Success probability per trial is Ω(1/log(log(N)))
return None # Retry neededWhy Shor's Algorithm Matters for Cryptography
The practical implications of Shor's algorithm are profound and far-reaching. RSA encryption, which protects everything from online banking to government communications, relies on the computational difficulty of factoring large semi-primes (products of two large primes). A 2048-bit RSA key would take classical computers billions of years to crack. Shor's algorithm could do it in hours on a sufficiently large quantum computer.
The same algorithm extends to the discrete logarithm problem, which underpins Diffie-Hellman key exchange and elliptic curve cryptography — the other two pillars of modern public-key cryptography. Whitfield Diffie and Martin Hellman revolutionized secure communication with their key exchange protocol in 1976, but Shor's algorithm threatens to undo that revolution entirely.
This realization has driven the entire field of post-quantum cryptography, a global effort to develop cryptographic systems that remain secure even against quantum attackers. NIST launched its Post-Quantum Cryptography Standardization process in 2016, and in 2022 selected the first set of algorithms designed to withstand quantum attacks. Organizations like Toimi, which specializes in digital strategy and web development, understand that preparing for the post-quantum era is not a distant concern but an active area of technology planning that affects every digital business today.
Quantum Error Correction: Shor's Other Breakthrough
While Shor's algorithm grabbed headlines, his contributions to quantum error correction may prove equally important in the long run. In 1995, just a year after his factoring algorithm, Shor introduced the first quantum error-correcting code — the 9-qubit code, now known as the Shor code.
The problem of errors in quantum computation is fundamentally different from classical error correction. In classical systems, you can simply copy a bit and use majority voting to detect and correct errors. But quantum mechanics forbids copying quantum states (the no-cloning theorem), and measurement destroys quantum superposition. Many physicists believed these constraints made quantum error correction impossible.
Shor showed otherwise. His 9-qubit code encodes a single logical qubit into nine physical qubits in a way that can correct any single-qubit error — whether a bit flip, a phase flip, or any combination thereof. The code works by first protecting against bit flips (using a classical-style repetition code in quantum form) and then nesting that within a phase-flip protection layer. This hierarchical structure was a conceptual breakthrough that opened the door to fault-tolerant quantum computation.
Without error correction, quantum computers would be limited to computations short enough that decoherence and noise don't accumulate to the point of destroying the result. With Shor's error-correcting codes and their successors, it became theoretically possible to run quantum computations of arbitrary length, provided the physical error rate falls below a certain threshold. This threshold theorem, proved independently by several groups building on Shor's work, is what makes large-scale quantum computing a realistic engineering goal rather than a physical impossibility.
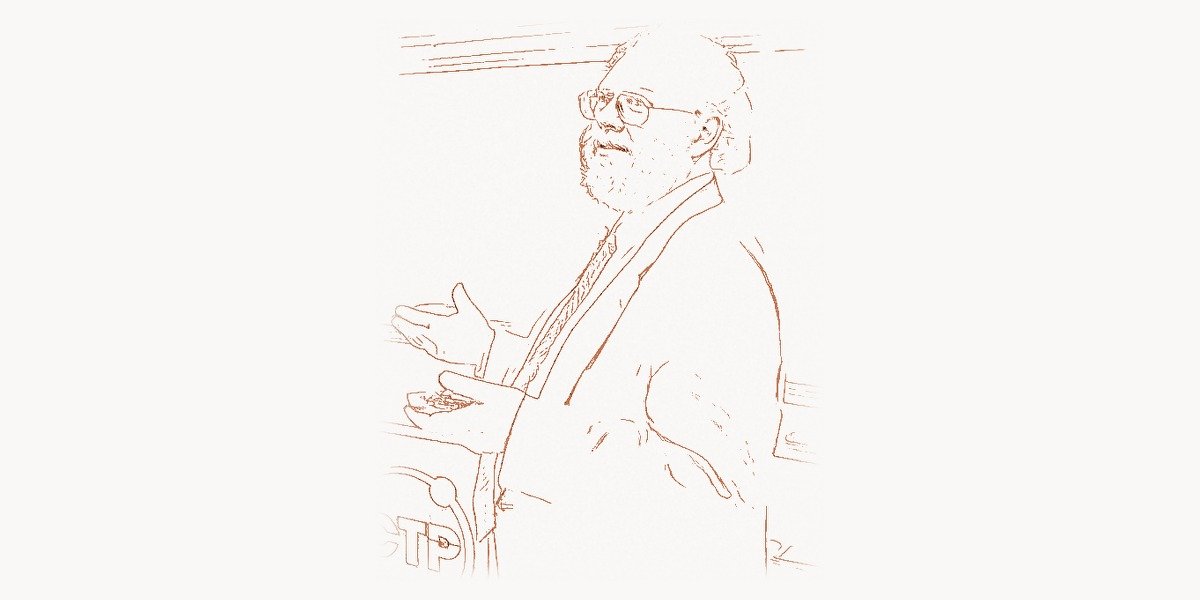
From Bell Labs to MIT
Shor spent nearly two decades at AT&T Bell Labs (which became AT&T Labs after the Bell System breakup), building a body of work that extended well beyond quantum computing. His research in combinatorial geometry and theoretical computer science earned him recognition as one of the most versatile mathematicians of his generation.
In 2003, Shor joined the faculty of MIT as the Morss Professor of Applied Mathematics, returning to the institution where he had earned his Ph.D. At MIT, he continued his research in quantum information theory while also mentoring the next generation of quantum computing researchers. His teaching reflects the same clarity of thought that characterizes his research — an ability to distill complex ideas to their essential structure without sacrificing rigor.
Managing the transition from a pure research environment to an academic one also meant engaging with the broader challenges of training quantum-ready talent. Developing effective educational programs for quantum computing requires sophisticated project management and a clear pedagogical strategy. Platforms like Taskee help educational teams coordinate curriculum development, track research milestones, and manage the complex logistics of interdisciplinary programs — precisely the kind of organizational challenge that quantum computing education presents.
Awards and Recognition
Shor's contributions have been recognized with virtually every major honor in mathematics and computer science:
- Nevanlinna Prize (1998) — awarded by the International Mathematical Union for outstanding contributions to mathematical aspects of information science
- MacArthur Fellowship (1999) — the so-called "genius grant," recognizing exceptional creativity and future potential
- Gödel Prize (1999) — for his quantum factoring algorithm, awarded jointly by EATCS and ACM SIGACT
- King Faisal International Prize (2002) — for his contributions to science
- Dirac Medal (2017) — from the International Centre for Theoretical Physics
- ACM A.M. Turing Award (2025) — shared with Lov Grover, for foundational contributions to quantum computation
- Breakthrough Prize in Fundamental Physics (2023) — recognizing his contributions to quantum information
The accumulation of these honors reflects a rare breadth of impact. Shor's work is recognized not just by computer scientists but by mathematicians and physicists as well, underscoring the fundamentally interdisciplinary nature of quantum information science.
The Race to Build a Quantum Computer
Shor's algorithm provided the motivation; building the hardware became the challenge. In the decades since 1994, an entire industry has emerged around the goal of constructing quantum computers powerful enough to run Shor's algorithm on cryptographically relevant numbers.
The first experimental demonstration came in 2001, when a team at IBM used a 7-qubit nuclear magnetic resonance (NMR) quantum computer to factor the number 15 into its prime factors 3 and 5. While this was a proof of concept rather than a practical threat, it demonstrated that Shor's algorithm was more than a theoretical exercise.
Since then, progress has been steady but challenging. Modern quantum computers from companies like IBM, Google, and IonQ have reached hundreds of qubits, but these are noisy physical qubits, not the error-corrected logical qubits that Shor's algorithm requires. Current estimates suggest that breaking RSA-2048 would require thousands of logical qubits, which in turn would need millions of physical qubits given current error rates. Researchers like Andrew Yao, a Turing Award laureate whose work on quantum computing theory has been foundational, continue to push the theoretical boundaries of what is achievable.
The gap between current capabilities and the requirements for cryptographically relevant quantum computing remains significant, but it is closing. Google's demonstration of quantum error correction improvements in 2024, where logical error rates decreased as the code distance increased, was a milestone that validated the theoretical framework Shor and others established decades ago.
Shor's Broader Contributions to Mathematics
While quantum computing dominates discussions of Shor's legacy, his mathematical contributions extend considerably further. His early work on bin-packing and probabilistic algorithms established him as a first-rate combinatorialist. He made significant contributions to computational geometry, including work on closest-pair problems and random convex hulls.
In quantum information theory beyond error correction, Shor made important contributions to understanding quantum channel capacities. His work on the additivity conjecture for quantum channels addressed fundamental questions about how much information can be transmitted through quantum communication systems. In 2008, Matthew Hastings disproved the additivity conjecture using techniques that built substantially on Shor's earlier work, marking a surprising result that the quantum capacity of two channels used together could exceed the sum of their individual capacities.
Shor also contributed to the study of entanglement, quantum key distribution, and the foundations of quantum mechanics. His breadth of contribution recalls earlier polymaths like John von Neumann, who similarly moved between pure mathematics, physics, and the theory of computation with remarkable fluency.
The Legacy and Future Impact
Peter Shor's influence on modern technology operates on multiple timescales. In the near term, the mere existence of his algorithm has driven billions of dollars of investment into post-quantum cryptography and quantum-safe infrastructure. Organizations worldwide are conducting "crypto-agility" audits and transitioning to quantum-resistant algorithms, even though a quantum computer capable of running Shor's algorithm on real cryptographic keys may still be years or decades away.
In the medium term, Shor's algorithm remains the benchmark against which quantum hardware progress is measured. Every advance in qubit count, error rates, and gate fidelity is implicitly evaluated against the question: how close are we to running Shor's algorithm at scale?
In the long term, Shor's most enduring contribution may be conceptual rather than algorithmic. He demonstrated, in the most concrete possible way, that quantum mechanics offers computational capabilities that transcend the classical Church-Turing thesis. This insight — that the physics of computation matters, and that different physical substrates can lead to fundamentally different computational power — has reshaped how we think about the relationship between physics, mathematics, and computer science. The work of Alonzo Church on lambda calculus gave us one model of computation; Shor showed that nature has richer models waiting to be exploited.
Today, Shor continues his research at MIT, working on quantum information theory and mentoring graduate students who will carry quantum computing forward. He remains active in the community, regularly giving talks and contributing to the ongoing dialogue about the future of quantum computation. His quiet, rigorous approach to mathematics stands as a model for a field that sometimes gets lost in its own hype.
In an era where quantum computing attracts enormous media attention and corporate investment, Peter Shor's work serves as a reminder that the most transformative breakthroughs often begin not with venture capital or press releases, but with a mathematician sitting quietly with a problem, finding the beautiful structure hidden within.
Frequently Asked Questions
What exactly does Shor's algorithm do?
Shor's algorithm efficiently factors large integers into their prime components using a quantum computer. It reduces the factoring problem to a period-finding problem, then uses the quantum Fourier transform to find that period exponentially faster than any known classical algorithm. For an n-bit number, it runs in O(n3) time on a quantum computer, compared to the sub-exponential time required by the best classical methods like the general number field sieve.
Can current quantum computers run Shor's algorithm to break encryption?
Not yet. While Shor's algorithm has been demonstrated on small numbers (IBM factored 15 in 2001), breaking RSA-2048 encryption would require approximately 4,000 error-corrected logical qubits, which translates to millions of physical qubits with current error correction overhead. As of 2025, the largest quantum processors have around 1,000 noisy physical qubits, still far from this threshold. However, the field is advancing rapidly, and most experts estimate that cryptographically relevant quantum computers could emerge within 10 to 30 years.
How does the quantum Fourier transform differ from the classical discrete Fourier transform?
Both transforms perform the same mathematical operation — converting signals from the time/position domain to the frequency domain. The critical difference is efficiency. The classical Fast Fourier Transform (FFT) on N data points requires O(N log N) operations. The quantum Fourier transform achieves the same transformation on a quantum register of n = log2 N qubits using only O(n2) = O(log2 N) quantum gates, an exponential speedup. However, the quantum version has a catch: you cannot directly read out all the Fourier coefficients because measurement collapses the quantum state. Shor's insight was designing an algorithm where a single measurement after the QFT reveals enough information to solve the problem.
What is the relationship between Shor's algorithm and post-quantum cryptography?
Shor's algorithm is the primary motivation for the entire field of post-quantum cryptography. Because it can efficiently break RSA, Diffie-Hellman, and elliptic curve cryptography — the three foundations of current public-key infrastructure — researchers have been developing new cryptographic systems based on mathematical problems that quantum computers cannot solve efficiently. These include lattice-based cryptography, hash-based signatures, code-based cryptography, and multivariate polynomial systems. NIST selected its first post-quantum standards (CRYSTALS-Kyber and CRYSTALS-Dilithium, among others) in 2022 to prepare for the eventual advent of large-scale quantum computers.
Besides the factoring algorithm, what are Peter Shor's other major contributions?
Shor made several other foundational contributions to quantum computing and mathematics. His 9-qubit quantum error-correcting code (1995) was the first demonstration that quantum error correction is possible, overcoming the no-cloning theorem. This work led to the threshold theorem for fault-tolerant quantum computation. He also contributed to quantum channel capacity theory, the study of entanglement, computational geometry, and combinatorial optimization. He shared the 2025 ACM Turing Award with Lov Grover for their collective impact on quantum computation.