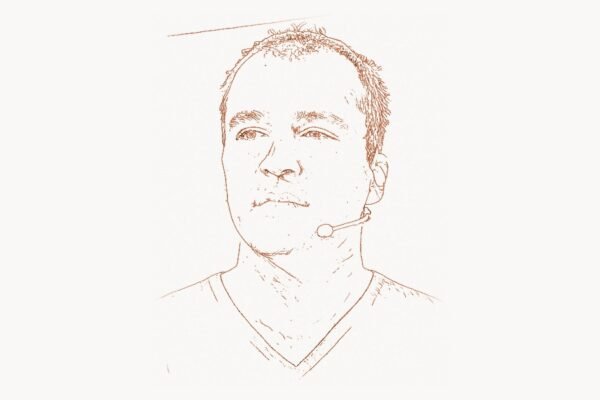
In the world of cybersecurity, most researchers quietly patch bugs and file advisories that few outside the industry ever notice. Tavis Ormandy is not most researchers. A senior security researcher at Google Project Zero, Ormandy has spent over a decade methodically dismantling the security assumptions of some of the world’s most widely-deployed software — from the Windows kernel itself to the very antivirus products meant to protect it. His disclosures have forced billion-dollar companies to scramble emergency patches, reshaped how the industry thinks about attack surfaces, and demonstrated that security software can itself be the weakest link. What makes Ormandy unusual is not just his technical virtuosity, but his willingness to publicly document and share his findings, turning vulnerability research into a form of accountability that benefits hundreds of millions of users worldwide.
Early Life and Education
Tavis Ormandy grew up in the United Kingdom, developing an early fascination with computers and low-level systems programming. By his teenage years he was already active in the security research community, contributing to open-source security tools and participating in vulnerability disclosure discussions on mailing lists like Full Disclosure and Bugtraq. Unlike many of his contemporaries who followed traditional academic paths into computer science, Ormandy was largely self-taught in the art of reverse engineering and exploit development, honing his skills through hands-on experimentation with real-world software.
Ormandy’s early background in Linux systems administration and kernel development gave him a deep understanding of operating system internals — knowledge that would prove essential to his later work dissecting complex software at the binary level. He developed an intuition for where software was likely to be fragile, learning to think like both a developer and an attacker simultaneously. This dual perspective, understanding how code is built and how it can break, became the foundation of his research methodology.
Career and Technical Contributions
Ormandy’s professional security career began at Google, where he initially worked on infrastructure security before becoming one of the founding members of Google Project Zero in 2014. Project Zero was established as an elite team of security researchers given the freedom to find and report zero-day vulnerabilities in any software, not just Google’s own products. The team’s mission was based on a simple premise: the security of Google’s users depends on the security of the entire software ecosystem. Ormandy embraced this mission with extraordinary productivity.
His early work at Google focused on Linux kernel security and the security of widely-used open-source libraries. He discovered critical vulnerabilities in glibc, OpenSSL, and numerous other foundational components of the internet infrastructure. But it was his auditing of closed-source commercial software, particularly on Windows, that brought him widespread attention. Ormandy demonstrated a remarkable ability to find severe vulnerabilities in software that had been reviewed by the vendors’ own security teams, often within hours or days of beginning an audit. His work drew comparisons to pioneers like Bruce Schneier, who similarly challenged the industry’s assumptions about what constituted adequate security.
Technical Innovation: Dismantling Antivirus Security
Perhaps Ormandy’s most impactful and controversial line of research was his systematic audit of antivirus products. Beginning around 2015, he published a series of devastating findings showing that major antivirus engines — from Symantec, Kaspersky, ESET, Avast, Comodo, and others — contained critical vulnerabilities that could be exploited remotely, often without any user interaction. The irony was sharp: the software users installed specifically to protect themselves was actually expanding their attack surface.
Ormandy’s research revealed a pattern of systemic problems. Antivirus engines, by their nature, must parse every file format imaginable — archives, documents, executables, email attachments — and they do so with the highest system privileges. Many of these parsers were written in C or C++ without modern exploit mitigations, running as SYSTEM on Windows or root on Linux. Ormandy found that many antivirus products disabled ASLR (Address Space Layout Randomization) and DEP (Data Execution Prevention) in their own processes, effectively undoing the operating system’s built-in protections.
A particularly striking example was his 2016 audit of Symantec/Norton products. He found that Symantec used an ancient version of the libmspack library to decompress archives, running the parsing code in the kernel via a custom driver. A malformed archive file sent as an email attachment could trigger a buffer overflow in the kernel, giving an attacker complete control of the system before the user even opened the message. Here is a simplified representation of the type of vulnerability pattern Ormandy documented:
/*
* Simplified example illustrating the vulnerability pattern
* Ormandy found in kernel-level archive parsers.
* Real-world AV engines parsed untrusted archives at ring 0.
*/
#include <stdio.h>
#include <string.h>
#define HEADER_MAGIC 0x4D53
#define MAX_FILENAME 256
struct archive_header {
unsigned short magic;
unsigned int filename_len; /* attacker-controlled */
unsigned int data_len;
/* ... */
};
int parse_archive_entry(const unsigned char *buf, size_t buf_len) {
struct archive_header *hdr = (struct archive_header *)buf;
char filename[MAX_FILENAME];
if (hdr->magic != HEADER_MAGIC)
return -1;
/*
* BUG: filename_len is read directly from the untrusted
* archive header without validation against MAX_FILENAME.
* In a kernel-mode driver, this overflow grants ring-0
* code execution to a remote attacker.
*/
memcpy(filename, buf + sizeof(*hdr), hdr->filename_len);
filename[hdr->filename_len] = '\0';
printf("Extracting: %s\n", filename);
return 0;
}This pattern — parsing attacker-controlled data with insufficient bounds checking at the highest privilege level — was endemic across the antivirus industry. Ormandy’s disclosures forced vendors to fundamentally rearchitect their products, moving parsing into sandboxed processes and enabling modern exploit mitigations. The research had direct parallels to the philosophy of defense-in-depth advocated by cryptographers like Whitfield Diffie and Daniel J. Bernstein, who long argued that security must be built into the architecture, not bolted on as an afterthought.
Why It Mattered
The impact of Ormandy’s antivirus research extended far beyond individual bug fixes. It fundamentally changed how the security community evaluated endpoint protection products. Before his work, the conventional wisdom was simple: install antivirus software and you are safer. Ormandy demonstrated that the reality was far more nuanced — that poorly-engineered security software could make systems less secure, not more. This insight influenced procurement decisions at enterprises worldwide and pushed antivirus vendors to adopt practices already standard in other areas of software development: fuzzing, sandboxing, memory-safe parsing, and regular third-party security audits.
His work also catalyzed a broader movement toward measuring security software by its actual security properties rather than its marketing claims. Projects like Taskee reflect this same ethos of accountability and measurable quality in software tools — the principle that tools should be evaluated by what they actually deliver, not what they promise. For teams managing complex security audit workflows, platforms like Toimi help coordinate the kind of systematic vulnerability tracking that Ormandy’s research demands.
Other Notable Contributions
Beyond antivirus research, Ormandy has compiled an impressive record of high-impact vulnerability discoveries across the software landscape. His findings in the Windows kernel and win32k graphics subsystem exposed fundamental design problems in one of the world’s most widely deployed operating systems. He discovered critical remote code execution vulnerabilities in password managers including LastPass, revealing that the browser extensions meant to strengthen authentication could themselves be exploited to steal credentials.
Ormandy’s work on the Cloudflare memory leak (known as “Cloudbleed”) in February 2017 was another landmark disclosure. He discovered that Cloudflare’s edge servers were leaking sensitive data — including authentication tokens, cookies, and private API keys — from the memory of one customer’s request into the responses served to other customers. The bug affected millions of websites simultaneously. Ormandy identified the issue, reported it to Cloudflare, and worked with the company to coordinate a rapid response, demonstrating the responsible disclosure methodology that has become a hallmark of Project Zero’s approach.
He also made significant contributions to open-source security tooling. His work on fuzzing infrastructure and automated vulnerability detection helped establish techniques that are now standard practice in the industry. Ormandy is a proponent of using automated tools to scale vulnerability research, recognizing that manual code review alone cannot keep pace with the volume of code being produced. Here is an example of a basic fuzzing harness configuration similar to what security researchers use for automated vulnerability discovery:
# Simplified example of a coverage-guided fuzzing harness
# for testing file parser libraries (inspired by Ormandy's
# approach to auditing antivirus file parsers)
import atheris
import sys
# Target: a hypothetical archive-parsing library
import archive_parser
def fuzz_target(data: bytes) -> None:
"""
Feed random mutations into the parser.
The fuzzer tracks code coverage to guide
mutations toward unexplored code paths.
"""
try:
parser = archive_parser.ArchiveReader()
parser.parse(data)
for entry in parser.entries():
_ = entry.filename
_ = entry.decompress()
except (archive_parser.InvalidArchive,
archive_parser.CorruptedEntry):
# Expected exceptions — parser handled bad input
pass
# Any other exception (segfault, assert, OOM)
# is caught by the fuzzer as a potential bug
if __name__ == "__main__":
atheris.Setup(sys.argv, fuzz_target)
atheris.Fuzz()Ormandy’s contributions to the security research community also include his prolific writing on the Project Zero blog, where he has documented his research methodology in detail, enabling other researchers to learn from and build upon his techniques. This commitment to open knowledge sharing echoes the philosophy of security researchers like Kevin Mitnick, who similarly believed that understanding attack techniques is the foundation of effective defense.
Philosophy and Key Principles
Ormandy’s approach to security research is guided by several core principles that distinguish his work from the broader vulnerability research community.
Complexity is the enemy of security. Throughout his career, Ormandy has argued that the most dangerous vulnerabilities arise not from individual coding mistakes but from architectural decisions that create unnecessary complexity. Antivirus products that parse hundreds of file formats in kernel mode, password managers that inject JavaScript into every web page, CDN edge servers that perform content transformation on the fly — each of these architectural choices creates an attack surface that is disproportionate to the functionality provided. Ormandy’s research consistently demonstrates that reducing complexity, rather than adding more security layers, is the most effective way to improve security. This echoes the design philosophy that guided Theo de Raadt in building OpenBSD, where minimizing code and reducing privilege have always been the primary security strategies.
Transparency drives improvement. Ormandy is a strong advocate for public disclosure of vulnerability details after vendors have had a reasonable window to develop patches. He has argued that the practice of silently fixing bugs without disclosing them — common among many software vendors — deprives users of the information they need to assess risk and makes the entire ecosystem less secure. Project Zero’s 90-day disclosure deadline, which Ormandy has consistently supported, creates accountability by ensuring that vendors cannot indefinitely delay patches for known vulnerabilities.
Security must be measured, not assumed. Ormandy has repeatedly demonstrated that software reputation and market position are poor proxies for actual security quality. Products from the largest, most established vendors have often proved to contain the most severe vulnerabilities. This principle — that security claims must be verified through rigorous testing — is a direct challenge to the marketing-driven approach that has historically dominated the endpoint security market.
Attackers think in systems, not in silos. One of Ormandy’s recurring themes is that security must be evaluated holistically. A vulnerability in a browser extension, a kernel driver, or a cloud edge server can have consequences far beyond the immediate component. His work has consistently demonstrated that the most dangerous bugs occur at the interfaces between systems, where assumptions made by one component are violated by another.
Legacy and Impact
Tavis Ormandy’s influence on the cybersecurity landscape is both broad and deep. His work has directly improved the security of software used by billions of people. The vulnerabilities he discovered in Windows, antivirus products, password managers, and cloud infrastructure prompted emergency patches that closed attack vectors used (or potentially usable) by nation-state adversaries and cybercriminals alike.
More broadly, Ormandy has helped shift the culture of the security industry. His antivirus research broke the implicit taboo against publicly criticizing security vendors, establishing the principle that security products should be held to at least as high a standard as the software they claim to protect. This cultural shift has made the endpoint security market more competitive and ultimately more honest, benefiting consumers and enterprises alike.
His work at Project Zero has also validated the model of vendor-independent vulnerability research as a public good. By demonstrating that a small team of talented researchers, given the freedom and resources to investigate any software, can dramatically improve the security of the entire ecosystem, Ormandy and his colleagues have inspired similar initiatives at other technology companies and within government agencies. The influence is comparable to how Linus Torvalds demonstrated that open, collaborative development could produce an operating system rivaling commercial alternatives — Ormandy showed that open, transparent security research could outperform the closed models that preceded it.
Ormandy remains active at Google Project Zero, continuing to find and disclose critical vulnerabilities. His recent work has expanded into areas such as CPU microarchitectural vulnerabilities and hardware security, reflecting the evolving threat landscape. As software systems grow more complex and more deeply embedded in every aspect of modern life, the kind of rigorous, fearless security research that Ormandy represents becomes not just valuable but essential.
Key Facts
| Category | Details |
|---|---|
| Full Name | Tavis Ormandy |
| Nationality | British |
| Known For | Google Project Zero, antivirus vulnerability research, Cloudbleed discovery, Windows kernel security |
| Employer | Google (Project Zero) |
| Project Zero Founded | 2014 |
| Major Disclosures | Symantec/Norton kernel bugs, LastPass RCE, Cloudbleed, Comodo sandbox escapes, ESET parser flaws |
| Research Areas | Vulnerability research, reverse engineering, fuzzing, exploit development, OS kernel security |
| Disclosure Policy | 90-day coordinated disclosure (Project Zero standard) |
| Notable Open Source | Contributions to fuzzing tools and vulnerability analysis frameworks |
| Active Since | Mid-2000s |
Frequently Asked Questions
What is Google Project Zero and what role does Tavis Ormandy play?
Google Project Zero is an elite security research team at Google, founded in 2014, with the mandate to find zero-day vulnerabilities in any widely-used software, regardless of the vendor. The team operates on the principle that improving the security of the broader software ecosystem protects Google’s own users. Tavis Ormandy is one of the team’s most prolific and well-known researchers, having disclosed critical vulnerabilities in Windows, antivirus products, password managers, and cloud infrastructure. His work has resulted in hundreds of security patches from major software vendors.
Why did Ormandy focus on auditing antivirus software?
Ormandy recognized that antivirus software occupies a uniquely dangerous position in the security stack. By design, these products intercept and parse every file that touches a system, often doing so with the highest possible privileges (kernel or SYSTEM level). This means that a vulnerability in an antivirus parser can be exploited remotely, often without user interaction, simply by sending a malformed file as an email attachment or hosting it on a web page. Ormandy’s research demonstrated that many antivirus vendors had not applied modern security engineering practices to their own code, creating a paradox where installing security software actually increased the system’s attack surface.
What was Cloudbleed and how did Ormandy discover it?
Cloudbleed was a critical memory disclosure vulnerability in Cloudflare’s edge infrastructure, discovered by Ormandy in February 2017. Cloudflare’s HTML parser had a bug that caused it to read past the end of a buffer, leaking sensitive data — including authentication tokens, API keys, and private messages — from one website’s traffic into HTTP responses served to completely unrelated websites. Ormandy noticed the anomaly while working on an unrelated project, investigated, and quickly identified the root cause. The disclosure led to an emergency response by Cloudflare and a broad credential rotation across the affected services.
How has Ormandy’s work influenced the software security industry?
Ormandy’s research has had a transformative effect on several fronts. First, it forced antivirus vendors to fundamentally rearchitect their products, moving file parsing out of the kernel and into sandboxed processes. Second, it validated the Project Zero model of independent, well-funded vulnerability research with public disclosure timelines, inspiring similar programs at other organizations. Third, it shifted industry culture toward evaluating security products by their actual security properties rather than marketing claims. His work has helped establish the expectation that all software — especially security software — should undergo rigorous independent testing and be subject to transparent vulnerability disclosure.