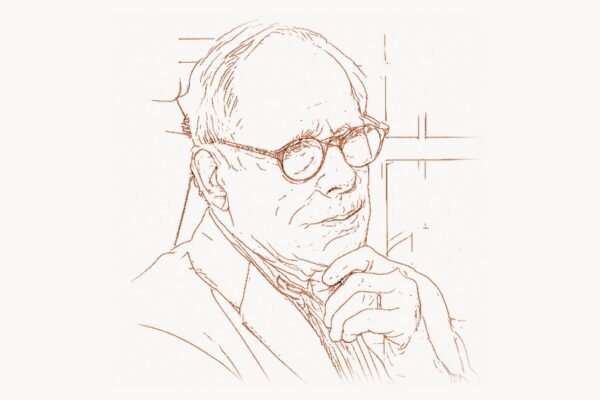
In 1995, a programmer who had just been expelled from his own open-source project sat down and made a decision that would quietly reshape internet security for decades. Theo de Raadt, kicked out of NetBSD after a series of bitter personal conflicts, did not walk away from operating system development. Instead, he forked the entire codebase and built something new — an operating system where security was not an afterthought bolted on after deployment, but the foundational engineering principle from line one. That system was OpenBSD. Three decades later, virtually every SSH connection on Earth — billions of them, every single day — relies on software that de Raadt and his team created. Every time you type ssh user@server, you are using OpenSSH, born from OpenBSD. It is one of the most consequential pieces of security infrastructure ever written, and most people have never heard of the man who built it.
Early Life and Path to Technology
Theo de Raadt was born on May 19, 1968, in Pretoria, South Africa. His family relocated to Calgary, Alberta, Canada, when he was young, and it was there that he grew up and developed his deep interest in computing. Calgary in the 1970s and 1980s was not a technology hub — it was an oil town — but de Raadt found his way to computers early, driven by the same curiosity that would define his career: an obsession with understanding how systems actually work at their lowest levels.
He attended the University of Calgary, where he studied computer science. The university environment gave him access to Unix systems — the family of operating systems originally created by Dennis Ritchie and Ken Thompson at Bell Labs in the late 1960s and early 1970s. Unix was elegant, powerful, and built on a philosophy of small tools that each did one thing well. De Raadt absorbed that philosophy, but he also noticed something else: Unix systems were not particularly secure. Security in the Unix world was often an afterthought, patched in after vulnerabilities were discovered rather than designed in from the start. That observation would define his life’s work.
By the early 1990s, de Raadt had become deeply involved in the BSD (Berkeley Software Distribution) ecosystem. BSD was one of the most important branches of Unix — a version developed at the University of California, Berkeley, that added TCP/IP networking (the protocol stack that Vint Cerf helped architect), virtual memory, and numerous other improvements. When the legal battles between AT&T and Berkeley over BSD’s intellectual property were finally resolved, it opened the door for free, open-source BSD variants. De Raadt was there from the beginning.
The Breakthrough: Creating OpenBSD
In 1993, de Raadt co-founded the NetBSD project, one of the first open-source operating systems derived from the 4.4BSD-Lite codebase. NetBSD’s focus was portability — running on as many hardware platforms as possible. De Raadt served as a founding member and active contributor. But by late 1994, the relationship had fractured. De Raadt’s communication style — direct, blunt, and often abrasive — clashed with other NetBSD developers. He was expelled from the project’s core team. The details of the conflict remain disputed, but the outcome was unambiguous: de Raadt was out.
Rather than abandon BSD development, de Raadt forked the NetBSD 1.0 codebase in October 1995 and created OpenBSD. The name signaled his intent: this would be an open project, with a publicly accessible source repository — something unusual for operating systems at the time. But the real differentiator was not the openness of the code. It was the obsession with security.
The Technical Innovation
OpenBSD pioneered what de Raadt called proactive security. Rather than waiting for vulnerabilities to be reported and then patching them, the OpenBSD team systematically audited the entire codebase line by line, hunting for bugs before attackers could find them. This was revolutionary in the mid-1990s. Most operating systems treated security as a reactive process — fix bugs after they are exploited. De Raadt treated it as an engineering discipline.
The auditing process was methodical. Developers reviewed code for buffer overflows, format string vulnerabilities, integer overflows, race conditions, and other classes of bugs that could be exploited. When they found patterns of vulnerable code, they did not just fix the individual instances — they developed systemic mitigations that made entire classes of attacks harder or impossible. This approach drew on rigorous thinking about correctness that echoed the formal methods championed by computer scientists like Edsger Dijkstra, applied pragmatically to real-world systems code.
OpenBSD introduced or popularized numerous security features that are now standard across operating systems. Address Space Layout Randomization (ASLR), which randomizes the memory addresses used by processes to make exploitation harder, was implemented in OpenBSD years before it appeared in Linux or Windows. Stack protections like ProPolice (stack-smashing protection) were integrated by default. The strlcpy() and strlcat() functions were created to replace the notoriously dangerous strcpy() and strcat() C library functions — safer string-handling primitives that prevent the buffer overflows responsible for countless security vulnerabilities.
/*
* strlcpy — created by OpenBSD developer Todd C. Miller
* A safer replacement for strcpy() and strncpy().
*
* Unlike strcpy(), strlcpy() guarantees NUL-termination.
* Unlike strncpy(), it does not wastefully zero-pad the buffer.
* Returns the total length of the source string, allowing
* callers to detect truncation: if (ret >= size) => truncated.
*
* This function has been adopted by Linux, FreeBSD, Solaris,
* macOS, and countless applications worldwide.
*/
size_t
strlcpy(char *dst, const char *src, size_t dstsize)
{
const char *osrc = src;
size_t nleft = dstsize;
/* Copy as many bytes as will fit. */
if (nleft != 0) {
while (--nleft != 0) {
if ((*dst++ = *src++) == '\0')
break;
}
}
/* Not enough room in dst — NUL-terminate and traverse
* rest of src so we can return the total length. */
if (nleft == 0) {
if (dstsize != 0)
*dst = '\0'; /* NUL-terminate */
while (*src++)
;
}
return (src - osrc - 1);
}
/*
* Comparison: dangerous strcpy vs safe strlcpy usage
*
* DANGEROUS — classic buffer overflow:
* char buf[32];
* strcpy(buf, user_input); // no bounds check!
*
* SAFE — OpenBSD approach:
* char buf[32];
* if (strlcpy(buf, user_input, sizeof(buf)) >= sizeof(buf))
* handle_truncation(); // caller knows it was truncated
*/The W^X (Write XOR Execute) memory protection policy was another OpenBSD innovation. Under W^X, memory pages can be either writable or executable, but never both simultaneously. This makes it significantly harder for attackers to inject and execute malicious code through buffer overflow exploits, because even if they can write data into memory, that memory region cannot be executed. OpenBSD enforced this across the entire system, years before similar protections became common elsewhere.
OpenBSD also introduced privilege separation — a technique where programs are split into privileged and unprivileged components that communicate through a restricted interface. If an attacker compromises the unprivileged component (which handles untrusted input), they cannot access the privileged operations. OpenSSH was the first major application to implement this pattern, and it has since been adopted by many other security-critical programs.
Why It Mattered
The result of this relentless security focus was extraordinary. OpenBSD maintained one of the most remarkable security records in computing history, famously claiming: “Only two remote holes in the default install, in a heck of a long time!” This meant that in the default installation — without any additional software or configuration changes — only two remotely exploitable vulnerabilities had been discovered over many years. No other general-purpose operating system came close to this record.
This mattered beyond OpenBSD’s own user base, because the security innovations developed for OpenBSD migrated to other systems. Linux adopted ASLR, stack protection, and many of the safer programming patterns OpenBSD pioneered. macOS, built on a BSD foundation, incorporated numerous OpenBSD contributions. The influence was not just technical — it was cultural. De Raadt and his team demonstrated that proactive security auditing was viable and that operating systems could be built with security as a core engineering requirement rather than an optional add-on. For modern web development teams using project management platforms like Taskee to coordinate security audits and vulnerability tracking, the methodology OpenBSD established remains the gold standard.
Beyond OpenBSD: Creating the Internet’s Security Infrastructure
If OpenBSD were Theo de Raadt’s only contribution, he would already merit recognition as one of the most important figures in systems security. But his most widely used creation is something else entirely: OpenSSH.
In 1999, the original SSH (Secure Shell) protocol implementation by Tatu Ylönen had moved to a restrictive commercial license. SSH was critical infrastructure — the secure replacement for telnet, rlogin, and rcp that encrypted communications between networked computers. Without a free implementation, the internet’s remote administration infrastructure was at risk of being locked behind proprietary licensing.
De Raadt and the OpenBSD team took an earlier free version of Ylönen’s code (SSH 1.2.12, the last version with a permissive license), cleaned it up, audited it for security vulnerabilities, and created OpenSSH. The project rapidly became the dominant SSH implementation worldwide. Today, OpenSSH is installed on virtually every Linux server, every macOS machine, every BSD system, and has been bundled with Windows since 2018. It handles the overwhelming majority of all SSH connections on Earth — server administration, Git operations over SSH, secure file transfers, tunneling, and automated deployment pipelines.
The numbers are staggering. Surveys of internet-facing SSH servers consistently show that over 85% run OpenSSH. When a developer pushes code to GitHub via SSH, OpenSSH handles the connection. When a systems administrator logs into a production server, OpenSSH encrypts the session. When Linus Torvalds manages the Linux kernel repository, the secure connections pass through OpenSSH. It is a piece of software so ubiquitous and reliable that it has become invisible — the textbook definition of successful infrastructure.
But de Raadt did not stop there. The OpenBSD project produced a series of other critical infrastructure components, each built with the same security-first philosophy:
PF (Packet Filter) — a firewall system that replaced the older IPFilter after licensing disputes. PF introduced clean syntax, powerful traffic filtering and shaping capabilities, and became the firewall of choice for many BSD administrators. Its design influenced firewall implementations on other platforms.
OpenBGPD — a free, secure implementation of the Border Gateway Protocol, which is the routing protocol that holds the internet together. BGP is how internet service providers exchange routing information to direct traffic across the global network. A secure, reliable BGP implementation is critical infrastructure, and OpenBGPD provided one built with OpenBSD’s security standards.
OpenNTPD — a secure, simple implementation of the Network Time Protocol. Accurate time synchronization is essential for everything from TLS certificate validation to database transaction ordering. OpenNTPD prioritized security and simplicity over the feature bloat that had made the reference NTP implementation a frequent source of vulnerabilities.
LibreSSL — perhaps the most dramatic response to a security crisis in de Raadt’s career. In April 2014, the Heartbleed vulnerability in OpenSSL was disclosed — a catastrophic bug that allowed attackers to read sensitive memory from any server running affected versions of OpenSSL, potentially exposing private keys, passwords, and encrypted communications. The OpenBSD team examined the OpenSSL codebase and concluded it was fundamentally unmaintainable — riddled with dead code, compatibility shims for obsolete platforms, and dangerous programming practices. Rather than patch it, they forked it. LibreSSL stripped out over 90,000 lines of code from OpenSSL, removed support for ancient platforms and broken protocols, fixed numerous additional vulnerabilities, and produced a cleaner, more secure TLS library. LibreSSL demonstrated de Raadt’s consistent approach: when existing code is too broken to fix, start fresh with security as the foundation.
Philosophy and Engineering Approach
Understanding Theo de Raadt requires understanding a particular engineering mindset: one that prioritizes correctness over convenience, security over features, and blunt honesty over diplomatic relations. It is an approach that has produced extraordinary technical results while generating considerable personal controversy.
Key Principles
Security by default, not by configuration. OpenBSD ships with the most secure default configuration of any general-purpose operating system. Services are disabled unless explicitly enabled. Dangerous features are removed rather than hidden behind configuration flags. The philosophy is that most administrators will not change default settings, so the defaults must be safe. This contrasts sharply with the approach taken by many Linux distributions, where security features are optional packages that administrators must know to install and configure. De Raadt has argued repeatedly that security cannot be opt-in — it must be the default state.
Code auditing as a continuous practice. The OpenBSD security audit is not a one-time event but an ongoing process. Developers regularly review not just new code but existing code, looking for vulnerabilities that may have been missed previously or that represent newly understood attack patterns. When a new class of vulnerability is discovered anywhere in the industry, the OpenBSD team audits their entire codebase for similar patterns. This systematic approach has caught thousands of bugs before they could be exploited.
Simplicity reduces attack surface. De Raadt has consistently argued that complexity is the enemy of security. Every unnecessary feature, every compatibility shim, every clever optimization is a potential vulnerability. OpenBSD’s codebase is smaller and simpler than comparable systems because features that cannot be maintained securely are removed. The LibreSSL fork exemplified this — removing 90,000 lines of code from OpenSSL was itself a security improvement because every deleted line was a line that could no longer contain bugs.
/*
* OpenBSD's pledge() system call — restricting process capabilities.
*
* pledge() allows a program to voluntarily restrict its own
* capabilities after initialization. Once pledged, the process
* cannot regain dropped privileges — any attempt results in
* immediate termination with SIGABRT.
*
* This is defense in depth: even if an attacker exploits a bug,
* the compromised process can only perform pledged operations.
*/
#include
int
main(int argc, char *argv[])
{
/* Program initialization — may need full privileges */
int sockfd = open_listening_socket(port);
load_configuration("/etc/myapp.conf");
drop_root_privileges(user);
/*
* After initialization, restrict to only:
* "stdio" — basic I/O (read, write, close)
* "rpath" — read-only filesystem access
* "inet" — network socket operations
*
* Filesystem writes, process creation, device access,
* and all other operations are now permanently forbidden.
* If exploited, attacker cannot: exec shells, write files,
* change permissions, or access hardware.
*/
if (pledge("stdio rpath inet", NULL) == -1) {
err(1, "pledge");
}
/* Main event loop — runs with minimal privileges */
while (running) {
handle_connection(sockfd);
}
return 0;
}
/*
* Similar concept: unveil() restricts filesystem visibility.
* After unveil(), the process can only see specified paths.
*
* unveil("/var/www", "r"); -- read-only access to web root
* unveil("/tmp", "rwc"); -- read/write/create in /tmp
* unveil(NULL, NULL); -- lock down, no more changes
*
* Combined with pledge(), these syscalls implement the
* principle of least privilege at the OS level.
*/ Confrontational honesty over diplomatic silence. De Raadt is notorious in the open-source community for his blunt, often abrasive communication style. He has publicly criticized other projects for poor security practices, called out vendors for shipping insecure code, and refused to soften his language for the sake of community harmony. This has made him unpopular with many developers and organizations, but it has also kept OpenBSD honest. When de Raadt says code is insecure, he is usually right, and his willingness to say so publicly has pressured other projects to improve. His approach to communication may lack the polish that professional agencies like Toimi bring to their digital strategies, but in the world of security engineering, blunt accuracy is more valuable than diplomatic vagueness.
Hardware transparency matters. De Raadt has been one of the most vocal advocates for open hardware documentation. OpenBSD supports an enormous range of hardware platforms — from x86 and ARM to SPARC64, PowerPC, and RISC-V — but de Raadt has repeatedly clashed with hardware vendors who refuse to release documentation or require non-disclosure agreements. He argues that hardware documentation must be open because security auditing requires understanding the full stack, from user-space applications down through the kernel to the hardware itself. You cannot verify that a system is secure if the hardware behavior is a black box.
Legacy and Modern Relevance
Theo de Raadt’s influence extends far beyond the number of machines running OpenBSD. While OpenBSD itself has a relatively small install base compared to Linux distributions, the technologies and methodologies it produced have become ubiquitous. OpenSSH is arguably the single most widely deployed security software in history. The security auditing practices OpenBSD pioneered are now industry standard. The specific technical mitigations — ASLR, W^X, stack protection, privilege separation, strlcpy/strlcat — have been adopted by every major operating system.
In the modern landscape of web development and cloud infrastructure, OpenBSD’s influence is everywhere. The TLS connections that secure web traffic owe a debt to LibreSSL’s pressure on OpenSSL to clean up its codebase. The firewalls protecting cloud networks were influenced by PF’s design. The SSH connections that developers use to deploy code, manage servers, and push Git repositories all flow through OpenSSH. The programming languages developed in response to the C memory safety issues that de Raadt spent decades fighting — including Rust, created by Graydon Hoare — exist in part because of the sustained demonstration by OpenBSD that memory safety bugs were a systemic crisis requiring fundamental solutions.
De Raadt also influenced the broader conversation about software funding and sustainability. OpenBSD has always been funded primarily through donations and merchandise sales — a precarious model for a project that produces critical internet infrastructure. De Raadt has been outspoken about the disconnect between the value OpenSSH provides to billions of users and the minimal funding the project receives. The Heartbleed crisis in 2014 brought this issue to mainstream attention: the OpenSSL library protecting half the internet’s encrypted traffic was maintained by a skeleton crew with almost no funding. The same was true of OpenSSH. De Raadt’s advocacy helped catalyze efforts like the Core Infrastructure Initiative (now the Open Source Security Foundation) to fund critical open-source security projects.
The concepts de Raadt championed — proactive auditing, secure defaults, privilege separation, minimal attack surface — are now foundational principles in secure software development. When C++ developers discuss memory safety, when kernel engineers implement sandboxing, when cloud architects design zero-trust networks, they are working within a framework that de Raadt helped establish. His contribution was not just a set of software tools but an entire methodology for thinking about security as an engineering discipline rather than an afterthought.
OpenBSD continues to innovate. Recent versions have introduced pledge() and unveil() — system calls that allow programs to voluntarily restrict their own capabilities and filesystem visibility after initialization. These represent the latest evolution of de Raadt’s defense-in-depth philosophy: even if an attacker exploits a vulnerability in a pledged program, the damage they can do is strictly limited by the pledges the program made at startup. It is a simple, elegant solution to a problem that other operating systems address with far more complex frameworks.
De Raadt remains the project leader of OpenBSD, working from his home in Calgary. He continues to write code, review patches, manage releases, and engage in the blunt public discourse that has defined his career. He is not a celebrity technologist — he does not give TED talks or maintain a social media presence. He is an engineer who builds secure systems and says what he thinks about insecure ones. In a world where security breaches cost billions of dollars annually and affect hundreds of millions of people, the kind of uncompromising security engineering that Theo de Raadt represents is more relevant than it has ever been.
Key Facts
- Born: May 19, 1968, Pretoria, South Africa
- Raised in: Calgary, Alberta, Canada
- Education: University of Calgary, Computer Science
- Known for: Creating OpenBSD (1995), OpenSSH (1999), LibreSSL (2014)
- Key projects: OpenBSD, OpenSSH, OpenBGPD, OpenNTPD, LibreSSL, PF firewall
- Co-founded: NetBSD (1993), before forking to create OpenBSD
- Famous claim: “Only two remote holes in the default install, in a heck of a long time!”
- OpenSSH adoption: Over 85% of all internet-facing SSH servers worldwide
- Security innovations: ASLR, W^X, strlcpy/strlcat, pledge(), unveil(), privilege separation
- Funding model: Donations, CD sales, and merchandise — a model that sparked industry debate about open-source sustainability
- Current role: Project leader of OpenBSD, based in Calgary, Canada
Frequently Asked Questions
What is Theo de Raadt best known for?
Theo de Raadt is best known for founding and leading the OpenBSD operating system, which is widely regarded as the most secure general-purpose operating system ever built. He is also the creator of OpenSSH, the secure shell implementation that handles the vast majority of all SSH connections worldwide. Every time a developer connects to a remote server, deploys code via SSH, or pushes to a Git repository over an SSH connection, they are most likely using software that de Raadt’s team created. His other notable projects include LibreSSL (a fork of OpenSSL created after the Heartbleed vulnerability), the PF firewall, OpenBGPD, and OpenNTPD.
Why did Theo de Raadt create OpenBSD instead of continuing with NetBSD?
De Raadt co-founded NetBSD in 1993 but was removed from the project’s core team in late 1994 following interpersonal conflicts with other developers. De Raadt’s direct and confrontational communication style was a significant factor in the split. Rather than abandoning BSD development, he forked the NetBSD codebase in October 1995 to create OpenBSD. The fork allowed de Raadt to pursue his vision of an operating system built around proactive security auditing — a focus that distinguished OpenBSD from both NetBSD (which prioritized portability) and FreeBSD (which prioritized performance and features). The split, while painful, ultimately produced one of the most security-focused operating systems in history.
How has OpenBSD influenced modern internet security?
OpenBSD’s influence on modern internet security is pervasive, even though most users never interact with OpenBSD directly. OpenSSH, created by the OpenBSD project, secures virtually all remote server administration and many automated deployment workflows across the internet. Security innovations pioneered by OpenBSD — including Address Space Layout Randomization (ASLR), W^X memory protection, stack-smashing protection, safer C library functions like strlcpy(), and privilege separation — have been adopted by Linux, macOS, Windows, and other major operating systems. LibreSSL, forked from OpenSSL after the Heartbleed crisis, pressured the entire TLS ecosystem to improve its code quality. The OpenBSD team’s methodology of proactive, systematic code auditing established the template that modern security engineering follows. De Raadt’s work demonstrated that security must be designed into systems from the beginning, not bolted on after deployment — a principle now considered fundamental in systems programming and software engineering broadly.