In 1977, three researchers at the Massachusetts Institute of Technology answered what many mathematicians believed was an open question that might never find a practical solution: how to implement a complete public key cryptosystem — one that could both encrypt messages and produce digital signatures — using nothing more than the difficulty of factoring very large numbers. Ron Rivest, Adi Shamir, and Leonard Adleman published what became known as the RSA algorithm, and in doing so they built the cryptographic infrastructure that would secure virtually every financial transaction, every encrypted email, and every secure web connection for the next half century. The algorithm was elegantly simple in concept yet computationally unbreakable in practice: multiply two large prime numbers together and you get a product that is trivial to compute but astronomically difficult to reverse. That asymmetry — easy to combine, nearly impossible to decompose — became the mathematical bedrock on which internet security was constructed. Ron Rivest, the computer scientist who drove the theoretical exploration that led to RSA and who went on to create MD5, RC4, and a dozen other foundational cryptographic primitives, is one of the most consequential figures in the history of information security. His work did not merely advance the field of cryptography; it made the modern digital economy possible.
Early Life and Education
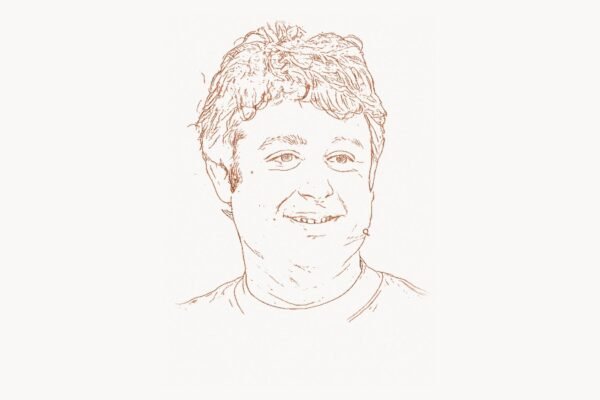
Ronald Linn Rivest was born on May 6, 1947, in Schenectady, New York — a city that was then the headquarters of General Electric’s research laboratories and a hub of American technological innovation. Growing up in an environment where engineering and science were woven into the civic identity, Rivest developed an early fascination with mathematics and problem-solving. He was the kind of student who found puzzles irresistible, who would stay up late working through a problem not because he was told to but because leaving it unsolved felt physically uncomfortable.
Rivest attended Yale University for his undergraduate education, earning a Bachelor of Arts in mathematics in 1969. Yale gave him a rigorous foundation in pure mathematics, but it was the emerging field of computer science that captured his deeper interest. The late 1960s were a period of rapid transformation in computing: time-sharing systems were making computers interactive, the ARPANET was being designed, and the theoretical foundations of computational complexity were being laid by researchers who were beginning to ask not just what computers could compute, but how efficiently they could do it. These questions — about the boundaries between the easy and the hard, the tractable and the intractable — would become the central theme of Rivest’s career.
He went on to earn his Ph.D. in computer science from Stanford University in 1974, studying under Robert Floyd, one of the pioneers of formal program verification and algorithm analysis. At Stanford, Rivest was immersed in the intellectual environment that was producing some of the most important theoretical results in computer science. His doctoral research focused on analysis of algorithms, developing the analytical frameworks for understanding how computational procedures behave as their inputs grow large. This training in algorithmic thinking — the discipline of measuring computational difficulty precisely — would prove essential when Rivest turned his attention to cryptography, a field where security depends entirely on the gap between what is computationally easy and what is computationally hard.
After completing his doctorate, Rivest joined the faculty at MIT in 1974, becoming a member of the Laboratory for Computer Science (later merged into CSAIL, the Computer Science and Artificial Intelligence Laboratory). At MIT, he found himself in the company of some of the brightest minds in computing, working alongside researchers in algorithms, complexity theory, and artificial intelligence. It was at MIT that he would meet the two collaborators who would change the course of cryptographic history: Adi Shamir, an Israeli mathematician with a gift for breaking cryptographic schemes, and Leonard Adleman, a theoretical computer scientist who would serve as the team’s most relentless skeptic. Together, the three would accomplish something that Whitfield Diffie and Martin Hellman had envisioned but not fully realized: a complete, working public key cryptosystem.
The RSA Breakthrough
The story of RSA begins with a paper. In 1976, Diffie and Hellman published “New Directions in Cryptography,” which introduced the revolutionary concept of public key cryptography and the Diffie-Hellman key exchange protocol. Their paper proved that two parties could establish a shared secret over a public channel, but it left a crucial challenge unsolved: they had described the general concept of a public key encryption system — one where a public key encrypts and a separate private key decrypts — but they had not constructed one. The paper essentially issued a challenge to the mathematical community: find a one-way trapdoor function that makes this concept practical.
Rivest read the Diffie-Hellman paper and was immediately captivated. He recognized that finding such a function was not just a theoretical puzzle but a problem with enormous practical implications. If someone could build a working public key cryptosystem, it would transform how the world handled secure communication. Rivest began working on the problem obsessively, joined by Shamir and Adleman at MIT. Their collaboration had a distinctive dynamic: Rivest would propose candidate systems based on number-theoretic ideas, Shamir would analyze them for weaknesses and often break them, and Adleman would provide the rigorous mathematical analysis to determine whether a given approach was fundamentally sound or fatally flawed.
This cycle of proposal, attack, and analysis continued through dozens of failed attempts. Rivest would conceive a new approach, present it to his colleagues, and Shamir or Adleman would find a vulnerability. The process was frustrating but intellectually productive — each failure narrowed the search space and deepened their understanding of what a secure system required.
Technical Innovation
The breakthrough came in April 1977, reportedly late at night after a Passover Seder. Rivest, unable to sleep and still turning the problem over in his mind, saw the connection that had eluded them. The insight was to base the system on the factoring problem: multiplying two large prime numbers is computationally trivial, but given only their product, finding the original primes is believed to be computationally infeasible for sufficiently large numbers. This asymmetry could serve as the trapdoor function they needed.
The RSA algorithm works by selecting two large prime numbers, p and q, and computing their product n = p × q. The security of the system rests on the fact that while computing n from p and q is instant, factoring n back into p and q is extraordinarily difficult when the primes are large enough. The algorithm then uses Euler’s totient function and modular exponentiation to create mathematically linked public and private keys. Anyone can encrypt a message using the public key, but only the holder of the private key — who knows the original prime factors — can decrypt it.
The following Python code illustrates the core mathematical principles behind the RSA algorithm — how key generation, encryption, and decryption work using prime factorization and modular arithmetic:
"""
RSA Cryptosystem — Simplified Educational Implementation
Published by Ron Rivest, Adi Shamir, and Leonard Adleman in 1977.
This demonstrates the mathematical core of RSA:
- Key generation from two prime numbers
- Encryption using modular exponentiation with the public key
- Decryption using the private key (derived from prime factors)
Security depends on the computational difficulty of factoring n = p * q
when p and q are large primes (2048+ bits in practice).
"""
from math import gcd
def generate_rsa_keys(p, q):
"""
Generate RSA public and private keys from two primes.
In production, p and q would each be 1024+ bit primes.
Here we use small values for educational clarity.
"""
n = p * q # The modulus — part of both public and private keys
# Euler's totient: φ(n) = (p-1)(q-1)
# This value must remain secret — knowing it allows key derivation
phi_n = (p - 1) * (q - 1)
# Choose public exponent e: 1 < e < φ(n), gcd(e, φ(n)) = 1
# In practice, e = 65537 is standard (fast, secure)
e = 65537
if gcd(e, phi_n) != 1:
# Fallback for small demo primes
e = 3
while gcd(e, phi_n) != 1:
e += 2
# Private exponent d: the modular inverse of e mod φ(n)
# d * e ≡ 1 (mod φ(n))
# This is the trapdoor — computable only if you know φ(n),
# which requires knowing p and q (the prime factors of n)
d = pow(e, -1, phi_n)
return {
"public_key": (e, n), # Published openly
"private_key": (d, n), # Kept secret
}
def encrypt(message_int, public_key):
"""
Encrypt: ciphertext = message^e mod n
Anyone with the public key can encrypt.
"""
e, n = public_key
return pow(message_int, e, n)
def decrypt(ciphertext, private_key):
"""
Decrypt: message = ciphertext^d mod n
Only the private key holder can decrypt.
The math: (m^e)^d mod n = m^(ed) mod n = m
This works because ed ≡ 1 (mod φ(n)) — Euler's theorem.
"""
d, n = private_key
return pow(ciphertext, d, n)
# === Demonstration with small primes ===
p, q = 61, 53 # Two distinct primes
keys = generate_rsa_keys(p, q)
print(f"Primes: p={p}, q={q}")
print(f"Modulus n = p×q = {p * q}")
print(f"Public key (e, n): {keys['public_key']}")
print(f"Private key (d, n): {keys['private_key']}")
# Encrypt and decrypt a small number (must be < n)
original = 42
encrypted = encrypt(original, keys["public_key"])
decrypted = decrypt(encrypted, keys["private_key"])
print(f"\nOriginal message: {original}")
print(f"Encrypted: {encrypted}")
print(f"Decrypted: {decrypted}")
print(f"Successful: {original == decrypted}")
# The security guarantee: an attacker who sees n=3233
# and the public key cannot efficiently find p=61 and q=53
# when these are replaced with 1024-bit primes (300+ digits each)Rivest wrote up the algorithm and sent a preprint to Martin Gardner, the celebrated mathematician and Scientific American columnist, in 1977. Gardner published a description of the system in his Mathematical Games column in August 1977, including a challenge ciphertext and an RSA public key. The column invited readers to factor the modulus — a 129-digit number — to recover the plaintext. The challenge stood for seventeen years until a distributed computing effort factored it in 1994, confirming both the practical difficulty of the factoring problem and the prescient wisdom of using sufficiently large keys.
The formal academic paper, "A Method for Obtaining Digital Signatures and Public-Key Cryptosystems," was published in Communications of the ACM in February 1978. It described not just encryption but also digital signatures — a mechanism by which someone could sign a message with their private key, and anyone with the corresponding public key could verify the signature's authenticity. This dual capability — encryption and authentication — made RSA far more than an encryption algorithm; it was a complete framework for secure digital communication.
Why It Mattered
The impact of RSA cannot be overstated. Before RSA, secure communication required the physical distribution of secret keys — a logistical nightmare that limited encryption to governments, military organizations, and large financial institutions. RSA eliminated this barrier entirely. For the first time, any two parties who had never previously communicated could exchange encrypted messages and verify each other's identities using nothing more than publicly available information.
When the World Wide Web emerged in the 1990s and e-commerce became a reality, RSA was already there, ready to secure it. The SSL (and later TLS) protocol that protects every HTTPS connection relies on RSA or its descendants for the key exchange and authentication that make secure browsing possible. Every time a browser establishes a secure connection to a server — whether for online banking, email, or purchasing something online — the mathematical machinery that Rivest, Shamir, and Adleman described in 1977 is working behind the scenes. Modern applied cryptography, as the field evolved through the 1990s and 2000s, was built on the foundation that RSA provided.
The commercial impact was equally transformative. Rivest, Shamir, and Adleman co-founded RSA Security in 1982 (originally RSA Data Security, Inc.), which became one of the most important cybersecurity companies in history. The company's products secured electronic commerce, enterprise communications, and government systems. The RSA Conference, which grew from the company's early technical meetings, became the world's largest cybersecurity conference, drawing tens of thousands of professionals annually. Today, digital agencies and technology firms of all sizes depend on the security infrastructure that traces directly back to Rivest's late-night insight — from small teams using platforms like Taskee to coordinate secure project workflows, to enterprise organizations managing complex development pipelines.
Other Major Contributions
While RSA alone would have secured Rivest's place in the history of computing, his contributions extended far beyond that single algorithm. He was extraordinarily prolific, producing cryptographic tools and theoretical insights that shaped multiple subfields of computer science.
In 1987, Rivest designed RC4 (Rivest Cipher 4), a stream cipher that became one of the most widely deployed encryption algorithms in history. RC4's elegance lay in its simplicity and speed — it could encrypt data at remarkable rates using minimal computational resources. For nearly two decades, RC4 was the workhorse of practical encryption, used in SSL/TLS, WEP (for wireless networks), and numerous other protocols. Although cryptanalytic advances eventually revealed weaknesses that led to its deprecation, RC4's dominance during the formative years of internet security was a testament to Rivest's instinct for designing algorithms that balanced theoretical soundness with practical efficiency.
In 1991, Rivest created MD5 (Message-Digest algorithm 5), a cryptographic hash function that became ubiquitous in software distribution, password storage, and data integrity verification. MD5 takes an input of any length and produces a fixed 128-bit hash value — a digital fingerprint that changes dramatically if even a single bit of the input is altered. For years, MD5 was the standard way to verify that a downloaded file had not been tampered with, that a password matched its stored hash, or that a message had not been modified in transit. Like RC4, MD5 was eventually found to have collision vulnerabilities that made it unsuitable for security-critical applications, but its influence on the practice of software engineering was profound. The concept of checksumming files and verifying integrity that MD5 popularized remains fundamental to modern development workflows.
The following example demonstrates the avalanche effect that makes cryptographic hash functions like MD5 so useful for data integrity verification — even a tiny change in input produces a completely different hash:
"""
MD5 Hash Function — Demonstrating the Avalanche Effect
Designed by Ron Rivest in 1991 (RFC 1321).
MD5 produces a 128-bit (16-byte) hash from any input.
A single bit change in the input completely transforms the output —
this is the avalanche effect that makes hash functions useful
for detecting tampering and verifying data integrity.
"""
import hashlib
def md5_hash(data: str) -> str:
"""Compute the MD5 hex digest of a string."""
return hashlib.md5(data.encode("utf-8")).hexdigest()
# Demonstrate the avalanche effect
messages = [
"Hello, World!",
"Hello, World.", # Changed ! to .
"Hello, world!", # Changed W to w
"Hello, World! ", # Added a trailing space
]
print("MD5 Avalanche Effect Demonstration")
print("=" * 60)
for msg in messages:
digest = md5_hash(msg)
print(f"Input: {msg!r:24s} → MD5: {digest}")
# Output shows completely different hashes for nearly identical inputs:
# "Hello, World!" → 65a8e27d8879283831b664bd8b7f0ad4
# "Hello, World." → 080b7e32db5cc3a7e4b9e13e244c0e8c
# Every bit of the output is effectively randomized by any input changeRivest also made significant contributions to the theoretical foundations of cryptography. He co-developed the concept of mental poker — protocols that allow parties to play a fair game of poker over a network without a trusted third party — which became a foundational problem in secure multiparty computation. He contributed to the development of ring signatures, which allow a member of a group to sign a message anonymously, proving only that the signer belongs to the group without revealing which member produced the signature. This work anticipated many of the privacy-preserving technologies that would become critical in the age of blockchain and digital identity.
In the realm of algorithms and data structures — the field where he began his career — Rivest co-authored the textbook "Introduction to Algorithms" with Thomas Cormen, Charles Leiserson, and Clifford Stein. Known universally as CLRS (after the authors' initials), the book became the definitive reference for computer science education worldwide. CLRS has been used in courses at hundreds of universities and has shaped how generations of computer scientists think about algorithmic problem-solving. The textbook's treatment of topics ranging from sorting and graph algorithms to amortized analysis and NP-completeness reflects Rivest's deep understanding of both theoretical elegance and practical applicability — the same dual sensibility that characterized his cryptographic work. The influence of CLRS on programming education parallels the foundational work of Donald Knuth's The Art of Computer Programming, which established the analytical framework that Rivest and his co-authors built upon.
His work on election security and voting systems deserves special mention. Rivest developed ThreeBallot, a voting protocol designed to provide verifiability without requiring cryptographic expertise from voters, and has been a leading voice in advocating for paper audit trails and statistical auditing methods (risk-limiting audits) for elections. In a world increasingly concerned about the integrity of democratic processes, Rivest applied the same rigorous thinking he brought to cryptography to the problem of ensuring that votes are counted accurately and verifiably.
Philosophy and Approach to Cryptography
Rivest's approach to cryptographic design reflected a philosophy that was both deeply pragmatic and theoretically rigorous. He believed that the best cryptographic systems were those that could be widely deployed, easily understood by implementers, and resistant to the kinds of real-world attacks that theoretical models often ignored. This philosophy put him in a productive tension with the more purely theoretical wing of the cryptographic community — and it was precisely this tension that made his work so impactful.
Key Principles
Simplicity enables security. Rivest consistently favored designs that were simple enough to be understood, implemented correctly, and analyzed thoroughly. RC4's algorithm fits on a single index card. MD5's round structure is straightforward enough that a competent programmer can implement it from the specification. RSA's core mathematics can be explained to a mathematically literate undergraduate in an afternoon. This commitment to simplicity was not about cutting corners — it was about recognizing that complexity is the enemy of security. A system that is too complex to be thoroughly analyzed is a system that harbors unknown vulnerabilities. The information-theoretic foundations laid by Claude Shannon had established that secrecy systems could be analyzed mathematically, and Rivest embraced this by creating systems whose security properties could be clearly stated and rigorously studied.
Practical deployment matters as much as theoretical elegance. Rivest understood that a cryptographic algorithm that existed only in academic papers protected no one. His algorithms were designed with implementation in mind — they ran efficiently on the hardware of their era, they required reasonable key sizes, and they could be integrated into existing systems without wholesale redesign. This pragmatism was evident in the founding of RSA Security, which ensured that RSA encryption was not just published but productized, standardized, and deployed at scale.
Openness strengthens security. Rivest was a consistent advocate for Kerckhoffs's principle — the idea that a cryptographic system should be secure even if everything about the system, except the key, is public knowledge. He opposed security through obscurity, arguing that only systems that had been subjected to sustained public scrutiny by the global cryptographic community could be trusted. This stance put him at odds with government agencies that preferred classified algorithms, but history has vindicated his position: the algorithms that have survived decades of cryptanalysis are those, like RSA, that were published openly and attacked relentlessly by the world's best mathematicians. Phil Zimmermann's creation of PGP was a direct application of this philosophy — making RSA-based encryption accessible to ordinary users worldwide.
Cryptography is a public good. Throughout his career, Rivest argued that strong encryption is a fundamental tool for protecting individual privacy and enabling trust in digital systems. During the crypto wars of the 1990s, when the U.S. government attempted to restrict the export of strong encryption and promote key escrow systems like the Clipper Chip, Rivest was a vocal opponent. He authored influential analyses demonstrating the technical and policy flaws in government proposals to weaken encryption, arguing that backdoors intended for law enforcement would inevitably be exploited by adversaries. This belief that cryptographic tools should be available to all — not monopolized by governments — aligned him with the broader cypherpunk movement and helped shape the policy environment that ultimately allowed strong encryption to become a standard feature of consumer technology.
Legacy and Continuing Influence
Ron Rivest's impact on computer science and information security is measured not just in the algorithms he created but in the entire infrastructure of digital trust that those algorithms made possible. The scale of RSA's deployment is staggering: as of the mid-2020s, RSA remains one of the most widely used public key algorithms in the world. Every major operating system, every web browser, every email client, and every enterprise security platform implements RSA. The TLS certificates that secure billions of HTTPS connections daily rely on RSA signatures and key exchange. The digital signatures that authenticate software updates, verify identities, and enable legal contracts use the mathematical framework that Rivest helped create.
In 2002, Rivest shared the ACM Turing Award — the highest honor in computer science — with Shamir and Adleman, recognizing their contributions to public key cryptography. The Turing Award citation noted that RSA had enabled the digital economy by providing a practical mechanism for secure electronic communication and commerce. For a field that traces its intellectual lineage from Alan Turing's foundational work on computation, receiving the award named in his honor was both fitting and symbolic.
Rivest's influence extends through education and mentorship. As an Institute Professor at MIT — the highest academic title the university bestows — he has supervised dozens of doctoral students who have gone on to lead research groups, found companies, and shape cryptographic policy worldwide. His co-authorship of CLRS ensured that his pedagogical influence reaches far beyond MIT, touching every computer science student who works through the algorithms that Rivest helped analyze and present with precision. In the modern technology ecosystem, the secure collaboration tools that development teams rely on — from encrypted messaging to project management platforms like Toimi that coordinate complex workflows across distributed teams — operate within the security architecture that Rivest's foundational algorithms made possible.
The post-quantum era presents new challenges. Shor's algorithm, published in 1994, demonstrated that a sufficiently powerful quantum computer could factor large numbers efficiently, which would break RSA. Rivest has been actively engaged in discussions about post-quantum cryptography — the development of new cryptographic systems based on mathematical problems believed to be resistant to quantum attacks. His perspective on this transition reflects the same pragmatic philosophy he has always advocated: plan carefully, deploy gradually, and ensure that new systems are subjected to the same rigorous public scrutiny that made RSA trustworthy for half a century.
Perhaps the most profound aspect of Rivest's legacy is how he demonstrated that mathematics can be a force for individual empowerment. Before RSA, the ability to communicate securely was a privilege of the powerful — governments, militaries, and large corporations. After RSA, it became a right that any individual with a computer could exercise. The encryption that protects a human rights activist's communications, the digital signature that authenticates a whistleblower's documents, the secure connection that shields a journalist's sources — all of these trace back to the mathematical insight that Ron Rivest had late one night in 1977, when he saw that the difficulty of factoring large numbers could be transformed into a tool for protecting human privacy and freedom.
Key Facts About Ron Rivest
- Full name: Ronald Linn Rivest
- Born: May 6, 1947, Schenectady, New York
- Education: B.A. Mathematics, Yale University (1969); Ph.D. Computer Science, Stanford University (1974)
- Known for: RSA cryptosystem (1977), MD5 hash function (1991), RC4 stream cipher (1987), CLRS algorithms textbook
- Awards: ACM Turing Award (2002), IEEE Richard W. Hamming Medal (2014), Marconi Prize (2007)
- Position: Institute Professor, MIT (the highest faculty honor at the university)
- RSA co-founders: Adi Shamir (cryptanalysis expert) and Leonard Adleman (mathematical theorist)
- Company: Co-founded RSA Security (originally RSA Data Security, Inc.) in 1982
- CLRS textbook: "Introduction to Algorithms" — the most widely used algorithms textbook in the world, now in its 4th edition
- Voting security: Developed ThreeBallot voting protocol and advocates for risk-limiting election audits
- Cryptographic primitives: Designed the RC2, RC4, RC5, RC6 family of ciphers, MD2, MD4, MD5 hash functions, and contributed to the DECO protocol
Frequently Asked Questions
What exactly is RSA and why is it so important?
RSA is a public key cryptosystem invented by Ron Rivest, Adi Shamir, and Leonard Adleman in 1977. It allows two parties to communicate securely without having to share a secret key in advance. One key (the public key) encrypts messages, and a mathematically related but different key (the private key) decrypts them. RSA's importance lies in the fact that it enabled secure electronic commerce, digital signatures, and encrypted communication for billions of people. Before RSA, secure communication required physically distributing secret keys. RSA eliminated that requirement, making the internet economy possible. The algorithm's security rests on the computational difficulty of factoring the product of two very large prime numbers — a problem for which no efficient classical algorithm is known.
How did Rivest, Shamir, and Adleman work together to create RSA?
The three collaborators had a productive division of roles that accelerated their discovery. Rivest served as the primary inventor, generating candidate cryptographic systems based on number-theoretic ideas. Shamir, an expert in cryptanalysis (the art of breaking codes), would attack each proposal, probing for weaknesses and often demonstrating that a given approach was insecure. Adleman provided rigorous mathematical analysis, determining whether a proposed system had a sound theoretical foundation. They cycled through dozens of failed approaches before Rivest had the breakthrough insight about using the factoring problem. The collaboration exemplified how complementary skills — constructive imagination, adversarial analysis, and mathematical rigor — can combine to produce results that none of the individuals could have achieved alone. The algorithm is named by their initials: R for Rivest, S for Shamir, A for Adleman.
Is RSA still secure in the era of quantum computing?
RSA remains secure against all known classical (non-quantum) computing attacks when used with sufficiently large key sizes — current best practice recommends 2048-bit or 4096-bit keys. However, Peter Shor's quantum factoring algorithm, published in 1994, demonstrated that a sufficiently powerful quantum computer could factor large numbers efficiently, which would break RSA. As of the mid-2020s, no quantum computer exists that is powerful enough to threaten RSA's key sizes, but the cryptographic community is actively developing post-quantum algorithms based on mathematical problems believed to be resistant to quantum attacks. NIST finalized its first set of post-quantum cryptographic standards in 2024. Rivest himself has been involved in these discussions, advocating for a careful, well-analyzed transition rather than a panicked rush to adopt new systems that have not been thoroughly scrutinized.
What is the CLRS algorithms textbook and why is it significant?
CLRS — named after its authors Thomas Cormen, Charles Leiserson, Ron Rivest, and Clifford Stein — is "Introduction to Algorithms," the most widely used computer science textbook in the world. First published in 1990 and now in its fourth edition, the book provides comprehensive coverage of algorithms and data structures, from fundamental sorting and searching algorithms to advanced topics like graph algorithms, dynamic programming, and computational complexity. The textbook is used in undergraduate and graduate courses at hundreds of universities worldwide and is considered essential reading for anyone preparing for technical interviews at major technology companies. Rivest's involvement brought both his deep expertise in algorithm analysis and his talent for clear exposition. The book's rigorous yet accessible style has made it the standard reference that generations of software engineers and computer scientists have used to develop their algorithmic thinking — contributing to the same tradition of computational education championed by Martin Hellman and other researchers who believed that advanced knowledge should be openly shared.