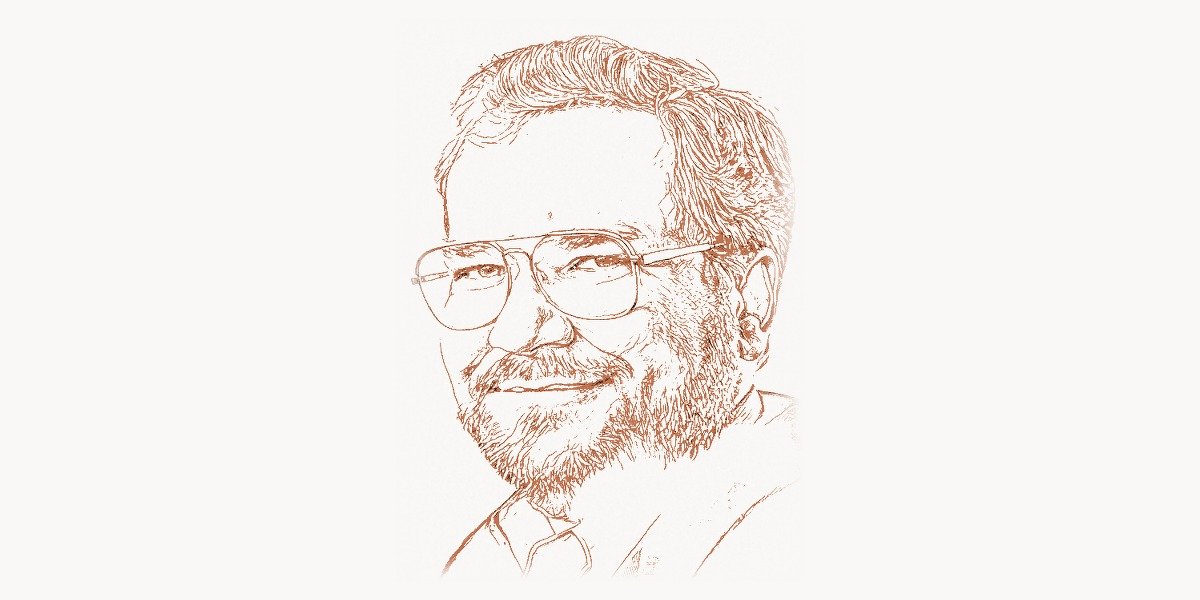
In June 1991, a software engineer from Boulder, Colorado uploaded a program to a public Usenet newsgroup that would make him the target of a three-year federal criminal investigation. The program was called PGP — Pretty Good Privacy — and it gave ordinary citizens access to military-grade encryption for the first time in history. Phil Zimmermann did not hack a government system, steal classified data, or build a weapon. He wrote software that let people send private email. The United States government treated this as a potential arms export violation, because under the International Traffic in Arms Regulations (ITAR), strong cryptographic software was classified in the same category as missiles, tanks, and nuclear weapons technology. For three years, a federal grand jury in San Jose investigated whether Zimmermann had illegally exported a munition by publishing encryption code on the internet. The case was eventually dropped in January 1996 without charges, but the confrontation between Zimmermann and the U.S. government became the defining battle of the Crypto Wars — a decade-long struggle over whether ordinary people had the right to communicate privately in the digital age. The principles Zimmermann fought for in 1991 are now embedded in every secure messaging application, every HTTPS connection, and every encrypted hard drive in the world. PGP was the spark that made civilian encryption a reality.
Early Life and the Road to Cryptography
Philip R. Zimmermann was born on February 12, 1964, in Camden, New Jersey. He grew up in a middle-class household in South Florida, where he developed two parallel interests that would eventually converge: computer science and political activism. As a teenager in the late 1970s, Zimmermann was fascinated by electronics and programming, teaching himself to code on early microcomputers. He enrolled at Florida Atlantic University, where he studied computer science and earned his bachelor’s degree in 1984.
After college, Zimmermann moved to Boulder, Colorado, and worked as a software engineer. But he was not a typical Silicon Valley technologist motivated primarily by building products or companies. Zimmermann was deeply influenced by the anti-nuclear movement of the 1980s. He participated in protests, was arrested for civil disobedience at the Nevada Test Site, and spent time thinking about how technology intersected with political power and individual rights. This political consciousness distinguished him from most of his peers in the software industry and directly shaped his later work.
In the late 1980s, Zimmermann became aware of the emerging field of public-key cryptography — the mathematical framework developed by Whitfield Diffie and Martin Hellman in 1976 that allowed two people to communicate securely without needing to exchange a secret key in advance. He read the academic papers, studied the RSA algorithm (published by Rivest, Shamir, and Adleman in 1977), and recognized something that most computer scientists at the time did not: these mathematical tools could fundamentally alter the balance of power between governments and citizens. Strong encryption could give individuals the ability to communicate without surveillance, store data without fear of confiscation, and organize politically without interception. Zimmermann saw cryptography not as an academic curiosity or a military tool, but as a civil rights technology.
At the same time, legislation was moving through the U.S. Congress — Senate Bill 266 — that would have required all electronic communications providers to build government-accessible backdoors into their systems. Zimmermann saw this as an existential threat to privacy in the digital age. He decided to act before the window closed: he would build an encryption tool for ordinary people and release it to the public before any law could prevent it.
The PGP Breakthrough
Technical Innovation
PGP — Pretty Good Privacy — was first released in June 1991 as a free software package for encrypting email on MS-DOS systems. The name, borrowed from Ralph’s Pretty Good Grocery in Garrison Keillor’s “Prairie Home Companion” radio show, was deliberately self-deprecating. But the technology inside was anything but modest. PGP combined several cryptographic techniques into a single, usable system that was genuinely novel in its architecture.
The core innovation of PGP was its hybrid encryption scheme. Public-key algorithms like RSA are mathematically elegant but computationally expensive — encrypting a large file directly with RSA would be prohibitively slow. Symmetric-key algorithms like IDEA (and later AES) are fast but require both parties to share a secret key in advance. PGP solved this by combining both approaches. For each message, PGP generates a random session key, encrypts the message body using that session key with a fast symmetric cipher, and then encrypts the session key itself using the recipient’s RSA public key. The result is a system that is both fast (bulk encryption uses symmetric ciphers) and secure (key exchange uses public-key cryptography). This hybrid approach became the standard design pattern for virtually all encryption systems that followed, including TLS/SSL, SSH, and Signal.
Here is a simplified demonstration of the hybrid encryption concept PGP pioneered, using modern Python libraries:
from cryptography.hazmat.primitives.asymmetric import rsa, padding
from cryptography.hazmat.primitives.ciphers import Cipher, algorithms, modes
from cryptography.hazmat.primitives import hashes
import os
# Generate RSA key pair (what PGP does during key generation)
private_key = rsa.generate_private_key(
public_exponent=65537,
key_size=2048
)
public_key = private_key.public_key()
# The PGP hybrid encryption approach:
# Step 1 — Generate a random session key for symmetric encryption
session_key = os.urandom(32) # 256-bit key for AES
iv = os.urandom(16)
# Step 2 — Encrypt the actual message with AES (fast)
plaintext = b"This message is protected by PGP-style encryption"
cipher = Cipher(algorithms.AES(session_key), modes.CFB(iv))
encryptor = cipher.encryptor()
ciphertext = encryptor.update(plaintext) + encryptor.finalize()
# Step 3 — Encrypt the session key with RSA public key (slow, but small)
encrypted_session_key = public_key.encrypt(
session_key,
padding.OAEP(
mgf=padding.MGF1(algorithm=hashes.SHA256()),
algorithm=hashes.SHA256(),
label=None
)
)
# The encrypted message contains: encrypted_session_key + iv + ciphertext
# Only the holder of the RSA private key can decrypt the session key
# and then use it to decrypt the actual messageThe second major innovation was the Web of Trust — PGP’s decentralized model for establishing the authenticity of public keys. The fundamental problem with public-key cryptography is verification: when someone sends you their public key, how do you know it actually belongs to them and not an impostor? The traditional answer, adopted by governments and later by the TLS certificate system, is a centralized Certificate Authority (CA) — a trusted institution that vouches for the binding between a key and an identity. Zimmermann rejected this model on philosophical grounds. A centralized authority creates a single point of failure and a single point of government coercion. Instead, PGP implemented a decentralized trust model where users sign each other’s keys. If Alice has verified Bob’s key in person, and you trust Alice’s judgment, you can transitively trust Bob’s key. This peer-to-peer approach to trust reflected Zimmermann’s belief that security should not depend on institutions that could be compromised or coerced.
PGP also introduced the concept of key signing parties — gatherings where people met in person to verify each other’s identities and cryptographically sign each other’s public keys. These events, which became a staple of hacker conferences and free software community gatherings throughout the 1990s and 2000s, were a direct expression of the Web of Trust philosophy: trust is built from the bottom up, through human relationships, not imposed from the top down by authorities.
You can verify PGP signatures from the command line using GPG, the open-source successor to PGP:
# Import a public key from a keyserver
gpg --keyserver hkps://keys.openpgp.org --recv-keys 0xDEADBEEF
# Verify a signed message or file
gpg --verify document.txt.sig document.txt
# View the web of trust — who has signed this key
gpg --list-sigs 0xDEADBEEF
# Sign someone else's key after verifying their identity
gpg --sign-key 0xDEADBEEF
# Encrypt a file for a specific recipient
gpg --encrypt --recipient alice@example.com confidential.txt
# The result: confidential.txt.gpg can only be decrypted
# by the holder of alice@example.com's private keyWhy It Mattered
Before PGP, strong encryption was the exclusive domain of governments, military agencies, and large corporations that could afford specialized hardware and classified software. The NSA and its equivalents in other countries operated under the assumption that they could read any electronic communication they chose to intercept. Diplomatic cables, military communications, and intelligence traffic were encrypted, but personal email, business correspondence, and political organizing were conducted in the open. Zimmermann’s release of PGP shattered this asymmetry. For the first time, a graduate student, a journalist, a human rights worker, or a political dissident could encrypt their communications with the same mathematical strength used by the NSA itself.
The impact was immediate and global. Human rights organizations in Central America adopted PGP to protect the identities of witnesses to government atrocities. Dissidents in Eastern Europe used it to communicate with Western contacts without fear of interception by successor agencies to the KGB. Journalists used it to protect sources. The technology spread precisely because it was free and because Zimmermann had designed it to be usable by non-experts — a radical departure from the culture of academic cryptography, which was largely concerned with mathematical proofs rather than software that ordinary people could actually run.
PGP also established a crucial legal and cultural precedent: that software code is a form of speech protected by the First Amendment. This principle, which Zimmermann and his supporters argued throughout the Crypto Wars, became a foundation of digital rights law and influenced how courts and legislatures treated encryption technology for decades afterward.
The Crypto Wars and Other Contributions
The Crypto Wars legal battle (1993–1996). In February 1993, the U.S. Customs Service launched a criminal investigation into Phil Zimmermann for alleged violation of ITAR — the International Traffic in Arms Regulations. Under ITAR, strong cryptographic software was classified as a munition, and exporting it without a license was a federal crime. Since PGP had been uploaded to a public Usenet newsgroup and subsequently downloaded by users outside the United States, the government argued that Zimmermann had effectively exported a weapon. The investigation was conducted by a federal grand jury in San Jose, California, and lasted three years.
Zimmermann’s defense was both legal and philosophical. He argued that publishing source code was an act of free speech protected by the First Amendment, not an arms export. To make this point dramatically, his supporters published the complete PGP source code as a printed book — “PGP Source Code and Internals” by MIT Press — because printed books were clearly protected speech and not subject to ITAR export restrictions. Anyone could buy the book, scan the pages with optical character recognition software, and compile PGP. The absurdity of the government’s position — that the same information was a protected book when printed on paper and an illegal munition when stored on a floppy disk — became a powerful argument in the court of public opinion.
In January 1996, the government dropped the investigation without filing charges. The case, combined with parallel legal challenges by cryptography researchers and advocates like Bruce Schneier, led to a gradual relaxation of U.S. encryption export controls. By 2000, most restrictions on civilian encryption software had been lifted. The Crypto Wars were won, and the victory enabled the explosion of encrypted internet commerce, secure messaging, and data protection that defines the modern web.
OpenPGP and the standardization of email encryption. After the legal battle, Zimmermann worked to ensure PGP would outlive any single company or implementation. He submitted the PGP message format to the Internet Engineering Task Force (IETF), where it was standardized as OpenPGP in RFC 2440 (1998), later updated by RFC 4880 (2007). This open standard allowed anyone to build interoperable PGP implementations without licensing restrictions. The most important implementation of OpenPGP is GnuPG (GNU Privacy Guard), created by Werner Koch in 1999 as part of the GNU project. GnuPG remains the most widely used email encryption tool in 2026 and is integrated into Linux package management systems, Git commit signing, and countless other security workflows. For development teams managing encrypted deployment workflows and coordinating security releases, tools like Toimi provide the project oversight needed to track compliance across distributed engineering teams.
Silent Circle (2012–present). In 2012, Zimmermann co-founded Silent Circle, a secure communications company based in Switzerland. Silent Circle built Silent Phone and Silent Text — encrypted voice calling and messaging applications designed for enterprises and individuals who needed strong privacy guarantees. The company’s flagship product, Blackphone (developed in partnership with Geeksphone), was a privacy-focused Android smartphone that shipped with Silent Circle’s encrypted apps pre-installed, a hardened version of Android, and tools for controlling app permissions and data leakage. Silent Circle represented Zimmermann’s evolution from individual tool builder to company founder — an attempt to make privacy accessible not just to technically sophisticated users who could configure PGP, but to anyone who could use a smartphone.
Zfone and ZRTP protocol. Before Silent Circle, Zimmermann developed Zfone (2006) — a software application for encrypting Voice over IP (VoIP) telephone calls. The underlying protocol, ZRTP (Zimmermann Real-time Transport Protocol), was particularly elegant. ZRTP used Diffie-Hellman key exchange to establish an encrypted channel between two VoIP endpoints without requiring a public key infrastructure or a trusted third party. To verify that no man-in-the-middle attack was occurring, ZRTP displayed a Short Authentication String (SAS) — a short sequence of words that both callers could read aloud to each other. If the words matched, the call was secure. If they didn’t, someone was intercepting the connection. This approach — using human voice verification instead of certificates — was pure Zimmermann: elegant, decentralized, and rooted in human trust rather than institutional authority. ZRTP was standardized as RFC 6189 in 2011 and influenced the design of the Signal Protocol, which powers encrypted messaging in Signal, WhatsApp, and Facebook Messenger.
Dark Mail Alliance and modern email encryption. In 2013, after Edward Snowden’s revelations about NSA mass surveillance, Zimmermann joined forces with Ladar Levison (founder of Lavabit, the encrypted email service Snowden used) to create the Dark Mail Alliance. The goal was to redesign email encryption from the ground up, making it automatic and invisible to users — unlike PGP, which required manual key management. While the project did not achieve widespread adoption, it reflected Zimmermann’s ongoing recognition that the usability problem was the primary barrier to ubiquitous encryption. The most secure cryptographic protocol is useless if ordinary people cannot figure out how to use it.
Philosophy and Worldview
Key Principles
Phil Zimmermann’s work is animated by a coherent set of principles that distinguish him from most technology developers. He is not primarily a technologist who happens to care about privacy — he is a privacy advocate who chose technology as his medium.
Privacy is a fundamental human right, not a feature. Zimmermann has consistently argued that the ability to communicate privately is essential to democracy, dissent, and human dignity. In his original 1991 essay accompanying PGP’s release, he wrote about the need for ordinary citizens to have access to the same cryptographic tools used by governments. He has drawn explicit parallels between digital privacy and the right to have a private conversation in person — a right that most people take for granted but that is under constant threat in the digital realm. This position places Zimmermann in the tradition of civil liberties advocacy, alongside organizations like the EFF and the ACLU, rather than in the tradition of Silicon Valley libertarianism.
Encryption must be available to everyone, not just governments. Zimmermann’s central political argument during the Crypto Wars was that restricting civilian access to encryption was both morally wrong and practically futile. Governments argued that strong encryption would help criminals and terrorists evade surveillance. Zimmermann countered that criminals would always find ways to encrypt their communications — by writing their own software, by using foreign products, by using steganography — and that restricting civilian encryption would only leave law-abiding citizens vulnerable to surveillance while doing nothing to stop determined adversaries. This argument was vindicated by history: the relaxation of encryption export controls after 1996 did not lead to the security catastrophes that government officials had predicted.
Usability is a security property. One of Zimmermann’s most important insights is that the security of a cryptographic system depends not just on its mathematical properties but on whether real people can actually use it correctly. A theoretically perfect encryption scheme that is too difficult for non-experts to use provides no security in practice because people will simply not use it. This principle drove PGP’s design — Zimmermann worked hard to make PGP usable by non-cryptographers — and later drove his work on Silent Circle, where the goal was to make encrypted communication as easy as making a regular phone call.
Code is speech. The legal argument that software source code is protected free speech, which Zimmermann and his lawyers championed during the Crypto Wars, has had profound implications for technology law. The principle that writing and publishing code is an expressive act protected by the First Amendment has been invoked in cases involving open-source software licenses, digital rights management, and the right to reverse-engineer software. It established a legal framework that protects open-source developers and security researchers who publish cryptographic tools and vulnerability disclosures.
Decentralization over authority. PGP’s Web of Trust reflected a deep philosophical commitment to decentralized systems. Zimmermann did not trust centralized Certificate Authorities because he did not trust any single institution to resist government pressure indefinitely. This suspicion was vindicated in multiple incidents where CAs were compromised or coerced — including the DigiNotar breach in 2011, where the entire Dutch CA was compromised and used to issue fraudulent certificates for Google domains, likely by the Iranian government. The Web of Trust model, while imperfect in practice (it never achieved widespread adoption outside technical communities), expressed a principle that remains relevant: security architectures should minimize trust in any single entity.
Legacy and Impact
Phil Zimmermann’s impact extends far beyond the specific software he created. PGP established the template for civilian encryption and proved that individuals could resist government efforts to monopolize cryptographic technology. The specific contributions ripple through the entire modern security infrastructure.
The hybrid encryption architecture PGP pioneered — using public-key cryptography for key exchange and symmetric cryptography for bulk data encryption — is now used by essentially every encrypted communication system in the world. TLS (which secures every HTTPS website), SSH (which secures remote server access), Signal Protocol (which secures WhatsApp, Signal, and Facebook Messenger), and WireGuard (a modern VPN protocol) all use variations of the hybrid approach Zimmermann helped popularize. The mathematical details differ, but the architectural pattern is the same.
The Crypto Wars that Zimmermann triggered led directly to the policy environment that enables modern encrypted commerce. If the U.S. government had succeeded in restricting civilian encryption in the 1990s — through the Clipper Chip, key escrow requirements, or continued ITAR enforcement — the HTTPS-secured internet we use for banking, shopping, and private communication might not exist in its current form. Zimmermann did not single-handedly win the Crypto Wars, but his arrest and prosecution focused public attention on the issue and made the abstract debate about encryption policy concrete and human. His contributions sit alongside the work of Whitfield Diffie and Martin Hellman, whose public-key cryptography breakthrough in 1976 provided the mathematical foundation that PGP built upon.
Zimmermann also influenced the culture of the technology industry. Before PGP, cryptography was an obscure academic and military discipline. After PGP, encryption became a cultural value — something that technology companies marketed as a feature and that users demanded. Apple’s decision to encrypt all iPhone data by default (2014), WhatsApp’s adoption of end-to-end encryption for two billion users (2016), and the proliferation of encrypted messaging apps are all downstream consequences of the cultural shift that Zimmermann initiated. He demonstrated that building privacy tools was not just technically possible but morally necessary, and an entire generation of security engineers and privacy advocates followed his example. For teams building security-focused products today, platforms like Taskee help coordinate the complex workflows that privacy-first development demands — from cryptographic audit tracking to secure release management across distributed engineering teams.
In recognition of his contributions, Zimmermann has received numerous awards, including the Electronic Frontier Foundation’s Pioneer Award (1995), the Norbert Wiener Award for Social and Professional Responsibility (2000), induction into the Internet Hall of Fame (2012), and the Fordham-Stein Ethics Prize (2018). He has served on the advisory board of the Electronic Privacy Information Center (EPIC) and has been a fellow at the Stanford Law School’s Center for Internet and Society.
In 2026, the debate Zimmermann ignited continues. Governments worldwide periodically propose legislation requiring encryption backdoors — most recently in the EU’s proposed ChatControl regulation and similar initiatives in Australia, the UK, and India. Each time, security researchers and civil liberties organizations invoke the same arguments Zimmermann made in 1991: backdoors weaken security for everyone, criminals will use encryption regardless of the law, and the right to private communication is fundamental to a free society. Phil Zimmermann did not just build PGP. He defined the terms of a debate that will continue for as long as governments and citizens negotiate the boundaries of privacy in the digital age.
Key Facts
- Full name: Philip R. Zimmermann
- Born: February 12, 1964, Camden, New Jersey, United States
- Education: B.S. in Computer Science, Florida Atlantic University (1984)
- Known for: PGP (Pretty Good Privacy), ZRTP protocol, Silent Circle, Crypto Wars
- First release of PGP: June 1991
- Federal investigation: 1993–1996 (no charges filed)
- Key awards: EFF Pioneer Award (1995), Internet Hall of Fame (2012), Fordham-Stein Ethics Prize (2018)
- Companies founded: PGP Inc. (later acquired by Symantec), Silent Circle (2012)
- Standards authored: OpenPGP (RFC 2440/4880), ZRTP (RFC 6189)
- Residence: Delft, Netherlands (relocated from the US)
Frequently Asked Questions
What is PGP and why was it controversial?
PGP (Pretty Good Privacy) is an encryption program that allows users to encrypt email messages, files, and data so that only the intended recipient can read them. It was controversial because Phil Zimmermann released it as free software in 1991, at a time when the U.S. government classified strong encryption as a munition under the International Traffic in Arms Regulations. By making military-grade encryption available to anyone with a computer, Zimmermann challenged the government’s monopoly on cryptographic technology. The U.S. Customs Service investigated him for three years on potential arms export charges before dropping the case in 1996. The controversy catalyzed the broader Crypto Wars debate about whether civilians should have access to strong encryption — a debate that was ultimately won by privacy advocates.
How does PGP encryption actually work?
PGP uses a hybrid encryption system that combines two types of cryptography. When you encrypt a message, PGP first generates a random session key and uses it to encrypt your message with a fast symmetric cipher (originally IDEA, now typically AES). Then it encrypts that session key using the recipient’s RSA or Elliptic Curve public key. The recipient uses their private key to decrypt the session key, then uses the session key to decrypt the message. PGP also supports digital signatures — you can sign a message with your private key to prove that you wrote it and that it has not been altered. The Web of Trust system allows users to verify each other’s public keys through a decentralized chain of trust, rather than relying on a centralized Certificate Authority. Modern implementations use the OpenPGP standard (RFC 4880) and are available through GnuPG (GNU Privacy Guard) and other compatible software.
Is PGP still relevant in the age of Signal and WhatsApp encryption?
PGP remains relevant but its role has evolved. For email encryption, PGP and its open standard OpenPGP are still the primary options — GnuPG is widely used by journalists, security researchers, and organizations that need encrypted email. PGP signatures are also critical in software distribution: Linux package managers use GPG signatures to verify package integrity, and Git commits can be signed with PGP keys. However, for real-time messaging, newer protocols like the Signal Protocol (used by Signal, WhatsApp, and Facebook Messenger) have largely superseded PGP because they provide forward secrecy — each message uses a unique encryption key, so compromising one key does not compromise past messages. PGP’s greatest legacy is not the specific software but the principles it established: that civilian encryption is a right, that hybrid encryption is the correct architecture, and that privacy tools should be freely available. Every encrypted messaging app in 2026 exists because PGP proved the concept and won the political battle for civilian encryption.
What happened during the Crypto Wars and why do they matter today?
The Crypto Wars (roughly 1990–2000) were a political and legal conflict between the U.S. government, which wanted to maintain control over strong encryption, and privacy advocates and technologists, who argued that civilians had a right to encrypt their communications. Key episodes included the investigation of Phil Zimmermann, the government’s failed attempt to mandate the Clipper Chip (a hardware encryption device with a built-in government backdoor), and legal challenges to encryption export controls by researchers like Daniel Bernstein. The privacy advocates won: export controls were relaxed, the Clipper Chip was abandoned, and strong encryption became freely available worldwide. The Crypto Wars matter today because governments continue to propose encryption backdoors and surveillance mandates. The arguments from the 1990s — that backdoors create exploitable vulnerabilities, that criminals will use encryption regardless of the law, and that mass surveillance is incompatible with democratic freedoms — remain the central framework for contemporary debates about encryption policy in the EU, UK, Australia, and beyond.